
ntpq Command in Linux
The ntpq command in Unix and Linux is a utility used to monitor NTP (Network Time Protocol) daemon ntpd operations and determine performance. Read this tutorial to get a good understanding of ntpq command and how to apply it in practice.
Table of Contents
Here is a comprehensive guide to the options available with the ntpq command −
- Overview of ntpq Command
- Syntax of ntpq Command
- ntpq Command Options
- Examples of ntpq Command in Linux
Overview of ntpq Command
The ntpq command provides a user interface for querying the ntpd daemon about its internal state, and it can also perform various control and configuration functions. The program can be executed in interactive mode or controlled using command-line arguments. It allows users to create requests for reading and writing arbitrary variables, offering both raw and formatted output options. The ntpq command can gather and display a list of peers by sending multiple queries to the server.
When ntpq is run with one or more request options included on the command line, each request is sent to the NTP servers running on the specified hosts or, by default, on localhost. If no request options are provided, ntpq attempts to read commands from the standard input and execute them on the NTP server running on the first specified host, defaulting to localhost if no host is specified. If the standard input is a terminal device, ntpq will prompt for commands.
ntpq uses NTP mode 6 packets to communicate with the NTP server, allowing it to query any compatible server on the network that permits such queries.
Since NTP relies on the UDP protocol, communication can be somewhat unreliable, particularly over large network distances. To mitigate this, ntpq makes one attempt to retransmit requests and will timeout if the remote host does not respond within an appropriate time frame.
Syntax of ntpq Command
The following is the general syntax for the ntpq command −
ntpq [options] [hostname...]
ntpq Command Options
The following table provides a breakdown of the different options available for the ntpq command, with explanations for each −
| Tag | Description |
|---|---|
| -4 | Forces DNS resolution of following host names on the command line to the IPv4 namespace. |
| -6 | Forces DNS resolution of following host names on the command line to the IPv6 namespace. |
| -c | The following argument is interpreted as an interactive format command and is added to the list of commands to be executed on the specified host. Multiple -c options may be given. |
| -d | Turns on debugging mode. |
| -k | Specify a keyfile. ntpq will look in this file for the key specified with -a. |
| -n | Outputs all host addresses in dotted-quad numeric format rather than converting to the canonical host names. |
| -p | Prints a list of the peers known to the server as well as a summary of their state. This is equivalent to the peers interactive command. |
| -w | Enable wide display of addresses/hosts on a separate line. |
| -W | Force output width to this value instead of querying the terminal size. |
| -u | Display time with units. |
| -a | Enable authentication with the numbered key |
| -l | Logs debug messages to the provided filename. |
Examples of ntpq Command in Linux
The following examples showcase the versatility of the ntpq command, allowing you to monitor and interact with NTP servers effectively −
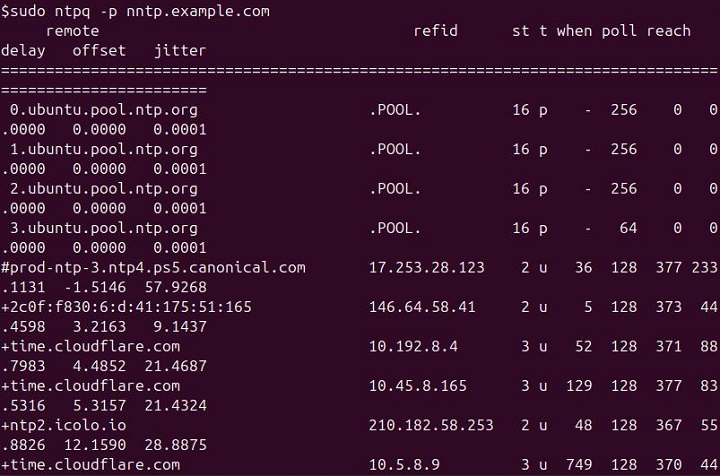
List Peers
To display a list of peers known to the server, simply run −
sudo ntpq -p nntp.example.com
This command prints a summary of the state of the peers.
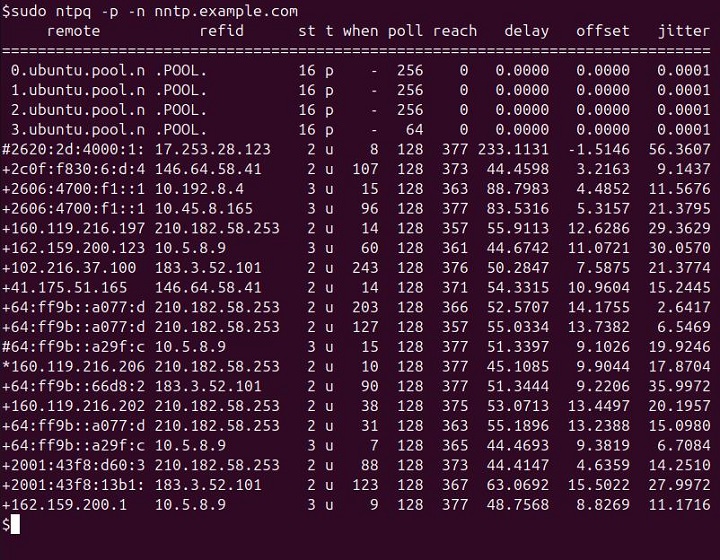
Numeric Host Addresses
To output host addresses in numeric format instead of converting them to hostnames, use the "-n" flag −
sudo ntpq -p -n nntp.example.com
This helps in avoiding DNS resolution delays.
Interactive Mode
To run ntpq in interactive mode, you can simply run the following command −
sudo ntpq
This will prompt for commands and operate similarly to a command shell.

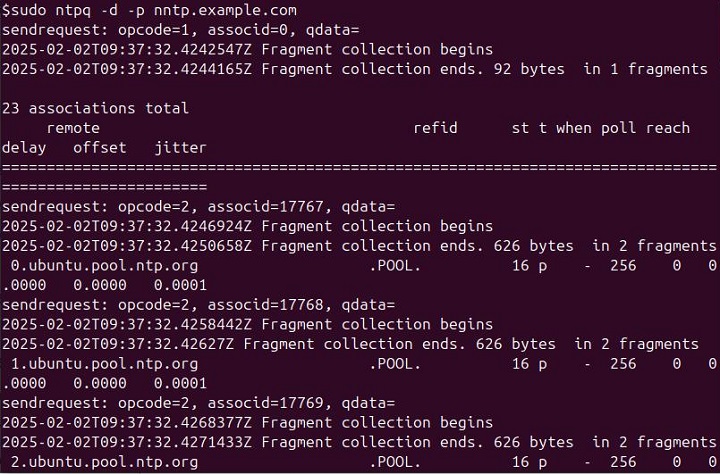
Debugging Mode
To enable debugging output, use the "-d" flag −
sudo ntpq -d -p nntp.example.com
This helps in diagnosing issues with ntpq.
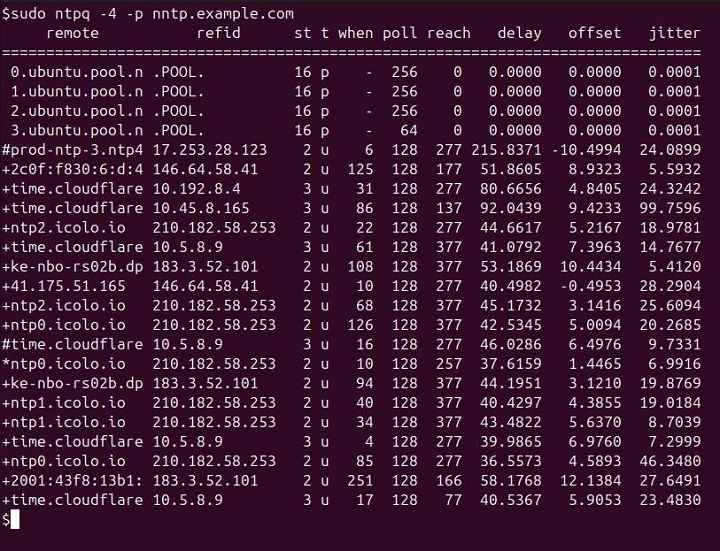
Force IPv4
To force DNS resolution of hostnames to the IPv4 namespace, use the -4 flag −
sudo ntpq -4 -p nntp.example.com
Force IPv6
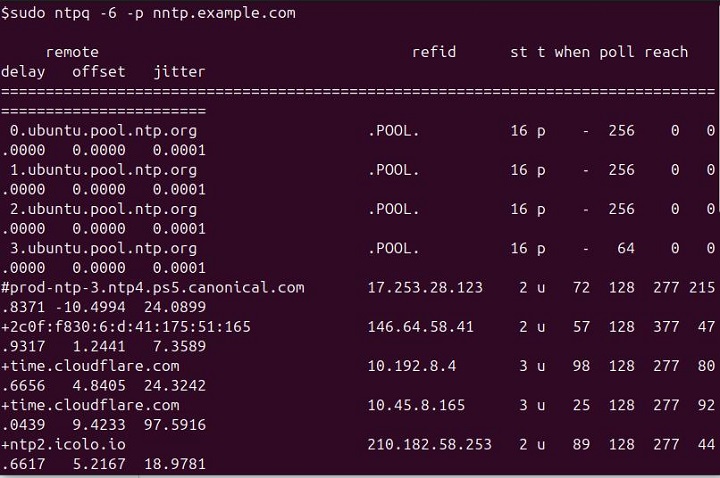
To force DNS resolution of hostnames to the IPv6 namespace, use the -6 flag −
sudo ntpq -6 nntp.example.com
Print Version
To display the version of ntpq you are using, run the following command −
sudo ntpq --version

Specifying a Command
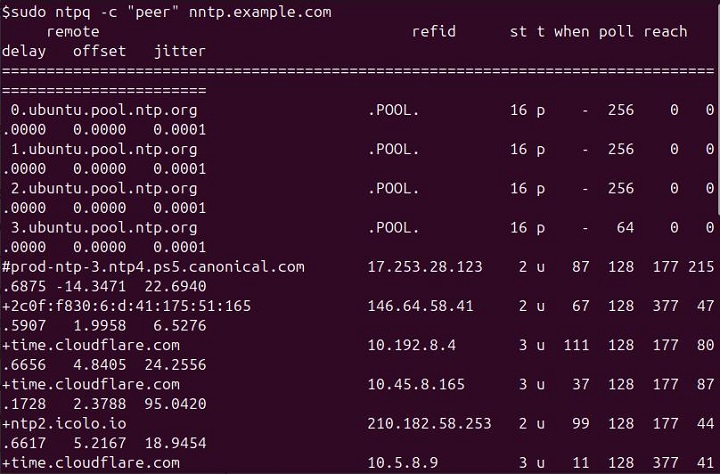
To execute a specific command, you can use the "-c" flag followed by the command −
sudo ntpq -c "peer" nntp.example.com
This sends the peer command to the nntp.example.com NTP server.
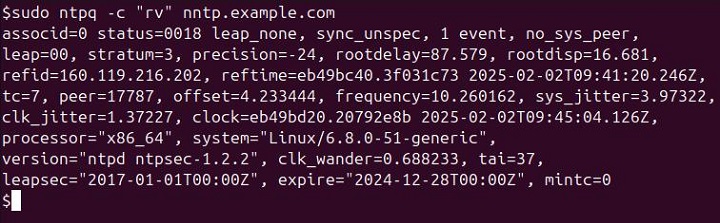
Display System Variables
To display system variables, use the following command −
sudo ntpq -c "rv" nntp.example.com
This command displays detailed system variables (like time and server status) of the specified NTP server.
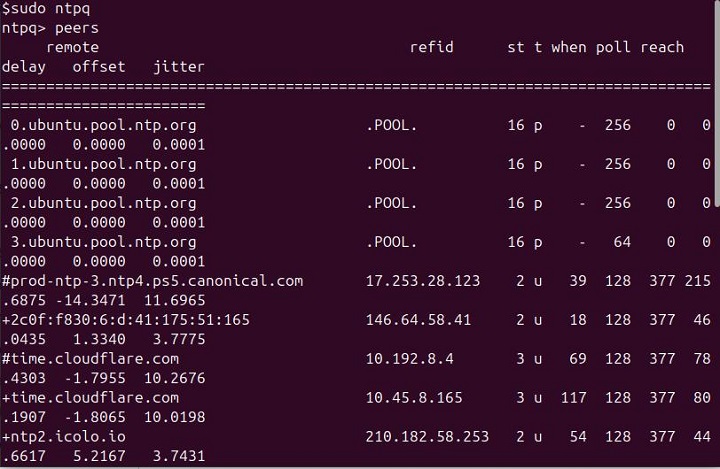
Interactive: Hostname and IP
In interactive mode, you can run the following command to display the hostname and IP of peers −
ntpq> peers
This command shows the list of peers with their hostnames and IPs.
Conclusion
The ntpq command is a powerful and versatile tool for managing and monitoring Network Time Protocol (NTP) servers on Unix and Linux systems. By providing various options, such as interactive and debugging modes, you can gain insights into server performance, peer status, and network latency.
Whether querying system variables, displaying peer information, or troubleshooting NTP issues, ntpq allows for detailed analysis and control of NTP operations. With support for IPv4 and IPv6, as well as features like time offsets and delay measurements, this command remains an essential tool for system administrators and anyone involved in network time synchronization.
