
enc Command in Linux
enc command in Linux is a port of the OpenSSL toolkit, used for encrypting and decrypting files on the system. This command supports various encryption algorithms like DES, AES and more. You can use this command to secure your data since it converts the data into an unreadable format that you can revert back using the correct key or password.
Apart from that, the enc command also allows for base64 encoding and decoding, this makes it a versatile command for different data formats. The developers most commonly use this command in scripts and automation to ensure data privacy and security.
Table of Contents
Here is a comprehensive guide to the options available with the enc command −
- Syntax for enc Command in Linux
- Different Options Available for enc Command
- Examples of enc Command in Linux
Syntax for enc Command in Linux
The basic syntax to use the enc command in Linux is provided below −
openssl enc -algorithm -in inputfile -out outputfile -pass pass:yourpassword
Here,
- algorithm specifies the encryption algorithm to use (such as aes-256-cbc).
- in inputfile is the file to be encrypted or decrypted.
- out outputfile is the file to save the encrypted or decrypted data.
- pass pass:yourpassword is the password to use for encryption or decryption.
Different Options Available for enc Command
With enc command, you can use several options of flags, these are discussed in the table given below −
| Option | Description |
|---|---|
| -a, -A, -base64 | Apply Base64 encoding before or after the cryptographic operation, you can use -A option to remove line breaks. |
| -bufsize n | Set the buffer size for internal operations, unrelated to cryptographic algorithms. |
| -debug | Enable debugging output, which does not include any sensitive information. |
| -e or -d | Encrypt (-e) or decrypt (-d). Encryption is the default. Ensure correct cipher name and options. |
| -engine id | Specify an engine, likewise a special hardware to use. |
| -in filename | Specify the input file to be processed. |
| -iv IV | Set the initialization vector (IV) as a hexadecimal number. Derived from the password if not provided. |
| -K key | Set the encryption or decryption key directly utilized by the cipher algorithm. Derived from a password if not provided. |
| -k password, -kfile filename | Specify a file or password that contains the password for key derivation. Deprecated; use -pass instead. |
| -md messagedigest | Specify the message digest algorithm for key derivation, such as md2, md5, sha, or sha1. |
| -nopad | Disable standard padding. |
| -out filename | Specify the output file that the command will create or overwrite if it already exists. |
| -p, -P | Print the key, initialization vector, and salt value if used; if -P is used, only these values are printed, and no encryption occurs. |
| -pass arg | Specify the password source and possible values are file:filename or pass:password. |
| -salt, -nosalt, -S salt | Control the use of salting. With -S salt, explicitly provide the salt value in hexadecimal. |
| -z | Enable zlib compression. After encryption (and possibly Base64 encoding), the file will be compressed using zlib. |
Examples of enc Command in Linux
Lets explore a few examples of enc command in Linux systems −
- Encrypt a File with AES-128-CBC Algorithm
- Decrypt a File with AES-128-CBC Algorithm
- Base64 Encode a File
- Base64 Decode a File
- Encrypt a File with a Specific Key and IV
- Decrypt a File with a Specific Key and IV
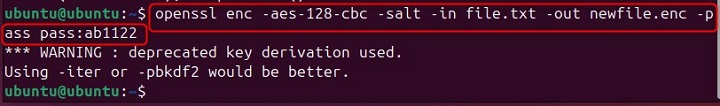
Encrypt a File with AES-128-CBC Algorithm
To encrypt a file using the AES-128-CBC algorithm with enc, you can follow the below-given example −
openssl enc -aes-128-cbc -salt -in file.txt -out newfile.enc -pass pass:ab1122
The above example will encrypt file.txt and save the encrypted data to newfile.enc using the password ab112. The -salt option will add a random salt to the encryption process, and helps enhance the security. Make sure to add the correct input file name that is present at the current location. Further, you can modify the output file name and password according to your choice.
Decrypt a File with AES-128-CBC Algorithm
To decrypt a file that was encrypted using the AES-128-CBC algorithm, you can follow the below-given command −
openssl enc -aes-128-cbc -d -in output_filename.enc -out input_filename.txt -pass pass:yourpassword
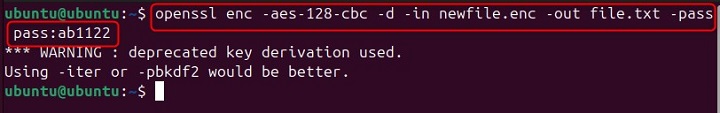
The above command will decrypt myfile.enc using the AES-128-CBC algorithm and save the decrypted data to myfile.txt. The -d option specifies decryption.
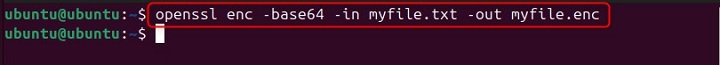
Base64 Encode a File
To encode a file in Base64, you can use the following example as a guide −
openssl enc -base64 -in myfile.txt -out myfile.enc
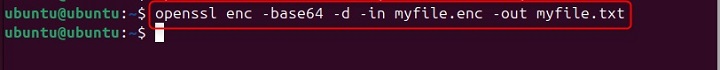
Base64 Decode a File
To decode a Base64 encoded file, you can simply follow the below-given example −
openssl enc -base64 -d -in myfile.txt -out myfile.enc
Encrypt a File with a Specific Key and IV
If you want to encrypt a file using a specific key and initialization vector (IV), you can consider the following example for guidance −
openssl enc -aes-256-cbc -K 00112233445566778899aabbccddeeff -iv 0102030405060708 -in myfile.txt -out myfile.enc
The above command will encrypt myfile.txt using the AES-256-CBC algorithm with the specified key and IV, and save the encrypted data to myfile.enc. The -K option sets the encryption key, and the -iv option sets the initialization vector.
Decrypt a File with a Specific Key and IV
For decrypting a file that was encrypted with a specific key and IV, consider the below-given example −
openssl enc -aes-256-cbc -d -K 00112233445566778899aabbccddeeff -iv 0102030405060708 -in myfile.enc -out myfile.txt
The above command will decrypt myfile.enc using the AES-256-CBC algorithm with the specified key and IV, and save the decrypted data to myfile.txt.
Conclusion
The enc command is a powerful Linux tool that is used for encrypting and decrypting files to help users ensure data privacy and security. It supports various encryption algorithms and Base64 encoding that makes it a versatile tool for different use cases. This article has provided a useful guide about enc by presenting its syntax and options that you can use with the command. In the end, examples are provided to help you understand how to use this command on Linux systems for different cases.
