
- MicroStrategy - Home
- MicroStrategy - Overview
- MicroStrategy - Environment Setup
- MicroStrategy - Desktop
- MicroStrategy - Architecture
- MicroStrategy - Importing Data
- MicroStrategy - OLAP Services
- Configuration Objects
- MicroStrategy - Public Objects
- MicroStrategy - Schema Objects
- MicroStrategy - Report Objects
- MicroStrategy Basic Reporting
- MicroStrategy - Report Types
- MicroStrategy - Slicing
- MicroStrategy - Dicing
- MicroStrategy - Pivoting
- MicroStrategy - Drilldown
- MicroStrategy - Rollup
- MicroStrategy - Creating Metrics
- MicroStrategy - Nested Metrics
- MicroStrategy Advanced Reporting
- Creating Derived Metrics
- MicroStrategy - Metric Comparison
- MicroStrategy - Creating Filters
- MicroStrategy - Advanced Filters
- Shortcut & Embedded Filters
- MicroStrategy - Refreshing Reports
- MicroStrategy - Intelligent Cubes
- MicroStrategy Dashboards
- Creating a Dashboard
- Formatting a Dashboard
- MicroStrategy - Graph Visualizations
- MicroStrategy - Grid Visualizations
- Heat Map Visualization
- MicroStrategy - N/W Visualization
- Visualization with Multiple Datasets
- Filtering Data in Dashboard
- MicroStrategy - Adding Web Content
- MicroStrategy Office
- Conditional Formatting
- MicroStrategy - Custom Groups
- MicroStrategy - Report Cache Flow
- MicroStrategy - Data Marts
- MicroStrategy - Predictive Models
- MicroStrategy Useful Resources
- MicroStrategy - Quick Guide
- MicroStrategy - Useful Resources
- MicroStrategy - Discussion
MicroStrategy - Configuration Objects
MicroStrategy objects appear in the system layer and are usable across multiple projects. Configuration objects include objects such as users, database instances, database login IDs, and schedules.
On logging in to MicroStrategy Developer, as a admin we get the Administration option under MicroStrategy Secure Enterprise. Expanding this option gives us the various configuration objects which are discussed in the following sections.
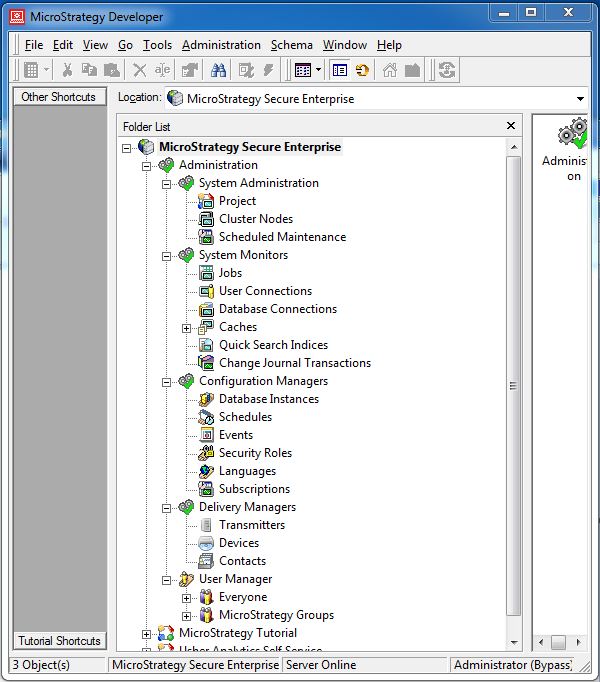
User Manager
These objects are used by the administrator to manage the MicroStrategy users. It is configured to handle the following user configurations. It offers the following configuration options −
User authentication − To allow the user into the environment.
User groups − A collection of users to whom some specific privilege is assigned.
User privileges − To use only a subset of all the features available in the environment.
User permissions − To allow/disallow the use of a specific object.
Configuration Manager
These objects are used to manage the database connectivity information. They store the path and credential information for the many databases to which MicroStrategy can connect. It offers the following configuration options −
Database instance − The name of the database instance and its credentials.
The Connection lifetime − This limit is the maximum amount of time that a database connection thread remains cached.
Events − Triggers the tasks related to a database event.
Security role − Control the access of the user to various objects in the database.
System Monitor
There are many system monitors which help in identifying the health of the MicroStrategy environment. They help in predicting the load on the system and any performance issue that is likely to arise. Following are some of the important system monitor options.
Jobs − Monitors currently executing jobs.
User Connections − Monitors the number of user connections at a given time.
Caches − Monitors the number of caches and their sizes.
System Administration
This administrative activity involves setting up various projects, allocate clusters to the projects, and schedule the maintenance windows.
