- SAP BO Data Services
- SAP BODS - Overview
- SAP BODS - Architecture
- SAP BODS - Data Services Designer
- SAP BODS Repository
- SAP BODS - Repository Overview
- Repository Creating & Updating
- Data Services Management Console
- SAP BODS - DSMC Modules
- SAP BODS - DS Designer Introduction
- SAP BODS - ETL Flow in DS Designer
- SAP BODS Datastores & Formats
- SAP BODS - Datastore Overview
- SAP BODS - Changing a Datastore
- SAP BODS - Memory Datastore
- SAP BODS - Linked Datastore
- SAP BODS - Adapter Datastore
- SAP BODS - File Formats
- COBOL Copybook File Format
- Extracting Data from DB Tables
- Data Extraction from Excel Workbook
- Data Flow & Work Flow
- SAP BODS - Dataflow Introduction
- BODS - Dataflow Changing Properties
- SAP BODS - Workflow Introduction
- SAP BODS - Creating Workflows
- SAP BODS Transforms
- SAP BODS - Transforms Types
- Adding Transform to a Dataflow
- SAP BODS - Query Transform
- SAP BODS Administration
- SAP BODS - Data Services Overview
- Creating Embedded Dataflow
- Debugging & Recovery Mechanism
- Data Assessment & Data Profiling
- SAP BODS - Tuning Techniques
- Multi-user Development
- BODS - Central vs Local Repository
- BODS - Central Repository Security
- Creating a Multi-user Environment
- SAP BODS Useful Resources
- SAP BODS - Questions Answers
- SAP BODS - Quick Guide
- SAP BODS - Useful Resources
- SAP BODS - Discussion
SAP BODS - Central Repository Security
There are various security parameters that can be applied on a central repository to make it secure.
Various security parameters are −
Authentication − This allows only authentic users to log in to the central repository.
Authorization − This allows the user to assign different level of permissions for each object.
Auditing − This is used to maintain the history of all the changes made to an object. You can check all the previous versions and revert to the older versions.
Creating Non Secure Central Repository
In a multiuser development environment, it is always advisable to work in central repository method.
To create a non-secure central repository follow the given steps −
Step 1 − Create a database, using database management system, which will act as a central repository.
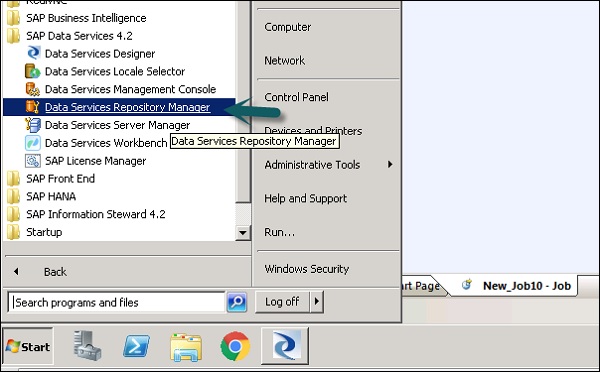
Step 2 − Go to a Repository Manager.
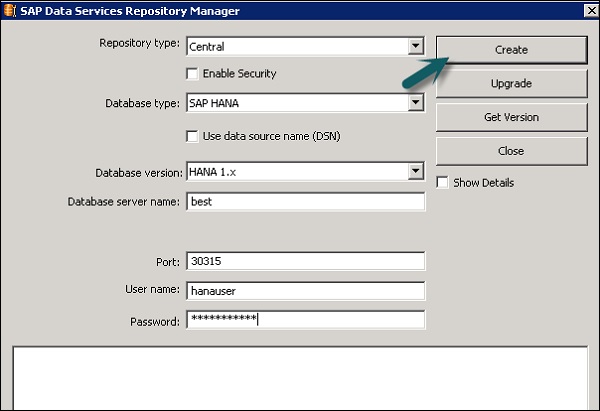
Step 3 − Select the Repository type as Central. Enter the database details such as User Name and Password and click Create.
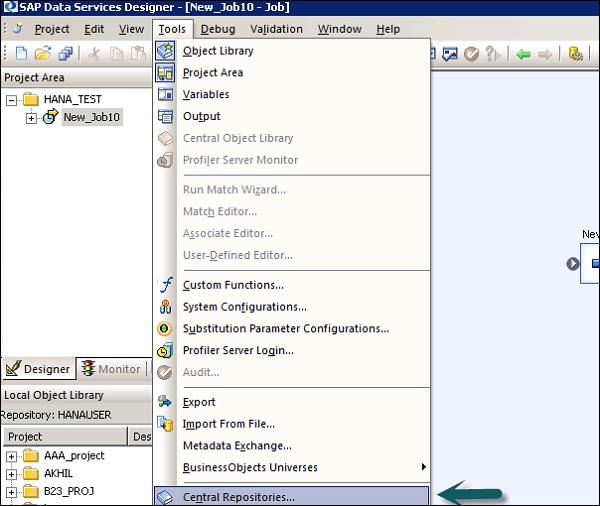
Step 4 − To define a connection to the Central Repository, Tools → Central Repository.
Step 5 − Select the Repository in Central Repository connection and click the Add icon.
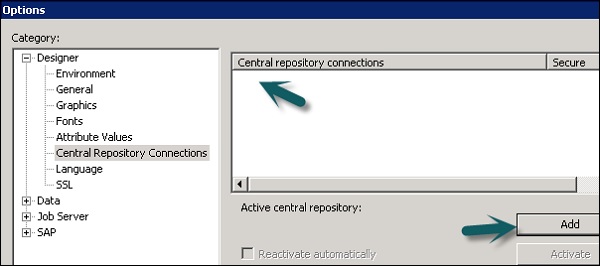
Step 6 − Enter the password for the central repository and click the Activate button.
Creating a Secure Central Repository
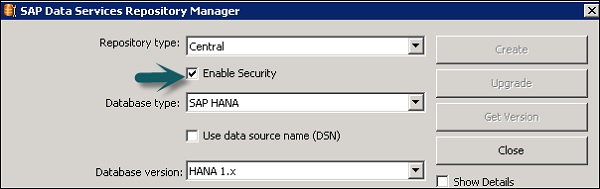
To create a secure Central Repository, go to the Repository Manager. Select the Repository Type as Central. Click the Enable Security Check box.