- Splunk - Home
- Splunk - Overview
- Splunk - Environment
- Splunk - Interfaces
- Splunk - Data Ingestion
- Splunk - Source Types
- Splunk - Basic Searching
- Splunk - Field Searching
- Splunk - Time Range Search
- Splunk - Sharing and Exporting
- Splunk - Search Language
- Splunk - Search Optimization
- Splunk - Transforming commands
- Splunk - Reports
- Splunk - Dashboards
- Splunk - Pivot & Datasets
- Splunk - Lookups
- Splunk - Schedules and Alerts
- Splunk - Knowledge Management
- Splunk - Subseraching
- Splunk - Search Macros
- Splunk - Event Types
- Splunk - Basic Chart
- Splunk - Overlay chart
- Splunk - Sparklines
- Splunk - Managing Indexes
- Splunk - Calculated Fields
- Splunk - Tags
- Splunk - Apps
- Splunk - Removing Data
- Splunk - Custom Chart
- Splunk - Monitoring Files
- Splunk - Sort Command
- Splunk - Top Command
- Splunk - Stats Command
- Splunk Useful Resources
- Splunk - Quick Guide
- Splunk - Useful Resources
- Splunk - Discussion
Splunk - Schedules and Alerts
Scheduling is the process of setting up a trigger to run the report automatically without the users intervention. Below are the uses of scheduling a report −
By running the same report at different intervals: monthly, weekly or daily, we can get results for that specific period.
Improved performance of the dashboard as the reports finish running in the background before the dashboard is opened by the users.
Sending of reports automatically via email after it finishes running.
Creating a Schedule
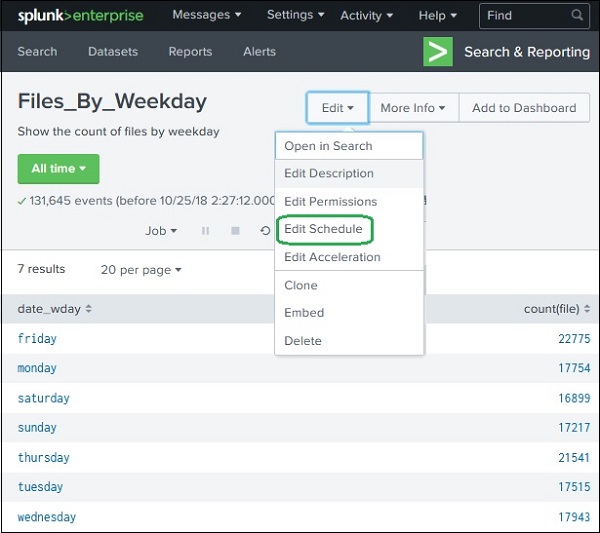
A schedule is created by editing the reports schedule feature. We go to the Edit Schedule option on the Edit button as shown in the image below.
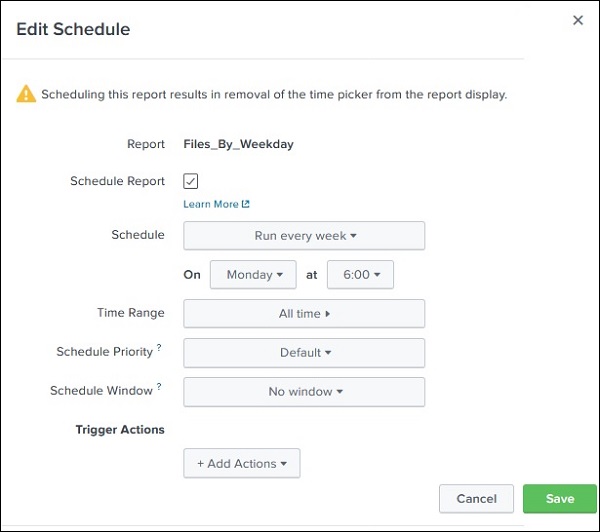
On clicking the edit schedule button, we get the next screen which lays out all the options for creating the schedule.
In the below example, we take all the default options and the report is scheduled to run every week on Monday at 6 AM.
Important Features of Scheduling
The following are the important features of scheduling −
Time Range − It indicates the time range from which the report must fetch the data. It can be last 15 minutes, last 4 hours or last week etc.
Schedule Priority − If more than one report is scheduled at the same time then this will determine the priority of a specific report.
Schedule Window − When there are multiple report schedules with same priority then we can choose a time window which will help the report to run at anytime during this window. If it is 5 minutes, then the report will run within 5 minutes of its scheduled time. This helps in enhancing the performance of the scheduled reports by spreading their run time.
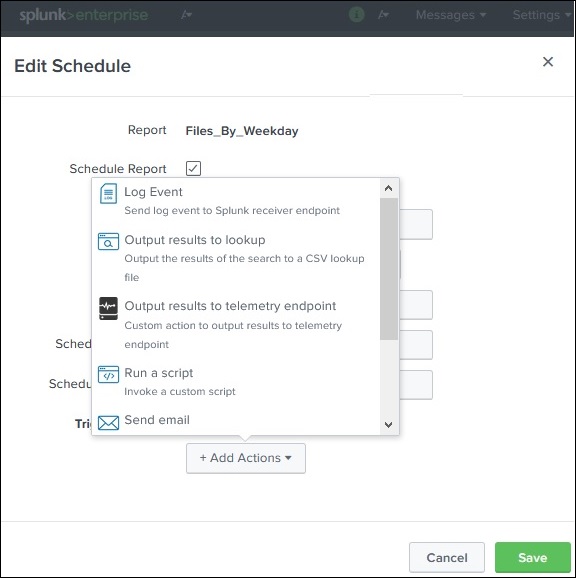
Schedule Actions
The schedule actions are meant to take some steps after the report is run. For example, you may want to send an email stating the run status of the report or run another script. Such actions can be carried out by setting the option by clicking on Add Actions button as shown below −
Alerts
Splunk alerts are actions which get triggered when a specific criterion is met which is defined by the user. The goal of alerts can be logging an action, sending an email or output a result to a lookup file, etc.
Creating an Alert
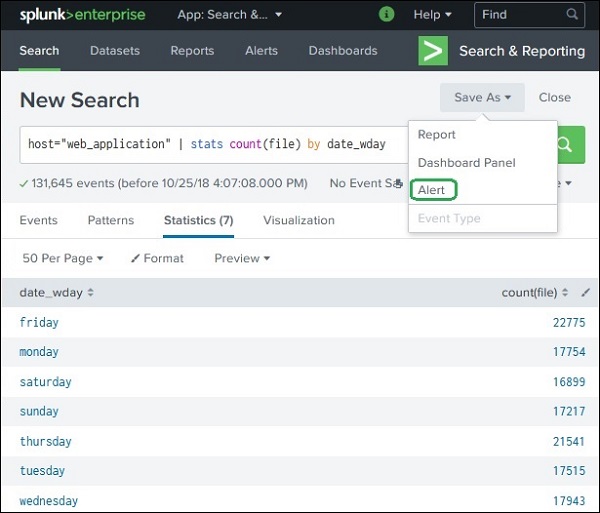
You create an alert by running a search query and saving its result as an alert. In the below screenshot, we take the search for daywise file count and save the result as an alert by choosing the Save As option.
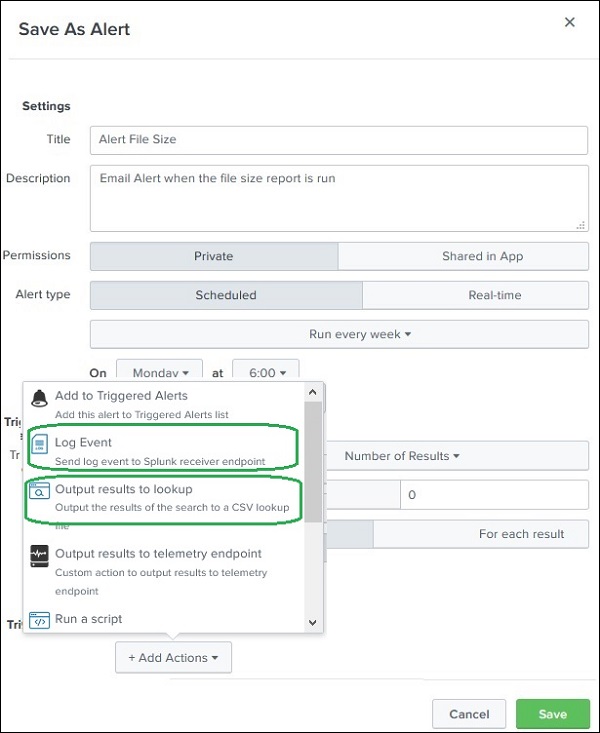
In the next screenshot, we configure the alert properties. The below image shows the configuration screen −
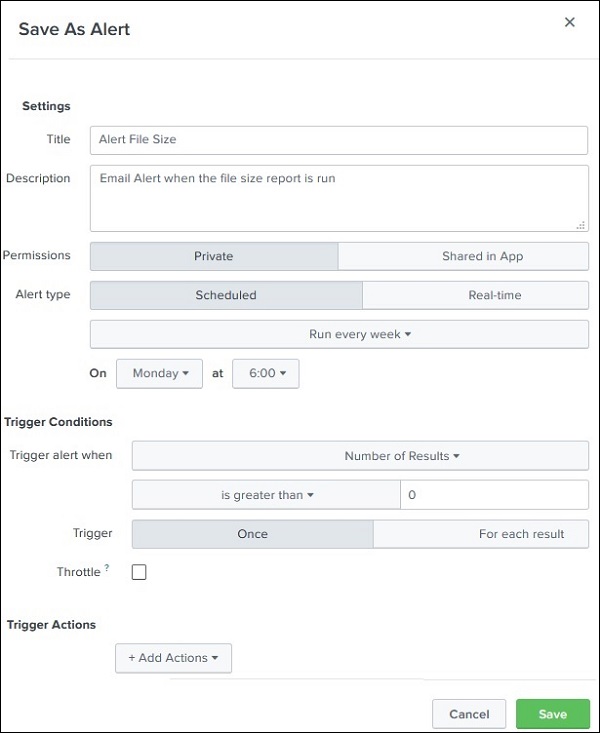
The purpose and choices of each of these options is explained below −
Title − It is the name of the alert.
Description − It is the detailed description of what the alert does.
Permission − Its value decided who can access, run or edit the alert. If declared private, then only the creator of the alert has all the permissions. To be accessed by others the option should be changed to Shared in App. In this case everyone has read access but only power user has the edit access for the alert.
Alert Type − A scheduled alert runs at a pre-defined interval whose run time is defined by the day and time chosen from the drop downs. But the other option on real-time alert causes the search to run continuously in the background. Whenever the condition is met, the alert action is executed.
Trigger condition − The trigger condition checks for the criteria mentioned in the trigger and sets off the alter only when the alert criteria is met. You can define number of results or number of sources or number of hosts in the search result to trigger the alert. If it is set for once, it will execute only once when the result condition is met but if it is set to For each Result, then it will run for every row in the result set where the trigger condition is met.
Trigger Actions − The trigger actions can give a desired output or send an email when the trigger condition is met. The below image shows some of the important trigger actions available in Splunk.