- Metasploit - Home
- Metasploit - Introduction
- Metasploit - Environment Setup
- Metasploit - Basic Commands
- Metasploit - Armitage GUI
- Metasploit - Pro Console
- Metasploit - Vulnerable Target
- Metasploit - Discovery Scans
- Metasploit - Task Chains
- Metasploit - Import Data
- Metasploit - Vulnerability Scan
- Metasploit - Vulnerability Validation
- Metasploit - Exploit
- Metasploit - Payload
- Metasploit - Credential
- Metasploit - Brute-Force Attacks
- Metasploit - Pivoting
- Metasploit - Maintaining Access
- Metasploit - MetaModules
- Metasploit - Social Engineering
- Metasploit - Export Data
- Metasploit - Reports
Metasploit - Basic Commands
In this chapter, we will discuss some basic commands that are frequently used in Metasploit.
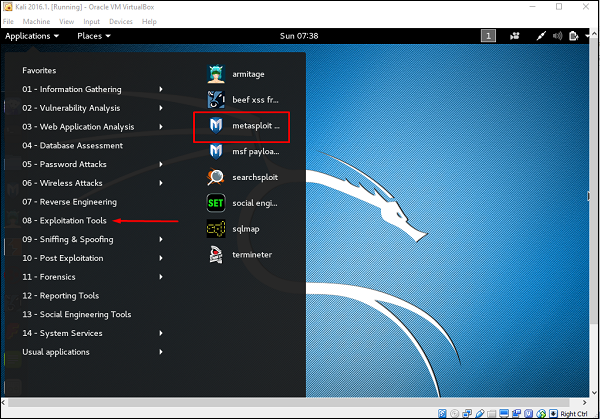
First of all, open the Metasploit console in Kali. You can do so by following the path: Applications → Exploitation Tools → Metasploit.
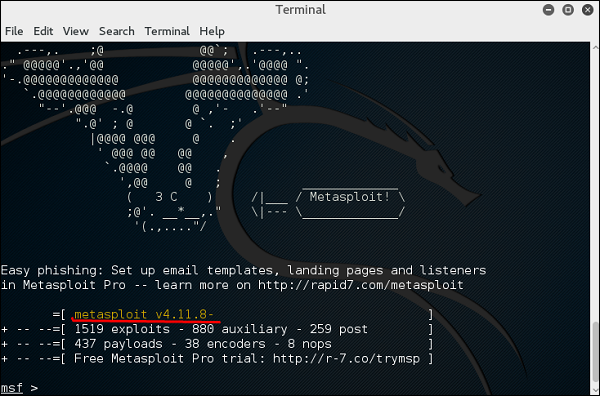
Once you open the Metasploit console, you will get to see the following screen. Highlighted in red underline is the version of Metasploit.
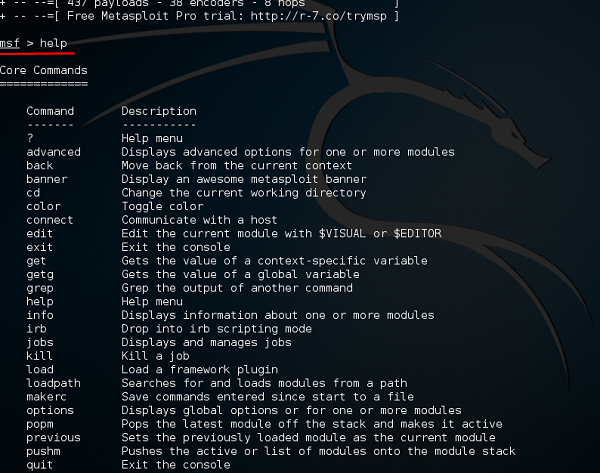
Help Command
If you type the help command on the console, it will show you a list of core commands in Metasploit along with their description.
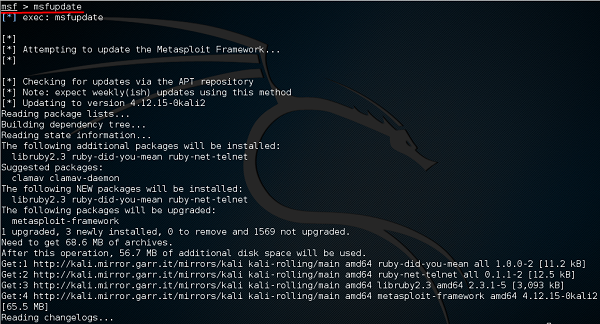
msfupdate Command
msfupdate is an important administration command. It is used to update Metasploit with the latest vulnerability exploits. After running this command, you will have to wait several minutes until the update completes.
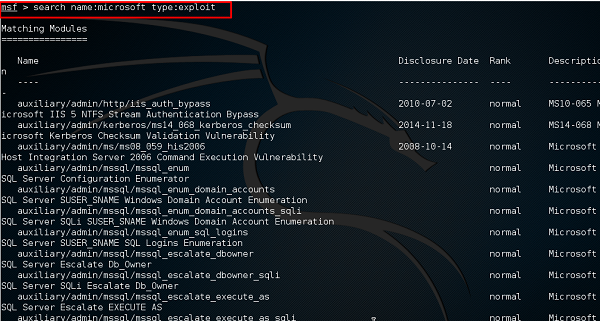
Search Command
Search is a powerful command in Metasploit that you can use to find what you want to locate. For example, if you want to find exploits related to Microsoft, then the command will be −
msf >search name:Microsoft type:exploit
Here, search is the command, name is the name of the object that you are looking for, and type is the kind of script you are searching.
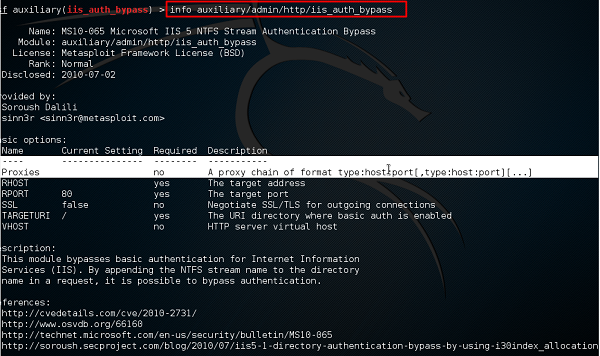
Info Command
The info command provides information regarding a module or platform, such as where it is used, who is the author, vulnerability reference, and its payload restriction.