
- Electrical Machines - Home
- Basic Concepts
- Electromechanical Energy Conversion
- Energy Stored in Magnetic Field
- Singly-Excited and Doubly Excited Systems
- Rotating Electrical Machines
- Electrical Machines Types
- Faraday’s Laws of Electromagnetic Induction
- Concept of Induced EMF
- Fleming's Left Hand and Right Hand Rules
- Transformers
- Electrical Transformer
- Construction of Transformer
- EMF Equation of Transformer
- Turns Ratio and Voltage Transformation Ratio
- Ideal Transformer
- Practical Transformer
- Ideal and Practical Transformers
- Transformer on DC
- Losses in a Transformer
- Efficiency of Transformer
- 3-Phase Transformer
- Types of Transformers
- More on Transformers
- Transformer Working Principle
- Single-Phase Transformer Working Principle
- 3-Phase Transformer Principle
- 3-Phase Induction Motor Torque-Slip
- 3-Phase Induction Motor Torque-Speed
- 3-Phase Transformer Harmonics
- Double-Star Connection (3-6 Phase)
- Double-delta Connection (3-6 Phase)
- Transformer Ratios
- Voltage Regulation
- Delta-Star Connection (3-Phase)
- Star-Delta Connection (3-Phase)
- Autotransformer Conversion
- Back-to-back Test (Sumpner's Test)
- Transformer Voltage Drop
- Autotransformer Output
- Open and Short Circuit Test
- 3-Phase Autotransformer
- Star-Star Connection
- 6-Phase Diametrical Connections
- Circuit Test (Three-Winding)
- Potential Transformer
- Transformers Parallel Operation
- Open Delta (V-V) Connection
- Autotransformer
- Current Transformer
- No-Load Current Wave
- Transformer Inrush Current
- Transformer Vector Groups
- 3 to 12-Phase Transformers
- Scott-T Transformer Connection
- Transformer kVA Rating
- Three-Winding Transformer
- Delta-Delta Connection Transformer
- Transformer DC Supply Issue
- Equivalent Circuit Transformer
- Simplified Equivalent Circuit of Transformer
- Transformer No-Load Condition
- Transformer Load Condition
- OTI WTI Transformer
- CVT Transformer
- Isolation vs Regular Transformer
- Dry vs Oil-Filled
- DC Machines
- Construction of DC Machines
- Types of DC Machines
- Working Principle of DC Generator
- EMF Equation of DC Generator
- Derivation of EMF Equation DC Generator
- Types of DC Generators
- Working Principle of DC Motor
- Back EMF in DC Motor
- Types of DC Motors
- Losses in DC Machines
- Applications of DC Machines
- More on DC Machines
- DC Generator
- DC Generator Armature Reaction
- DC Generator Commutator Action
- Stepper vs DC Motors
- DC Shunt Generators Critical Resistance
- DC Machines Commutation
- DC Motor Characteristics
- Synchronous Generator Working Principle
- DC Generator Characteristics
- DC Generator Demagnetizing & Cross-Magnetizing
- DC Motor Voltage & Power Equations
- DC Generator Efficiency
- Electric Breaking of DC Motors
- DC Motor Efficiency
- Four Quadrant Operation of DC Motors
- Open Circuit Characteristics of DC Generators
- Voltage Build-Up in Self-Excited DC Generators
- Types of Armature Winding in DC Machines
- Torque in DC Motors
- Swinburne’s Test of DC Machine
- Speed Control of DC Shunt Motor
- Speed Control of DC Series Motor
- DC Motor of Speed Regulation
- Hopkinson's Test
- Permanent Magnet DC Motor
- Permanent Magnet Stepper Motor
- DC Servo Motor Theory
- DC Series vs Shunt Motor
- BLDC Motor vs PMSM Motor
- Induction Motors
- Introduction to Induction Motor
- Single-Phase Induction Motor
- 3-Phase Induction Motor
- Construction of 3-Phase Induction Motor
- 3-Phase Induction Motor on Load
- Characteristics of 3-Phase Induction Motor
- Speed Regulation and Speed Control
- Methods of Starting 3-Phase Induction Motors
- More on Induction Motors
- 3-Phase Induction Motor Working Principle
- 3-Phase Induction Motor Rotor Parameters
- Double Cage Induction Motor Equivalent Circuit
- Induction Motor Equivalent Circuit Models
- Slip Ring vs Squirrel Cage Induction Motors
- Single-Cage vs Double-Cage Induction Motor
- Induction Motor Equivalent Circuits
- Induction Motor Crawling & Cogging
- Induction Motor Blocked Rotor Test
- Induction Motor Circle Diagram
- 3-Phase Induction Motors Applications
- 3-Phase Induction Motors Torque Ratios
- Induction Motors Power Flow Diagram & Losses
- Determining Induction Motor Efficiency
- Induction Motor Speed Control by Pole-Amplitude Modulation
- Induction Motor Inverted or Rotor Fed
- High Torque Cage Motors
- Double-Cage Induction Motor Torque-Slip Characteristics
- 3-Phase Induction Motors Starting Torque
- 3-phase Induction Motor - Rotor Resistance Starter
- 3-phase Induction Motor Running Torque
- 3-Phase Induction Motor - Rotating Magnetic Field
- Isolated Induction Generator
- Capacitor-Start Induction Motor
- Capacitor-Start Capacitor-Run Induction Motor
- Winding EMFs in 3-Phase Induction Motors
- Split-Phase Induction Motor
- Shaded Pole Induction Motor
- Repulsion-Start Induction-Run Motor
- Repulsion Induction Motor
- PSC Induction Motor
- Single-Phase Induction Motor Performance Analysis
- Linear Induction Motor
- Single-Phase Induction Motor Testing
- 3-Phase Induction Motor Fault Types
- Synchronous Machines
- Introduction to 3-Phase Synchronous Machines
- Construction of Synchronous Machine
- Working of 3-Phase Alternator
- Armature Reaction in Synchronous Machines
- Output Power of 3-Phase Alternator
- Losses and Efficiency of an Alternator
- Losses and Efficiency of 3-Phase Alternator
- Working of 3-Phase Synchronous Motor
- Equivalent Circuit and Power Factor of Synchronous Motor
- Power Developed by Synchronous Motor
- More on Synchronous Machines
- AC Motor Types
- Induction Generator (Asynchronous Generator)
- Synchronous Speed Slip of 3-Phase Induction Motor
- Armature Reaction in Alternator at Leading Power Factor
- Armature Reaction in Alternator at Lagging Power Factor
- Stationary Armature vs Rotating Field Alternator Advantages
- Synchronous Impedance Method for Voltage Regulation
- Saturated & Unsaturated Synchronous Reactance
- Synchronous Reactance & Impedance
- Significance of Short Circuit Ratio in Alternator
- Hunting Effect Alternator
- Hydrogen Cooling in Synchronous Generators
- Excitation System of Synchronous Machine
- Equivalent Circuit Phasor Diagram of Synchronous Generator
- EMF Equation of Synchronous Generator
- Cooling Methods for Synchronous Generators
- Assumptions in Synchronous Impedance Method
- Armature Reaction at Unity Power Factor
- Voltage Regulation of Alternator
- Synchronous Generator with Infinite Bus Operation
- Zero Power Factor of Synchronous Generator
- Short Circuit Ratio Calculation of Synchronous Machines
- Speed-Frequency Relationship in Alternator
- Pitch Factor in Alternator
- Max Reactive Power in Synchronous Generators
- Power Flow Equations for Synchronous Generator
- Potier Triangle for Voltage Regulation in Alternators
- Parallel Operation of Alternators
- Load Sharing in Parallel Alternators
- Slip Test on Synchronous Machine
- Constant Flux Linkage Theorem
- Blondel's Two Reaction Theory
- Synchronous Machine Oscillations
- Ampere Turn Method for Voltage Regulation
- Salient Pole Synchronous Machine Theory
- Synchronization by Synchroscope
- Synchronization by Synchronizing Lamp Method
- Sudden Short Circuit in 3-Phase Alternator
- Short Circuit Transient in Synchronous Machines
- Power-Angle of Salient Pole Machines
- Prime-Mover Governor Characteristics
- Power Input of Synchronous Generator
- Power Output of Synchronous Generator
- Power Developed by Salient Pole Motor
- Phasor Diagrams of Cylindrical Rotor Moto
- Synchronous Motor Excitation Voltage Determination
- Hunting Synchronous Motor
- Self-Starting Synchronous Motor
- Unidirectional Torque Production in Synchronous Motor
- Effect of Load Change on Synchronous Motor
- Field Excitation Effect on Synchronous Motor
- Output Power of Synchronous Motor
- Input Power of Synchronous Motor
- V Curves & Inverted V Curves of Synchronous Motor
- Torque in Synchronous Motor
- Construction of 3-Phase Synchronous Motor
- Synchronous Motor
- Synchronous Condenser
- Power Flow in Synchronous Motor
- Types of Faults in Alternator
- Miscellaneous Topics
- Electrical Generator
- Determining Electric Motor Load
- Solid State Motor Starters
- Characteristics of Single-Phase Motor
- Types of AC Generators
- Three-Point Starter
- Four-Point Starter
- Ward Leonard Speed Control Method
- Pole Changing Method
- Stator Voltage Control Method
- DOL Starter
- Star-Delta Starter
- Hysteresis Motor
- 2-Phase & 3-Phase AC Servo Motors
- Repulsion Motor
- Reluctance Motor
- Stepper Motor
- PCB Motor
- Single-Stack Variable Reluctance Stepper Motor
- Schrage Motor
- Hybrid Schrage Motor
- Multi-Stack Variable Reluctance Stepper Motor
- Universal Motor
- Step Angle in Stepper Motor
- Stepper Motor Torque-Pulse Rate Characteristics
- Distribution Factor
- Electrical Machines Basic Terms
- Synchronizing Torque Coefficient
- Synchronizing Power Coefficient
- Metadyne
- Motor Soft Starter
- CVT vs PT
- Metering CT vs Protection CT
- Stator and Rotor in Electrical Machines
- Electric Motor Winding
- Electric Motor
- Useful Resources
- Quick Guide
- Resources
- Discussion
What is a Three Winding Transformer?
The transformers may also be constructed with a third winding in addition to the primary and secondary windings. This third winding is known as tertiary winding. The primary winding has the highest voltage rating, the tertiary winding has the lowest voltage rating and the secondary winding has the intermediate voltage rating. Also, the kVA ratings of the three windings of the 3-winding transformer are usually unequal. The figure shows the schematic diagram of a 3-winding transformer.
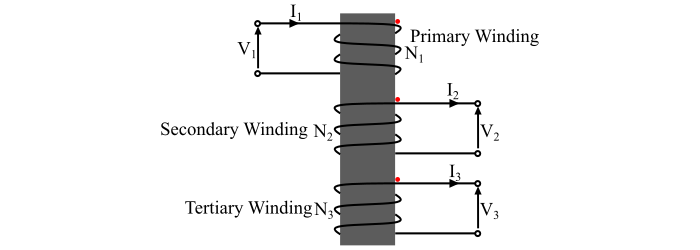
The tertiary winding is always connected in delta. The primary advantage of the delta connected tertiary winding is that it suppresses any harmonic components that may be generated in the star connected primary and secondary windings of the transformer.
In case of unbalanced load currents in the secondary winding, which are reflected as unbalanced primary currents, an increased circulating current is reduced in the tertiary windings. This tends to restore the primary and secondary phase voltages to their normal magnitudes and phase angles. Therefore, the tertiary winding also reduces the secondary and primary imbalance and distributes the secondary load imbalance evenly among the primary phases.
Working Principle of Tertiary Winding of the Transformer
The principle uses of the tertiary winding of the transformer are given as follows −
- The tertiary windings are used as auxiliary winding for supplying the substation uses (e.g., lighting, fan, pumps, etc.).
- Tertiary windings are used to interconnect three supply systems operating at different voltage levels.
- Tertiary windings can be used for measuring voltage of high voltage testing transformers.
- The tertiary windings may also be used for supplying a single load from two source, where the continuity of supply is important.
- Since the tertiary winding is connected in delta, thus it reduces the impedance offered to the zero-sequence currents to allow sufficient earth fault current for proper operation of protective devices.
- The synchronous condenser or static high voltage capacitors are connected across the delta connected output of the tertiary windings for reactive power injection into the power system for either power factor correction or voltage regulation or both.
The main advantages of a three winding transformer are greater efficiency and economical construction.
Voltage Ratios and MMF Balance Equation
For an ideal three winding transformer, the voltage ratios are defined as follows −
$$\mathrm{\frac{_{2}}{_{1}}=\frac{_{2}}{_{1}}}$$
Where,
- V1 = Primary voltage,
- V2 = Secondary voltage,
- N1 = Number of turns in primary winding, and
- N2 = Number of turns in secondary winding.
Similarly, the voltage transformation ratio between primary and tertiary winding is
$$\mathrm{\frac{V_{3}}{V_{1}} \: = \: \frac{N_{3}}{N_{1}}}$$
Where,
- V3 is voltage across tertiary winding, and
- N3 is number of turns in tertiary winding.
Also, the total MMF of the primary winding is equal to the sum of MMF required by the secondary winding and MMF required by the tertiary winding, i.e.,
$$\mathrm{N_{1}I_{1} \:=\: N_{2}I_{2} \:+\: N_{3}I_{3}}$$
This expression is the MMF balance equation of a three winding transformer.
Equivalent Circuit of Three Winding Transformer
The equivalent circuit of the 3-winding transformer is shown in the figure. The equivalent circuit of a 3-winding transformer can be represented by the 1-phase equivalent circuit, in which each winding of the transformer can be represented by its equivalent resistance and reactance.
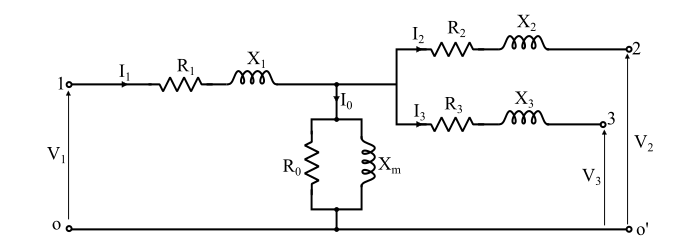
Here, the terminals 1, 2, 3 indicate primary, secondary and tertiary winding terminals respectively. The resistances R1, R2 and R3 are the resistances of primary, secondary and tertiary windings respectively. The reactances X1, X2 and X3 are the leakage reactances of the primary, secondary and tertiary windings respectively. If the no-load current is also considered, then the core loss resistance R0 and magnetising reactance Xm are also connected.
