
- Computer - Home
- Computer - Overview
- Computer - Advantages & Disadvantages
- Computer - Classification
- Computer - Applications
- Computer - History & Evolution
- Computer - System Characteristics
- Computing Origins
- Computer - Origins
- Computer - Generations
- Computer - Types
- Computer Components
- Computer - Components
- Computer - CPU
- Computer - CPU Components
- Computer - Arithmetic Logic Unit (ALU)
- Computer - Control Unit
- Computer - Input Devices
- Computer - Output Devices
- Computer - Memory Units
- Computer Hardware
- Computer - Hardware
- Computer - Motherboard
- Computer - GPU
- Computer - PSU
- Computer Software
- Computer - Software
- Computer - Software Types
- Computer Data Storage & Memory
- Computer - Data Storage
- Computer - Types of Data Storage
- Computer - Hard Disk Drives (HDD)
- Computer - Solid State Drives (SSD)
- Computer - Memory Cards
- Computer - Optical Storage
- Computer - NAND Flash Memory
- Computer - NVMe Memory
- Computer - CompactFlash Card
- Computer - Cloud Storage
- Computer Memory
- Computer - Memory
- Computer - Primary Memory
- Computer - Secondary Memory
- Computer - RAM
- Computer - ROM
- Computer - DRAM
- Computer - VRAM
- Computer - Cache Memory
- Computer Internet & Intranet
- Computer - Internet and Intranet
- Computer - Internet
- Computer - Extranet
- Computer - Websites
- Computer Office Tools
- Computer - Word Processors
- Computer - Spread Sheet
- Computer - Power Presentations
- Computer - E-mail Tools
- Computer Miscellaneous
- Computer - Ports
- Computer - Number System
- Computer - Number Conversion
- Computer - Data and Information
- Computer - Networking
- Computer - Operating System
- Computer - Keyboard Shortcut Keys
- Computer - Virus
- Computer - Antivirus
- Computer - How to Buy?
- Computer - Available Courses
- Calculator Vs. Computer
- Brain Vs. Computer
- Analog Vs. Digital Computer
- Supercomputer Vs. Mainframe Computer
- Mainframe Vs. Minicomputer
- Printer Vs. Scanner
- OCR Vs. MICR
- File Vs. Folder
- exFAT Vs. FAT32
- FAT32 Vs. NTFS
- FAT32 Vs. exFAT Vs. NTFS
- CPU Vs. GPU
- GUI Vs. CLI
- GUI Vs. CUI
- Cache Memory Vs. Virtual Memory
- Register Vs. Memory
- RAM Vs. CAM
- SRAM Vs. DRAM
- DDR2 Vs. DDR3
- PROM Vs. EPROM
- CD Vs. DVD
- Blu-Ray Vs. DVD
- MMU Vs. MPU
- Computer Terminologies
- Microsoft Windows
- Desktop
- Monitor
- Microphone
- Keyboard
- Keypad
- Mouse
- Printer
- Webcam
- Floppy Disk Drive
- Compact Disc
- Program
- Incognito Mode
- Electronic Mail (E-Mail)
- Server
- Cloud Hosting
- Minicomputers
- Supercomputer
- Bit
- Byte
- Kilobyte
- Megabyte
- Terabyte
- Yottabyte
- Zettabyte
- Exabyte
- Petabyte
- JEDEC
- Hub
- Block Storage
- Username
- URL
- Num Lock
- BIOS
- Bluetooth
- Computer Useful Resources
- Computer - Quick Guide
- Keyboard Function Keys
- Keyboard Shortcuts for Ubuntu
- Computer - Useful Resources
- Computer - Discussion
Computer - Memory
What is Computer Memory?
A physical device that stores data or information temporarily or permanently in it is called memory. Its a device where data is stored and processed. In common, a computer has primary and secondary memories. Auxiliary (secondary) memory stores data and programs for long-term storage or until the time a user wants to keep them in memory, while main memory stores instructions and data during programme execution; hence, any programme or file that is currently running or executing on a computer is stored in primary memory.
Types of Computer Memory
Computer memory comes in various types and serves different purposes −
- Primary Memory (RAM - Random Access Memory) − Volatile memory loses its contents when the machine is turned off. RAM stores the data that is actively being used. During the booting process of a system, the operating system actively uses RAM and applications that are necessary to execute a file or a program. It speeds up CPU processing by providing fast data and instruction access.
- Secondary Memory (Storage) − Secondary Memory is also known as permanent memory or non-volatile memory of a computer. Secondary memory retains data when the machine shuts down. Files, programmes, and the OS are stored there permanently. HDDs, SSDs, USB flash drives, and optical discs are non-volatile memory devices.
- Cache Memory − Memory that is smaller and faster than RAM is called cache memory. It is placed closer to the CPU than the RAM. It saves data and instructions that are used a lot so that processing goes faster.
- Register Memory − Register memory, which is also called processor registers or "registers," is the smallest and fastest type of computer memory that is directly integrated into the CPU. Registers are small, fast storage units inside the CPU that are used to quickly store data that is being processed or instructions that are being run.
Primary Memory
Computer primary memory is also known as volatile memory, as it loses contents when the machine is turned off. There are two types of primary memory: RAM and ROM. RAM stores the data that is actively being used. During the booting process of a system, the operating system actively uses RAM and applications that are necessary to execute a file or a program. It speeds up CPU processing by providing rapid data and instruction access.
Here is the classification of primary memory:
- RAM (Random Access Memory)
- SRAM (Static RAM)
- DRAM (Dynamic RAM)
- SDRAM (Synchronous DRAM)
- DDR (Double Data Rate) RAM
- ROM (Read-Only Memory)
- PROM (Programmable ROM)
- EPROM (Erasable Programmable ROM)
- EEPROM (Electrically Erasable Programmable ROM)
- Flash ROM
1. Random Access Memory (RAM)
RAM contains of a various number of memory locations wherein each location, typically 8-bits are stored. It can be possible to read from a RAM location, as well as write to a RAM location. The drawback of RAM is that it is volatile. That means, when the power supply to the RAM is switched off, the information in the RAM will be lost.
From the memory, data can be accessed in two different ways – SequentialAccess and Random Access.
Sequential Access − Sequential access and random access are two types of accessing information. In sequential access, it is mandatory to access information strictly in order. If there are 4000 memory locations, it have to be accessed in the order of 1, 2, 3,…,4000. Thus, it takes minimum time to access information from location 0 and at most time to access information from location 4000. Magnetic tape is an example that employs sequential access.
Random Access − In a random access technique, it can be possible to access a memory location in any order. For example, one can read from the 4000 locations in the order of 1500, 1210, 3060, 1640, 1352, and so on. Second, it takes a similar time to read from a memory location irrespective of its position. In a RAM, the access method is random, and its name, in fact, is derived based on the method of access.
2. Read Only Memory (ROM)
ROM consists of a number of memory locations wherein each location typically stores 8 bits like a RAM. A ROM also uses random access method just like a RAM. The advantage of ROM is that it is non-volatile in nature. That means, though the power supply to the ROM is switched off, the information in the ROM will not be lost. However, only reading operation is possible from a ROM location. Thus, in a computer, ROM is used for storing information which is not lost when power is switched off.
Let us discuss different versions of ROM provided by semiconductor manufacturers for storing information:
Mask-Programmed ROM It derives this name because the information is written to this type of ROM at the time of manufacture by applying a suitable mask. Once written, the information cannot be changed, even by the manufacturer. It is cheaper compared to other types of ROMs when considering cost per unit quantity, but requires bulk ordering. It is used in equipment produced in large quantities.
Programmable Read Only Memory (PROM) The user writes information to this type of ROM using a PROM programmer. Once written, the information cannot be changed. Like Mask-Programmed ROM, the information is permanent. It is more expensive than mask ROM but allows purchasing in smaller quantities.
Erasable Programmable Read Only Memory (EPROM) Information is written by the user with an EPROM programmer. As its content is erasable and rewritable, the user can modify it multiple times. Data is erased using strong ultraviolet (UV) light on the quartz window of the EPROM chip, which removes all content. Users can purchase a single piece of EPROM and rewrite its content multiple times.
Electrically Erasable Programmable Read Only Memory (EEPROM) Information is written by the user using an EPROM programmer. Unlike EPROM, EEPROM data is erased using electrical signals rather than UV light. EEPROM allows selective data erasure and is more expensive than other ROM types. It is gaining popularity due to its flexibility.
| Types of ROM |
Info.entered by |
Possible to change info? |
Cost per chip |
Min.order quantity |
Method of erasing info. |
Application area |
|---|---|---|---|---|---|---|
| Mask-programmed ROM |
Manufacturer |
No |
Cheapest |
Large |
Not possible |
Large-scale production |
| PROM |
User |
No |
Costlier |
One |
Not possible |
Medium-scale production |
| EPROM |
User |
Yes |
Even more costly |
One |
Using strong UV source |
R& D |
| EEPROM |
User |
Yes |
Costliest |
One |
Using electrical signals |
R& D |
Secondary Memory
Computer secondary memory stores data and programs permanently, even when the computer is off.The secondary memory is also known as external memory or auxiliary memory.
Classification of Secondary Memory
Here is the complete classification of secondary memory:
-
Magnetic Storage
- Hard Disk Drive (HDD)
- Floppy Disk (Obsolete)
- Magnetic Tape
-
Optical Storage
-
CD (Compact Disc)
- CD-ROM (Read-Only Memory)
- CD-R (Recordable)
- CD-RW (Rewritable)
-
DVD (Digital Versatile Disc)
- DVD-ROM
- DVD-R/DVD+R
- DVD-RW/DVD+RW
- Blu-ray Disc (BD)
-
CD (Compact Disc)
-
Flash Storage (Solid-State Storage)
- Solid-State Drive (SSD)
- USB Flash Drive (Pen Drive)
- Memory Cards (SD Card, microSD, etc.)
-
Cloud Storage
- Google Drive
- Dropbox
- OneDrive
- Amazon S3
-
Hybrid Storage
- Hybrid Drive (HDD + SSD Combination)
- SSHD (Solid-State Hybrid Drive)
Cache Memory
Cache memory is smaller and faster than RAM. It is placed closer to the CPU than the RAM.
Different types of cache memory, like L1, L2, and L3 cache, have different speeds and amounts of space.
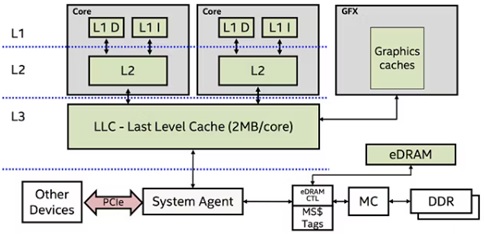
The Levels of Cache Memory: L1, L2, and L3
CPU Cache memory is divided into three "levels": L1, L2, and L3. The memory hierarchy is again according to the speed and, thus, the cache size.
L1 Cache
Level 1 cache is a computer's fastest memory. The CPU's most frequently accessed data resides in the L1 cache. CPU determines L1 cache size. Some high-end consumer CPUs, such as the Intel i9-9980XE, have a 1MB L1 cache, but they are expensive and rare. Server chipsets like Intel's Xeon have 1-2MB L1 memory cache. Before buying, examine the CPU specs to ascertain the L1 cache size. There is no "standard" amount.
Source: [1]
The L1 cache normally has two sections: the instruction cache, which stores CPU operation information, and the data cache, which stores operation data.
L2 Cache
Level 2 cache is larger but slower than L1. Modern L2 memory caches are gigabytes, not kilobytes. AMD's top-rated Ryzen 5 5600X has 384KB L1 and 3MB L2 caches and 32MB L3 cache. The L2 cache size depends on the CPU but is usually 256KB to 32MB. Nowadays, most CPUs have more than 256KB L2 cache, which is small. Some of the most powerful current CPUs have L2 memory caches exceeding 8MB. In terms of speed, the L2 cache is slower than the L1 cache but still faster than the system RAM. L2 caches are 25 times faster than RAM, while L1 caches are 100 times faster.
L3 Cache
Level 3 cache. The L3 memory cache was originally on the motherboard. This was long ago when most CPUs were single-core. The L3 cache on top-end consumer CPUs can reach 32MB, while AMD's groundbreaking Ryzen 7 5800X3D CPUs have 96MB. CPU L3 caches in some servers can reach 128MB.
The largest and slowest cache memory unit is L3. Modern CPUs have an on-chip L3 cache. The chip's L1 and L2 caches serve each core, while the L3 cache is more like a memory pool for the whole chip. The following images illustrate the CPU memory cache levels for a 2012 Intel Core i5-3570K CPU and a 2020 AMD Ryzen 5800X CPU. The second image's bottom right corner contains CPU cache data.
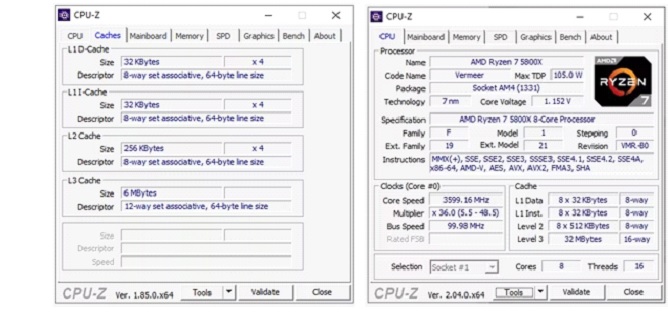
Source: [1]
Note how both CPUs have a split L1 cache and larger L2 and L3 caches. On the AMD Ryzen 5800X, the L3 cache is over five times greater than the Intel i5-3570K.
How cache memory works:
- Hierarchy − Computers normally have L1, L2, and L3 caches are the several layers of cache memory. The L1 cache is the smallest and fastest cache, located closest to the CPU; L2 and L3 caches are larger and slower.
- Cache Organization − Each block or line of cache memory contains a small bit of data copied from the main memory. The CPU accesses cache memory in fixed-size blocks, not bytes.
- Cache Coherency − Cache coherency ensures cached data matches the main memory data. Cache coherence techniques update other cores' caches when one core writes to a memory location in a multi-core processor.
- Cache Replacement Policies − A cache replacement policy decides which block to evict when the cache is full and a new block is needed. LRU, FIFO, and Random Replacement are common policies.
- Cache Access − The CPU checks the cache before reading or writing data. When data is cached, the CPU can quickly retrieve it. If data is not in the cache (cache miss), the CPU must fetch it from the main memory, which may delay it.
- Cache Hierarchy − Modern processors contain L1, L2, and L3 caches that grow in capacity and latency farther from the CPU cores. Parallel access is achieved by splitting the L1 cache into instruction and data caches.
- Cache Management − Optimization of cache utilization maximizes hit rates and minimizes miss penalties. Prefetching, where the processor predicts memory accesses and loads data into the cache, improves cache performance.
Cache memory buffers frequently access data between the CPU and main memory to speed up processing and increase system performance. Modern computer systems require effective management and structure for optimal performance.
Register Memory
Register memory, which is also called processor registers or "registers," is the smallest and fastest type of computer memory that is directly integrated into the CPU. Registers are small, fast storage units inside the CPU that are used to quickly store data that is being processed or instructions that are being run.
Registers serve several important functions in a computer system:
- Instruction Execution − Registers hold the instructions that the CPU is currently running. This includes the operation code (opcode) and associated operands with it.
- Data Storage − Registers store CPU-processed data. This can provide memory addresses, intermediate values during arithmetic or logical operations, and other data needed by the instructions being executed.
- Addressing − Memory addresses are used to store or retrieve data from memory locations in RAM or other parts of the computer's memory hierarchy.
Types of Registers
- Program Counter (PC) − Stores the memory address of the next instruction to be fetched and executed.
- Instruction Register (IR) − Holds the current instruction being executed by the CPU.
- Memory Address Register (MAR) − Stores the memory address of data being read from or written to memory.
- Memory Data Register (MDR) − Contains the actual data being read from or written to memory.
- General-Purpose Registers (GPRs) − Used for general data storage and manipulation during program execution.
