
- ITIL - Home
- ITIL - Overview
- ITIL - Terminologies
- ITIL - Service Basics
- ITIL - Service Lifecycle
- Service Strategy
- ITIL - Service Strategy Overview
- ITIL - Service Strategy Roles
- ITIL - Strategy Generation
- ITIL - Service Portfolio Management
- Business Relationship Management
- ITIL - Demand Management
- ITIL - Financial Management
- Service Design
- ITIL - Service Design Overview
- ITIL - Service Catalogue Management
- ITIL - Service Level Management
- ITIL - Capacity Management
- ITIL - Availability Management
- ITIL - Service Continuity Management
- Information Security Management
- ITIL - Supplier Management
- Service Transition
- ITIL - Service Transition Overview
- ITIL - Project Management
- ITIL - Change Management
- Service Assets and Configuration Management
- Release and Deployment Management
- ITIL - Service and Validation Testing
- Service Operation
- ITIL - Service Operation Overview
- ITIL - Event Management
- ITIL - Incident and Request
- ITIL - Problem Management
- ITIL - Access Management
- Continual Service Improvement
- CSI Overview
- Service Reporting
Incident Management and Request Fulfillment
Overview
Incident is defined as any disruption in IT service. Incident can be reported either through the Service Desk or through an interface from event management to incident management tools.
Incident Management deals with handling incident and ensures to restore IT service soon as possible.
Incident Manager is the process owner of this process.
Incident Models
There are always some incidents which are not new. They may happen again over a period of time. Therefore, it is a best practice to have pre-defined model to handle such incidents.
An incident model should include −
Steps that should be taken to handle the incident
Chronological order these steps should be taken in, with any dependences or co-processing defined.
Responsibilities who should do what
Timescales and thresholds for completion of the actions
Escalation procedures; who should be contacted and when
Any necessary evidence-preservation activities
Incident Management Process
The following diagram shows several standard steps to be taken when an incident occurs −
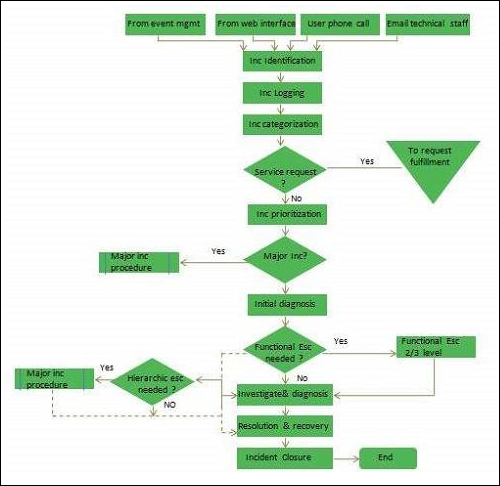
Incident Logging
All incidents should be fully logged and date/time stamped.
Incident Categorization
It is important later when looking at incident types/frequencies to establish trends for use in Problem Management.
Incident Prioritization
It deals with severity of an incident Low, Medium or High.
Incident Diagnosis
Service Desk analyst must carry out initial diagnosis while the user is on call and try to discover the full symptoms of the incident and to determine exactly what has gone wrong and how to correct it.
Incident Escalation
Various aspects of incident escalation are as follows −
Function escalation
When it becomes clear that Service Desk is unable to resolve the incident or target time for Service Desk has been exceeded, the incident must be escalated immediately for further support.
Hierarchic escalation
Hierarchic escalation is done when either incident is serious in nature or Investigation and Diagnosis is taking too long time.
Investigation and diagnosis
It includes the following activities −
Understanding what exactly has gone wrong.
Understanding chronological order of the events
Confirming the full impact of the incident
Identifying any events that could have triggered the incident
Searching for previous similar kind of incidents
Resolution and recovery
A potential resolution need to be identified, applied and tested.
Incident closure
Before closing an incident, Service desk should ask the user whether he is satisfied and agree to close the incident.
Request Fulfilment
Service Request refers to demand by the users. These requests can be regarding small changes, changing the password, installing additional software application, requesting information etc.
An incident is unplanned event but Service Request can be planned.
Key Points
Depending upon the number of Service Requests, an organization usually has, a specialized team that can be formed to fulfil those requests.
For frequently recurring requests, a predefined model can be devised to fulfil the requests.
