Article Categories
- All Categories
-
 Data Structure
Data Structure
-
 Networking
Networking
-
 RDBMS
RDBMS
-
 Operating System
Operating System
-
 Java
Java
-
 MS Excel
MS Excel
-
 iOS
iOS
-
 HTML
HTML
-
 CSS
CSS
-
 Android
Android
-
 Python
Python
-
 C Programming
C Programming
-
 C++
C++
-
 C#
C#
-
 MongoDB
MongoDB
-
 MySQL
MySQL
-
 Javascript
Javascript
-
 PHP
PHP
-
 Economics & Finance
Economics & Finance
Bypass Anti-virus using Veil Framework
This article demonstrates how to bypass antivirus detection using the Veil Framework, a collection of penetration testing tools. The framework consists of several modules designed for payload generation and evasion techniques.
Veil Framework Components
The Veil Framework includes the following key modules ?
- Veil-Evasion ? generates antivirus-evading payloads using various techniques and programming languages
- Veil-Catapult ? a psexec-style payload delivery system that integrates with Veil-Evasion
- Veil-PowerView ? a PowerShell tool for network reconnaissance on Windows domains
- Veil-Pillage ? a modular post-exploitation framework integrated with Veil-Evasion
System Requirements
Before installing the Veil Framework, ensure your system has the latest Python packages configured. The installation requires superuser privileges, so use sudo or switch to the root user account.
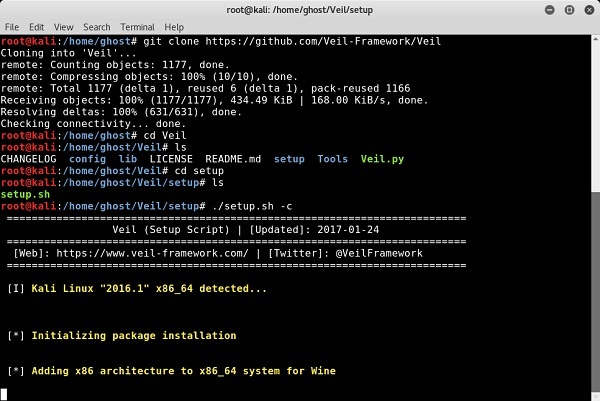
Installation Process
Follow these steps to install the Veil Framework from GitHub ?
git clone https://github.com/Veil-Framework/Veil.git cd Veil/ ./config/setup.sh --force --silent
The installation script will automatically configure all dependencies and required components.
Generating Payloads
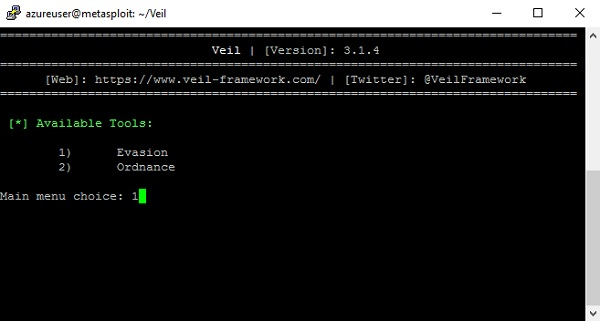
Step 1: Select Evasion Module
Launch Veil and select the Evasion module from the main menu to begin payload generation ?
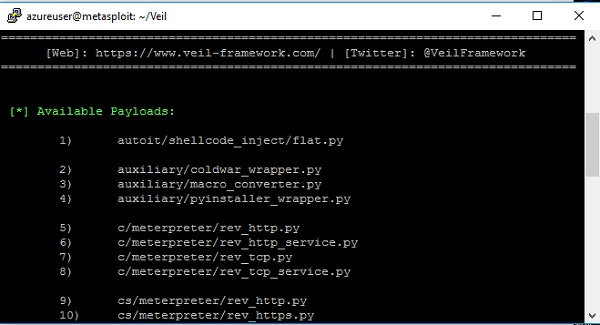
Step 2: List Available Payloads
Use the list command to display all available payload options. This shows various programming languages and techniques you can use ?
Step 3: Select Payload Type
Choose your desired payload using the use command followed by the payload number. This will load the specific payload configuration ?
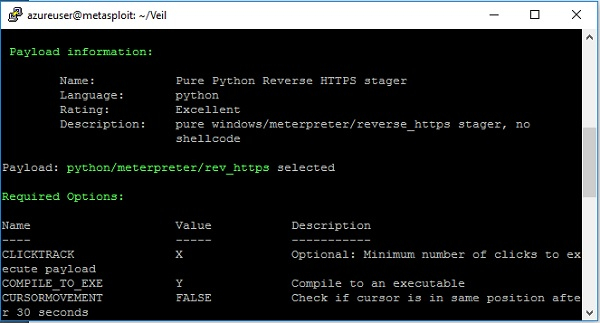
Step 4: Configure and Generate
Select the py2exe compiler option and execute the generate command to create your FUD (Fully Undetectable) payload ?
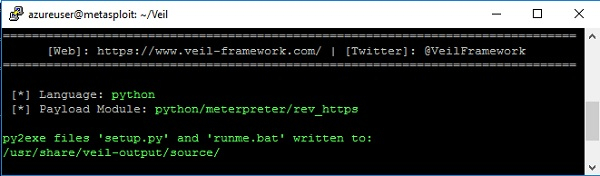
The generated payload file runme.bat will be stored in the /usr/share/veil-output/source directory, ready for deployment in your penetration testing scenarios.
Key Benefits
The Veil Framework offers several advantages for penetration testers ?
- Multiple payload formats and programming languages
- Advanced evasion techniques to bypass modern antivirus solutions
- Automated payload generation with minimal configuration
- Integration with popular penetration testing frameworks
Conclusion
The Veil Framework provides an effective solution for generating antivirus-evading payloads during authorized penetration testing. Its modular design and multiple evasion techniques make it a valuable tool for security professionals testing defensive measures.


