Article Categories
- All Categories
-
 Data Structure
Data Structure
-
 Networking
Networking
-
 RDBMS
RDBMS
-
 Operating System
Operating System
-
 Java
Java
-
 MS Excel
MS Excel
-
 iOS
iOS
-
 HTML
HTML
-
 CSS
CSS
-
 Android
Android
-
 Python
Python
-
 C Programming
C Programming
-
 C++
C++
-
 C#
C#
-
 MongoDB
MongoDB
-
 MySQL
MySQL
-
 Javascript
Javascript
-
 PHP
PHP
-
 Economics & Finance
Economics & Finance
Features that Matter in an Effective Mobile Anti-Virus!!
The usage of the smartphone has witnessed exponential growth in recent times. The benefit of using a smart device coupled with an active internet connection is endless. However, with multiple advantages, there is a possibility of unwanted suspicious threats. These threats are regarding the fall of your sensitive data which is present inside a mobile which may go into wrong hands through malware or spyware.

Though most mobile users think antivirus as the only savior from a disaster, they lack the knowledge of judging the best one among all available. It takes a lot of parameters to decide the exact worthiness of an antivirus for getting it installed. This article aims at providing the requisite information in much detail.
What is Mobile Malware?
Mobile malware is a kind of unwanted buggy software that can cause significant loss of technological workflow. The malware not only exploits the OS but also paralyze the smooth functioning of the device. The amount of such malware is growing at an alarming rate which has become the core for tech concerning freaks. There are multiple kinds to it. Some of the major notable categories are –
Trojans
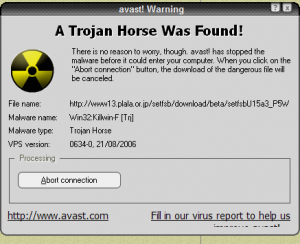
Trojans are those type of malware which gets attached with the healthy-seeming apps silently and soon after their entry start to attack the system. Their main aim is to steal the confidential login information related to banks or institutions without the knowledge of the user.
Phishing Apps
These are the more ‘trojanized” version of the earlier one. They mimic themselves as one of the important application that one user may find interesting to download. They do so just to get installed on your system, and even before you acknowledge them as a next-to-be-deleted app, they will steal the information that they want from you.

Bot Processes
It is a little-sophisticated version of its kind as it operates hidden from the background without getting noticed. They keep running as executable files and wait for the golden moments to strike, like opening an online banking page or transferring money, etc. The advanced versions of botnets are even programmed to await the instruction from their masters to work more efficiently.

Most question on how to know that their mobile has been infected with malware. The simple answer to that lies in the unwanted behaviors shown by your device or degradation in the performance level than normal. The perfect way of shielding is to opt for an effective Mobile Antivirus that has potential to detect and successfully eliminate them completely.
Antivirus and Authenticity
With the above-mentioned reality of mobile malware, it is easy for anyone to hit on to a mobile antivirus. But installing the same and getting tension free from any of the future consequences due to malware attacks is not wise though. Many times, users have questioned upon the authenticity of the genuine working ability of Antivirus.

If major antivirus brands are taken into an analysis, most offer some level of data backup, remote wipe, GPS tracking and remote locking. However, the features fall short when compared to desktop applications. Desktop security systems regularly scan the newly downloaded file and keep a regular checking on other documents on a real-time basis which lacks in the mobile feature.
When it comes to desktop versions, security applications are lighter and provide ease of doing normal things without getting system hanged. However, same is not the case in mobiles. Most users complain that antivirus is making their operating system run slower. Also, things like asking for repetitive updates and unnecessary reboot of the system irritates them.
Key Considerations to Look for in Antivirus
Most antivirus companies may claim them to be superior to others regarding providing additional features to attract you. However, one must know the exact key parameters that matter while going for an effective mobile antivirus. So here is the list depicting all necessary key elements of an ideal antivirus.
Email Scanning
Despite the presence of spam folders in the emails, lots of complaints about the loss of sensitive data information comes from the ground of email hacking only. The spammers are best in their skills to turn a spam mail into a reasonable one so that you may consider of clicking them.
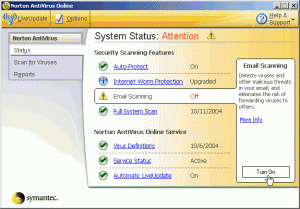
In this regards, the antivirus plays a major role over here, as it scans each mail against its global database that contains similar spammer list. Once it gets a match, it immediately warns you and even prompts you to delete that. In that way, you can save your hard drive being erased completely against prying eyes.
Protection for Suspicious Downloads
Internet is full of lucrative files that attract users to download them. Most of them are spyware thus need to be prevented from getting the download. Make sure about this feature before making a choice. The antivirus should not only detect the suspicious downloads but also should remove any such pre-downloaded ones soon after its installation.
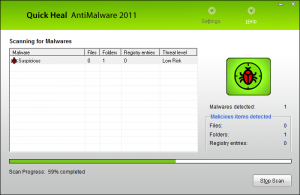
Speed
This term refers to two aspects; the speed with which it scans files and the speed with which your phone operates post antivirus installation. Most antivirus software slows down the performance level of the phone by putting a lot of pressure on the CPU.

Similarly, in the name of “Quick-scan”, most antivirus fails to scan thick subfolders that possibly contain suspicious malware. Speedy scan even detects potential files. To make sure, these parameters are available, read the users review through various online shopping websites. Referring the views can save the money from getting wasted on the wrong antivirus.
Compatibility

Before blindly jumping into any paid software, make sure that it is well compatible with your device. Most times Mac users face compatibility issue with an antivirus that Windows or Android users do not face. Check the online guidelines of the antivirus in which they explicitly mention the compatible OS with their versions.
Requires Storage Space

Mobile antivirus is hated by most for demanding longer digital space memory inside the phone, which most users don’t have. The application runs smooth when installing in phone memory rather than on SD card, says study. In this regard, the people who do not use any external SD card and ultimately depend upon phone’s internal memory face the heat. Don’t forget to look for this parameter in the first hand.
Privacy Policy
A phone contains lots of personal data and sensitive information. On getting stolen or moving into the wrong hands can ultimately put those at risk. In this regard, a mobile antivirus can wipe off the complete data as well as sensitive information on getting a hint from the user.

It can also backup that valuable information into its cloud database so that one can retrieve them into his new mobile through proper login and authentication. Some antivirus giants have also integrated the live tracking feature to track the real-time location of the stolen mobile.
Simple UI Design

Nobody wants to waste his time to understand the complex user interface of any antivirus. The simpler the graphic user interface will be, the easier it will be to use. Make sure, the antivirus that you wish to buy for must stand tall in this regard.
Conclusion
Though judging all the above-said features before the use is a daunting task, the same can be smoother, if some the antivirus will have a free trial version. Trail versions have limited functionalities and features to showcase, but the common performance parameters like speed, compatibility and quick scan qualities can be well judged.


