
- CICS Tutorial
- CICS - Home
- CICS - Overview
- CICS - Environment
- CICS - Basic Terms
- CICS - Nucleus
- CICS - Transactions
- CICS - COBOL Basics
- CICS - BMS
- CICS - MAP
- CICS - Interface Block
- CICS - Pseudo Programming
- CICS - Aid Keys
- CICS - File Handling
- CICS - Error Handling
- CICS - Control Operations
- CICS - Temporary Storage
- CICS - Intercommunication
- CICS - Status Codes
- CICS - Interview Questions
- CICS Useful Resources
- CICS - Quick Guide
- CICS - Useful Resources
- CICS - Discussion
CICS - Basic Terms
We must have knowledge of the basic terms used in CICS to get a better understanding of how it works. Application programs use CICS for communication with remote and local terminals and subsystems.
IBM 3270 Terminal
The 3270 Information Display System is a family of display and printer terminals. 3270 terminals were being used to connect to the mainframe via IBM controllers. Today, 3270 emulation software is available which means that even normal PCs can be used as 3270 terminals. 3270 terminals are dumb terminals and do not do any processing themselves. All processing needs to be done by the application program. IBM terminals consist of the following components −
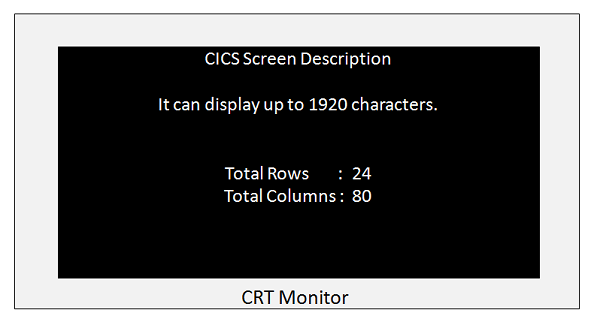
CRT Monitor
The CRT monitor displays the output or the input fields of the application program. A screenshot of a 3278 Model of CRT monitor is shown below. It has the following characteristics −
It is capable of displaying 1920 characters.
Each of these 1920 character positions is individually addressable.
A COBOL application program can send data to all the positions on the screen.
The display characteristics like intensity, protected, non-protected of the field can be set using BMS which we will be discussing in detail in upcoming modules.
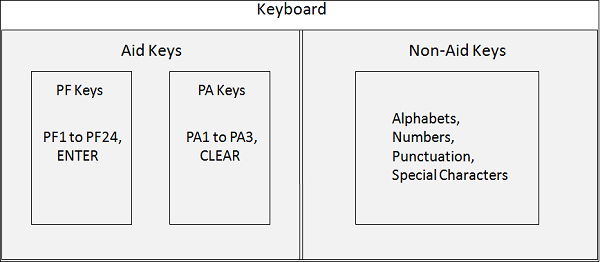
Keyboard
IBM keyboard keys are divided into following two categories −
Non-AID Keys − All other keys for alphabets, numeric, punctuation etc. are Non-Aid keys. When the user types text or numbers using non-aid keys, CICS will not even know if the user is typing anything or not.
AID Keys − AID keys are known as Attention Identifier Keys. CICS can detect only AID keys. After typing all the input, only when the user presses one of the AID keys, CICS takes control. AID Keys : ENTER, PF1 to PF24, PA1 to PA3, CLEAR. AID keys are further divided into two categories −
PF Keys − PF keys are known as function keys. PF keys allow transfer of data from terminal to CICS. PF Keys are ENTER and PF1 to PF24.
PA Keys − PA keys are known as Program Access keys. PA keys do not allow transfer of data between terminal and CICS. PA Keys are PA1 to PA3 and CLEAR.
Transaction
A CICS program is invoked through a transaction. A CICS transaction is a collection of logically related programs in an application. The whole application could be logically divided into several transactions.
Transaction identifiers which are 1 to 4 characters long are used to identify the transactions which the users want to do.
A programmer links one program to the transaction identifier which is used to invoke all the application programs for that particular transaction.
Task
A Task is a unit of work which is specific to a user.
Users invoke an application by using one of the transaction identifiers. CICS looks up for the transaction identifier to find out which program to invoke first to do the work requested. It creates a task to do the work, and transfers control to the mentioned program.
A transaction can be completed through several tasks.
A task can receive data from and send data to the terminal that started it. It can read and write files and can start other tasks also.
Task vs. Transaction
The difference between a transaction and a task is that several users can invoke a transaction but each user initiates his own task.
LUW
LUW stands for Logical Unit of Work. LUW states that a piece of work should be done completely or not done at all. A task can contain several Logical Unit of Works in CICS. We will discuss more about it in upcoming modules.
Application
An application is a series of logically grouped programs to form several transactions which is used to complete a specific task for the end-user.