
- Cryptography - Home
- Cryptography - Origin
- Cryptography - History
- Cryptography - Principles
- Cryptography - Applications
- Cryptography - Benefits & Drawbacks
- Cryptography - Modern Age
- Cryptography - Traditional Ciphers
- Cryptography - Need for Encryption
- Cryptography - Double Strength Encryption
- Cryptosystems
- Cryptosystems
- Cryptosystems - Components
- Attacks On Cryptosystem
- Cryptosystems - Rainbow table attack
- Cryptosystems - Dictionary attack
- Cryptosystems - Brute force attack
- Cryptosystems - Cryptanalysis Techniques
- Types of Cryptography
- Cryptosystems - Types
- Public Key Encryption
- Modern Symmetric Key Encryption
- Cryptography Hash functions
- Key Management
- Cryptosystems - Key Generation
- Cryptosystems - Key Storage
- Cryptosystems - Key Distribution
- Cryptosystems - Key Revocation
- Block Ciphers
- Cryptosystems - Stream Cipher
- Cryptography - Block Cipher
- Cryptography - Feistel Block Cipher
- Block Cipher Modes of Operation
- Block Cipher Modes of Operation
- Electronic Code Book (ECB) Mode
- Cipher Block Chaining (CBC) Mode
- Cipher Feedback (CFB) Mode
- Output Feedback (OFB) Mode
- Counter (CTR) Mode
- Classic Ciphers
- Cryptography - Reverse Cipher
- Cryptography - Caesar Cipher
- Cryptography - ROT13 Algorithm
- Cryptography - Transposition Cipher
- Cryptography - Encryption Transposition Cipher
- Cryptography - Decryption Transposition Cipher
- Cryptography - Multiplicative Cipher
- Cryptography - Affine Ciphers
- Cryptography - Simple Substitution Cipher
- Cryptography - Encryption of Simple Substitution Cipher
- Cryptography - Decryption of Simple Substitution Cipher
- Cryptography - Vigenere Cipher
- Cryptography - Implementing Vigenere Cipher
- Modern Ciphers
- Base64 Encoding & Decoding
- Cryptography - XOR Encryption
- Substitution techniques
- Cryptography - MonoAlphabetic Cipher
- Cryptography - Hacking Monoalphabetic Cipher
- Cryptography - Polyalphabetic Cipher
- Cryptography - Playfair Cipher
- Cryptography - Hill Cipher
- Polyalphabetic Ciphers
- Cryptography - One-Time Pad Cipher
- Implementation of One Time Pad Cipher
- Cryptography - Transposition Techniques
- Cryptography - Rail Fence Cipher
- Cryptography - Columnar Transposition
- Cryptography - Steganography
- Symmetric Algorithms
- Cryptography - Data Encryption
- Cryptography - Encryption Algorithms
- Cryptography - Data Encryption Standard
- Cryptography - Triple DES
- Cryptography - Double DES
- Advanced Encryption Standard
- Cryptography - AES Structure
- Cryptography - AES Transformation Function
- Cryptography - Substitute Bytes Transformation
- Cryptography - ShiftRows Transformation
- Cryptography - MixColumns Transformation
- Cryptography - AddRoundKey Transformation
- Cryptography - AES Key Expansion Algorithm
- Cryptography - Blowfish Algorithm
- Cryptography - SHA Algorithm
- Cryptography - RC4 Algorithm
- Cryptography - Camellia Encryption Algorithm
- Cryptography - ChaCha20 Encryption Algorithm
- Cryptography - CAST5 Encryption Algorithm
- Cryptography - SEED Encryption Algorithm
- Cryptography - SM4 Encryption Algorithm
- IDEA - International Data Encryption Algorithm
- Public Key (Asymmetric) Cryptography Algorithms
- Cryptography - RSA Algorithm
- Cryptography - RSA Encryption
- Cryptography - RSA Decryption
- Cryptography - Creating RSA Keys
- Cryptography - Hacking RSA Cipher
- Cryptography - ECDSA Algorithm
- Cryptography - DSA Algorithm
- Cryptography - Diffie-Hellman Algorithm
- Data Integrity in Cryptography
- Data Integrity in Cryptography
- Message Authentication
- Cryptography Digital signatures
- Public Key Infrastructure
- Hashing
- MD5 (Message Digest Algorithm 5)
- SHA-1 (Secure Hash Algorithm 1)
- SHA-256 (Secure Hash Algorithm 256-bit)
- SHA-512 (Secure Hash Algorithm 512-bit)
- SHA-3 (Secure Hash Algorithm 3)
- Hashing Passwords
- Bcrypt Hashing Module
- Modern Cryptography
- Quantum Cryptography
- Post-Quantum Cryptography
- Cryptographic Protocols
- Cryptography - SSL/TLS Protocol
- Cryptography - SSH Protocol
- Cryptography - IPsec Protocol
- Cryptography - PGP Protocol
- Image & File Cryptography
- Cryptography - Image
- Cryptography - File
- Steganography - Image
- File Encryption and Decryption
- Cryptography - Encryption of files
- Cryptography - Decryption of files
- Cryptography in IoT
- IoT security challenges, Threats and Attacks
- Cryptographic Techniques for IoT Security
- Communication Protocols for IoT Devices
- Commonly Used Cryptography Techniques
- Custom Building Cryptography Algorithms (Hybrid Cryptography)
- Cloud Cryptography
- Quantum Cryptography
- DNA Cryptography
- One Time Password (OTP) algorithm in Cryptography
- Difference Between
- Cryptography - MD5 vs SHA1
- Cryptography - RSA vs DSA
- Cryptography - RSA vs Diffie-Hellman
- Cryptography vs Cryptology
- Cryptography - Cryptology vs Cryptanalysis
- Cryptography - Classical vs Quantum
- Cryptography vs Steganography
- Cryptography vs Encryption
- Cryptography vs Cyber Security
- Cryptography - Stream Cipher vs Block Cipher
- Cryptography - AES vs DES ciphers
- Cryptography - Symmetric vs Asymmetric
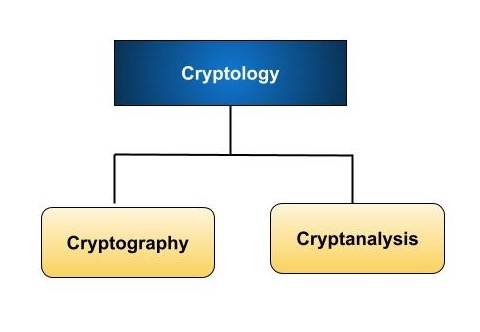
Cryptography - Cryptology vs Cryptanalysis
Cryptology and cryptanalysis are two key terms in cryptography − science and art of protecting one's secrecy and confidentiality of messages.
Cryptology is a broad umbrella term. It is the study of generating and breaking secret codes. In simple terms, it is about creating codes to protect information and determining how to crack such codes.
Cryptanalysis is a control of cryptology that focuses on cracking codes rather than creating them. It is similarly to the role of a detective working to solve a problem. Cryptanalysts use a range of techniques to crack encrypted messages, like pattern analysis, code vulnerability research, and mathematical algorithms.
In brief, cryptology deals with both the creation and breaking of codes, whereas cryptanalysis focuses primarily on the breaking of codes.
What is Cryptology?
The amazing topic of cryptology integrates information security, computer science, and mathematics. The study of hidden codes, including their encryption and decryption, is the basis of cryptology. The main goal of it is encrypting sensitive data to prevent unauthorised persons from accessing or interpreting.
Cryptology gives us tools and techniques of protecting data against unauthorized access as well as tools that can be applied in securing communication. Confidentiality, availability (integrity), privacy among others in preserving information are so critical in many areas such as: payments related activities; digital footprint management; safeguarding intellectual property rights (IPR), non-repudiation messages or evidences among others during an exchange process within organizations.
Cryptology has two main branches-cryptanalysis as well as cryptography. Cryptanalysis studies how one can find hidden data by breaking into secure codes; meanwhile, cryptography makes use of encryption methods in order to establish such codes themselves as impervious. Understanding of pros and cons regarding cryptographic systems comes from understanding logic governing these two domains.
What is Cryptanalysis?
Cryptanalysis is similar to becoming a detective searching for secret codes. It is all about finding out how to decrypt encrypted messages and provide the hidden information hidden within. Cryptoanalysts crack codes rather than creating them, as cryptography does.
They use a number of techniques and methods, like pattern analysis, code vulnerability discovery, and math-based puzzle solving. It is like cracking a puzzle, attempting to discover the secrets hidden behind encryption.
We need cryptanalysis to find out whether our data protection methods are good enough. Furthermore, programming-related languages can be better if errors are found out by competent professionals.
Difference between Cryptology and Cryptanalysis
| Basis of Difference | Cryptology | Cryptanalysis |
|---|---|---|
| Definition | Encompasses creation and breaking of codes to secure or reveal information | Specifically concentrates on decrypting encrypted messages |
| Focus | Deals with both creation and breaking of codes | Solely focuses on breaking codes to reveal content |
| Goal | Primary objective is to protect sensitive information through encryption methods | Aims to decrypt encrypted data, essentially breaking the encryption |
| Techniques | Employs encryption and decryption techniques | Utilizes methods such as statistical analysis, pattern recognition, and mathematical algorithms |
| Application | Used in secure communication, data protection, and digital signatures | Commonly used in security assessments, intelligence operations, and code-breaking endeavors |
| Skillset | Requires expertise in encryption methods, cryptographic protocols, and algorithm design | Demands analytical thinking, mathematical proficiency, and understanding of encryption algorithms |
| Objective | Aims to ensure confidentiality and integrity of information | Endeavors to uncover hidden information by decrypting messages |
| Importance | Crucial for establishing secure communication channels and safeguarding sensitive data | Plays a vital role in assessing security of cryptographic systems and identifying vulnerabilities |
| Examples | Includes creating ciphers, designing encryption algorithms like AES, and implementing secure communication protocols | Involves breaking encrypted messages and deciphering codes |
| Historical Role | Played a significant role in military communications, diplomacy, and securing financial transactions | Employed in intelligence operations, espionage activities, and code-breaking during wars |
Summary
Cryptology is the discipline of encryptingand decryptingsecret codes, whereas cryptanalysis is just the science of breaking them. Cryptology uses cryptic techniques to protect sensitive data, whereas cryptanalysis deciphers cryptic information. Cryptology involves coding and decoding means whereas cryptanalysis rests on such tools as statistical analysis and signal recognition. Cryptology is used in secure communication, encryption and signature appending.
