Article Categories
- All Categories
-
 Data Structure
Data Structure
-
 Networking
Networking
-
 RDBMS
RDBMS
-
 Operating System
Operating System
-
 Java
Java
-
 MS Excel
MS Excel
-
 iOS
iOS
-
 HTML
HTML
-
 CSS
CSS
-
 Android
Android
-
 Python
Python
-
 C Programming
C Programming
-
 C++
C++
-
 C#
C#
-
 MongoDB
MongoDB
-
 MySQL
MySQL
-
 Javascript
Javascript
-
 PHP
PHP
-
 Economics & Finance
Economics & Finance
What are snoopy cache protocols in computer architecture?
Snoopy cache protocols are very popular in shared bus multiprocessors due to their relative simplicity. They have both write-update and write-invalidate policy versions. Write-invalidate snoopy cache protocols resemble this protocol in many ways and therefore are also easy to understand after studying a write-update protocol.
The definition of transmission routes of commands can be omitted in snoopy cache protocols since the commands are uniformly broadcasted on the shared bus. The protocol applies both the write-back and the write-through update policies. The former is used for private blocks, the latter for shared blocks.
The description of possible states of blocks in caches. It includes
valid-exclusive − The block is the only copy of the memory block. The cache and memory blocks are consistent.
Shared − There are several cached copies of the memory block and all of them are consistent.
Dirty − It is the only copy of the memory block and the memory block is inconsistent.
The description of commands to be implemented at multiple read/write hit/miss actions.
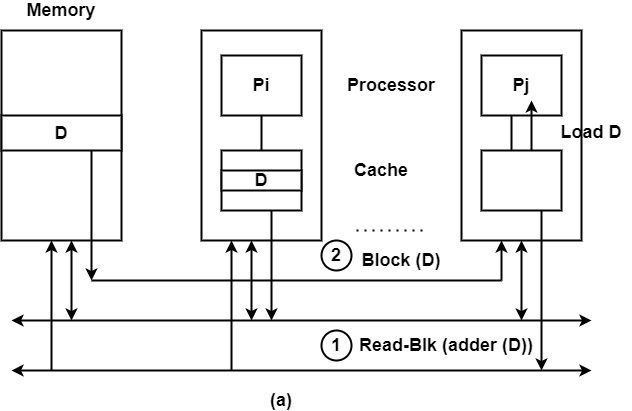
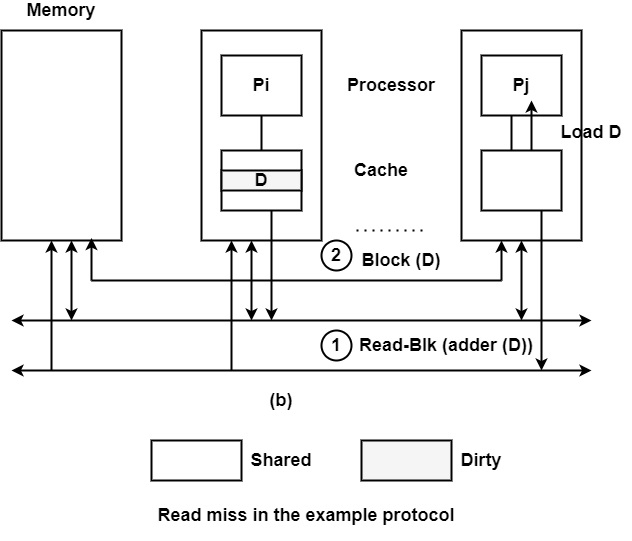
Read miss − The snoopy cache controller broadcasts a Read-blk command on the bus.
If there are shared copies of the data, the containing caches deliver the required copy as shown in figure (a) where Pj has a read miss. The resulting state in the requested processor will be shared.
If a dirty copy exists, it supplies the necessary copy and updates the main memory. All the copies become shared. This mechanism is shown in figure (b).
If a valid-exclusive copy exists, it supplies the necessary copy and all the copies become shared.
If there is no cache copy of the block, the memory sends the block which becomes valid-exclusive.
Write hit − If the state of the block is valid-exclusive or dirty, the write operation can be performed locally (no command is placed on the bus) and the new state will be dirty (write-back policy).
If the block is shared, the snoopy cache controller broadcasts an Update-blk command on the bus. The Update-blk command contains the address and value of the updated data. All copies including the memory one will be updated (write-update, write-through policy) and remain shared.
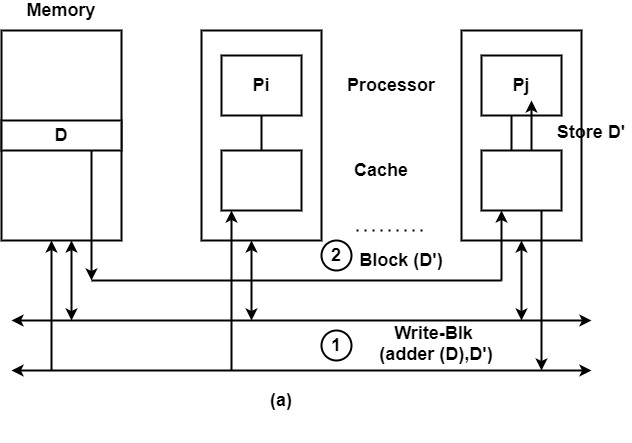
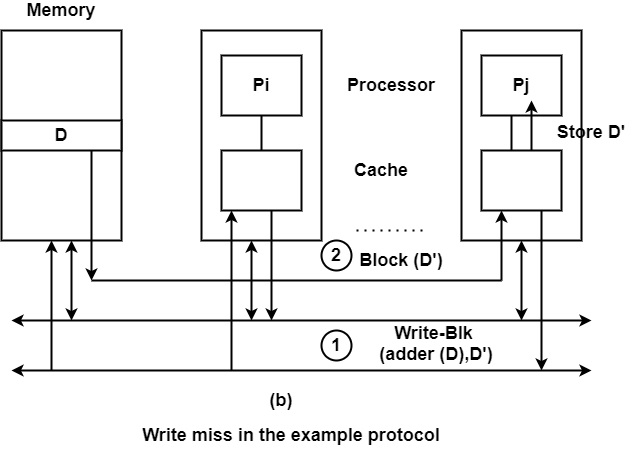
Write miss − The snoopy cache controller broadcasts a Write-blk command on the bus. The write-blk command contains the address and value of the updated data.
If only the memory contains the block, it will be updated with the new value of the updated data, and the update block is sent to the requester processor where it becomes valid-exclusive as shown in figure (a).
If shared copies are available, all copied including the memory one will be updated and the updated block is sent to the requested processor as shown in figure (b). The resulting state of all copies will be shared.
If a dirty or valid-exclusive copy exists, it will be updated and the memory block and the updated block are sent to the requester processor. The resulting state of all copies will be shared.