
- Security Testing - Home
- Security Testing - Overview
- Security Testing - Process
- Security Testing - Malicious Software
- HTTP Protocol Basics
- HTTPS Protocol Basics
- Encoding and Decoding
- Security Testing - Cryptography
- Security Testing - Same Origin Policy
- Security Testing - Cookies
- Hacking Web Applications
- Security Testing - Injection
- Testing Broken Authentication
- Testing Cross Site Scripting
- Insecure Direct Object Reference
- Testing Security Misconfiguration
- Testing Sensitive Data Exposure
- Missing Function Level Access Control
- Cross Site Request Forgery
- Components with Vulnerabilities
- Unvalidated Redirects and Forwards
- Security Testing - Ajax Security
- Testing Security - Web Service
- Security Testing - Buffer Overflows
- Security Testing - Denial of Service
- Testing Malicious File Execution
- Security Testing - Automation Tools
Security Testing - Denial of Service
Denial of Service (DoS) attack is an attempt by hackers to make a network resource unavailable. It usually interrupts the host, temporary or indefinitely, which is connected to the internet. These attacks typically target services hosted on mission critical web servers such as banks, credit card payment gateways.
Symptoms of DoS
- Unusually slow network performance.
- Unavailability of a particular web site.
- Inability to access any web site.
- Dramatic increase in the number of spam emails received.
- Long term denial of access to the web or any internet services.
- Unavailability of a particular website.
Hands ON
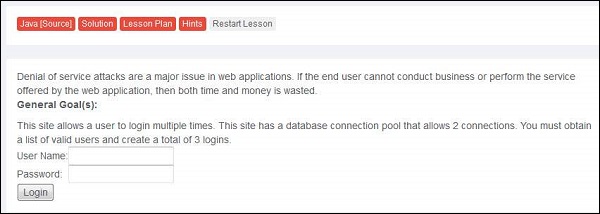
Step 1 − Launch WebGoat and navigate to 'Denial of Service' section. The snapshot of the scenario is given below. We need to login multiple times there by breaching maximum DB thread pool size.
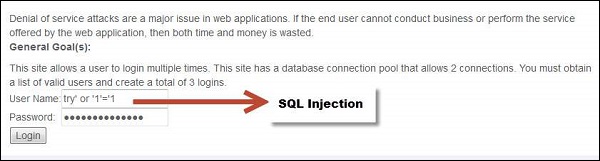
Step 2 − First we need to get the list of valid logins. We use SQL Injection in this case.
Step 3 − If the attempt is successful, then it displays all valid credentials to the user.
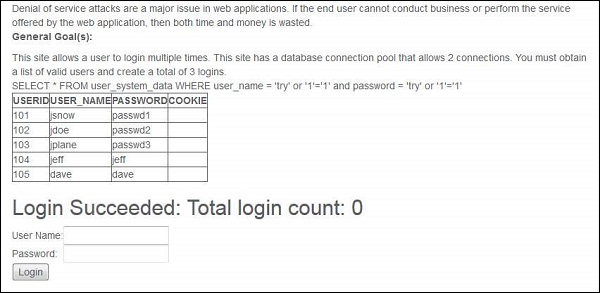
Step 4 − Now login with each one of these user in at least 3 different sessions in order to make the DoS attack successful. As we know that DB connection can handle only two threads, by using all logins it will create three threads which makes the attack successful.

Preventive Mechanisms
Perform thorough input validations.
Avoid highly CPU consuming operations.
It is better to separate data disks from system disks.
