
- SAP GRC - Home
- SAP GRC - Overview
- SAP GRC - Navigation
- SAP GRC - Access Control
- Access Management Work Center
- Access & Authorization Mngmt
- SAP GRC - Authorization
- Access Control Launchpad
- Integration with Access Control
- SAP GRC - Integration with IAM
- SAP GRC - Audit Universe
- Process Control Work Centers
- SAP GRC - SoD Risk Management
- SAP GRC - Risk Management
- SAP GRC - Risk Remediation
- SAP GRC - Mitigation Controls
- SAP GRC - Superuser Privilege
- SAP GRC - Implementing Superuser
- SAP GRC - Enhanced Risk Analysis
- Assigning Mitigation Controls
- SAP GRC - Workflow Integration
- Installation and Configuration
- Data Sources and Business Rules
- SAP GRC - Creating Business Rules
SAP GRC - Access Management Work Center
As per GRC software license, you can navigate Access Management Work Center. It has multiple sections to manage access control activities.
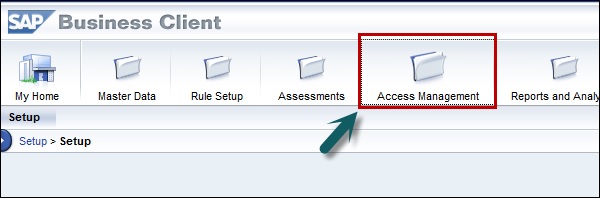
When you click on Access Management Work Center, you can see the following sections −
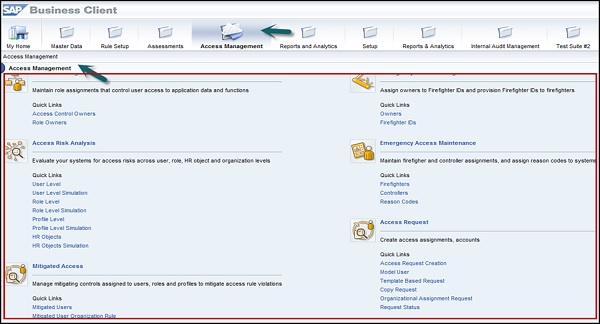
- GRC Role Assignments
- Access Risk Analysis
- Mitigated Access
- Access Requests Administration
- Role Management
- Role Mining
- Role Mass Maintenance
- Superuser Assignment
- Superuser Maintenance
- Access Request Creation
- Compliance Certification Reviews
- Alerts
- Scheduling
The above sections help you in the following ways −
When you go to access risk analysis section, you can evaluate your systems for access risks across users, roles, HR objects and organization levels. An access risk is two or more actions or permissions that, when available to a single user or single role, profile, organizational level, or HR Object, creates the possibility of error or irregularity.
Using mitigated access section, you can identify access risks, assess the level of those risks, and assign mitigating controls to users, roles, and profiles to mitigate the access rule violations.
In access request administration section, you can manage access assignments, accounts, and review processes.
Using role management, you manage roles from multiple systems in a single unified repository.
In role mining group feature, you can target roles of interest, analyze them, and take action.
Using role mass maintenance, you can import and change authorizations and attributes for multiple roles.
In Superuser Assignment section, you can assign firefighter IDs to owners and assign firefighters and controllers to firefighter IDs.
In Superuser Maintenance section, you can perform activities such as researching and maintaining firefighters and controllers, and assigning reason codes by system.
Using access request creation, you can create access assignments and accounts.
Compliance certification reviews supports reviews of users access, risk violations and role assignments.
Using alerts, you can generate by the application for execution of critical or conflicting actions.
Using Scheduling section of the Rule Setup Work Center, you can maintain schedules for continuous control monitoring and automated testing, and to track related job progress.
