- SAP - Home
- SAP - Evolution of SAP
- SAP - Introduction To ERP
- SAP - Modules
- SAP - Architecture
- SAP - GUI Installation
- SAP - Net Weaver
- SAP - Logging onto SAP System
- SAP - GUI Customization
- SAP - End-User Customization
- SAP - GUI Navigation
- SAP - Programming Language (ABAP)
- SAP - SAP Security
- SAP - SAP Basis
- SAP - Transaction Codes
- SAP - Project Lifecycle
- SAP - Career In SAP
SAP - Security
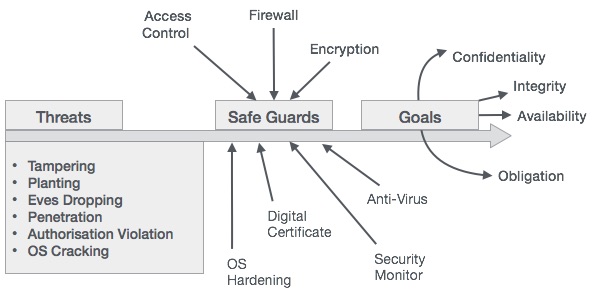
There are three points to look after in order to ensure security −
Confidentiality − Unauthorized disclosure of data
Integrity − Unauthorized modification of data
Availability − Denial of service (a lack of availability of computing resources)
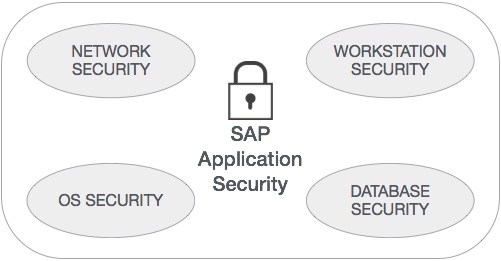
In SAP runtime environment, both application security and unauthorized system access to SAP have to be controlled. The user accounts defined for users in the SAP runtime environment are secured by roles that grant authorizations to them. SAP authorizations control access to transactions (Business Process Activities), or what can be performed within a specific business process step by −
- Keeping unauthorized persons out of the system
- Keeping people out of places where they should not be
- Safeguarding the data from damage or loss
Safeguards
In order to avoid threats, a sound and robust system implements safeguards such as access control, firewall, encryption, O/S hardening, digital certificate, security monitor, and antivirus.
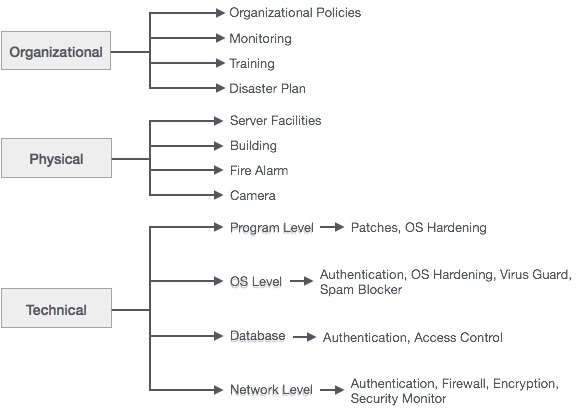
Classification of Security
Security can be classified into three different categories −
- Organizational Security − Related to organization
- Physical − Related to the physical assets
- Technical − Related to technical threats. This is again dived into four types −
- Program-level security
- O/S-level security
- Database security
- Network security
Different Layers of Security
We can help multiple layers of security in a SAP R/3 system.
Authentication − Only legitimate users should be able to access the system.
Authorization − Users should only be able to perform their designated tasks.
Integrity − Data integrity needs to be granted at all time.
Privacy − Protection of data against unauthorized access.
Obligation − Ensuring liability and legal obligation towards stakeholders and shareholders including validation.