
- Home
- Introduction
- Modulation
- Noise
- Analyzing Signals
- Amplitude Modulation
- Sideband Modulation
- VSB Modulation
- Angle Modulation
- Multiplexing
- FM Radio
- Pulse Modulation
- Analog Pulse Modulation
- Digital Modulation
- Modulation Techniques
- Delta Modulation
- Digital Modulation Techniques
- M-ary Encoding
- Information Theory
- Spread Spectrum Modulation
- Optical Fiber Communications
- Satellite Communications
Spread Spectrum Modulation
A collective class of signaling techniques are employed before transmitting a signal to provide a secure communication, known as the Spread Spectrum Modulation. The main advantage of spread spectrum communication technique is to prevent interference whether it is intentional or unintentional.
The signals modulated with these techniques are hard to interfere and cannot be jammed. An intruder with no official access, is never allowed to crack them. Hence these techniques are used for military purposes. These spread spectrum signals transmit at low power density and has a wide spread of signals.
Pseudo-Noise Sequence
A coded sequence of 1s and 0s with certain auto-correlation properties, called as PseudoNoise coding sequence is used in spread-spectrum techniques. It is a maximum-length sequence, which is a type of cyclic code.
Narrow-band Signal
Narrow-band signals have the signal strength concentrated as shown in the frequency spectrum in the following figure.
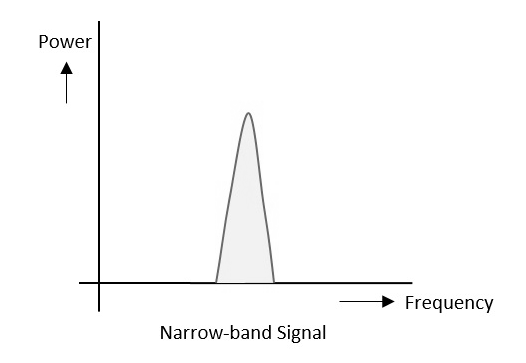
Here are the features of narrow-band signals −
- Band of signals occupy narrow range of frequencies.
- Power density is high.
- Spread of energy is low and concentrated.
Though the features are good, these signals are prone to interference.
Spread Spectrum Signals
The spread spectrum signals have the signal strength distributed as shown in the following frequency spectrum figure.
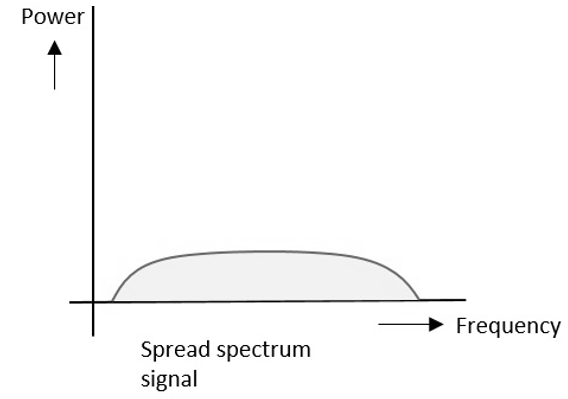
Here are the features of spread spectrum signals −
- Band of signals occupy a wide range of frequencies.
- Power density is very low.
- Energy is widespread.
With these features, the spread spectrum signals are highly resistant to interference or jamming. Since, multiple users can share the same spread spectrum bandwidth without interfering with one another, these can be called as multiple access techniques.
Spread spectrum multiple access techniques use signals which have a transmission bandwidth whose magnitude is greater than the minimum required RF bandwidth.
Spread spectrum signals can be classified into two categories −
- Frequency Hopped Spread spectrum (FHSS)
- Direct Sequence Spread spectrum (DSSS)
Frequency Hopped Spread Spectrum
This is frequency hopping technique, where the users are made to change the frequencies of usage, from one to another in a specified time interval, hence it is called as frequency hopping.
For example, a frequency was allotted to sender 1 for a particular period of time. Now, after a while, sender 1 hops to the other frequency and sender 2 uses the first frequency, which was previously used by sender1. This is called as frequency reuse.
The frequencies of the data are hopped from one to another in order to provide secure transmission. The amount of time spent on each frequency hop is called as Dwell time.
Direct Sequence Spread Spectrum
Whenever a user wants to send data using this DSSS technique, each and every bit of the user data is multiplied by a secret code, called as chipping code. This chipping code is nothing but the spreading code which is multiplied with the original message and transmitted. The receiver uses the same code to retrieve the original message.
This DSSS is also called as Code Division Multiple Access (CDMA).
Comparison between FHSS and DSSS/CDMA
Both the spread spectrum techniques are popular for their characteristics. To have a clear understanding, let us take a look at their comparisons.
| FHSS | DSSS/CDMA |
|---|---|
| Multiple frequencies are used | Single frequency is used |
| Hard to find the users frequency at any instant of time | User frequency, once allotted is always the same |
| Frequency reuse is allowed | Frequency reuse is not allowed |
| The sender need not wait | The sender has to wait if the spectrum is busy |
| Power strength of the signal is high | Power strength of the signal is low |
| It is stronger and penetrates through the obstacles | It is weaker compared to FHSS |
| It is never affected by interference | It can be affected by interference |
| It is cheaper | It is expensive |
| This is the mostly used technique | This technique is not frequently used |
Advantages of Spread Spectrum
Following are the advantages of Spread Spectrum.
- Cross-talk elimination
- Better output with data integrity
- Reduced effect of multipath fading
- Better security
- Reduction in noise
- Co-existence with other systems
- Longer operative distances
- Hard to detect
- Hard to demodulate/decode
- Harder to jam the signals
Although spread spectrum techniques were originally designed for military uses, they are now being used widely as commercial purpose.
