Article Categories
- All Categories
-
 Data Structure
Data Structure
-
 Networking
Networking
-
 RDBMS
RDBMS
-
 Operating System
Operating System
-
 Java
Java
-
 MS Excel
MS Excel
-
 iOS
iOS
-
 HTML
HTML
-
 CSS
CSS
-
 Android
Android
-
 Python
Python
-
 C Programming
C Programming
-
 C++
C++
-
 C#
C#
-
 MongoDB
MongoDB
-
 MySQL
MySQL
-
 Javascript
Javascript
-
 PHP
PHP
-
 Economics & Finance
Economics & Finance
What is Malware?
If your computer or smartphone has suddenly started misbehaving, then it might be because of a Malware program. In this chapter, we would know what Malware is and what are its common types.
What is Malware?
The term Malware is a combination of two words Malicious and Software. It is a common term that is used to denote a software or script that is implicitly designed to create damage to any computer, smartphone, IoT devices, Network, and other programable devices. The damage can be anything like hijacking the browser, locking the essential files, degrading the device's performance, and many such.

The term Malware was coined by Yisrael Rada in 1990, though Malware was already in existence in the form of viruses. Usually, computer users confuse Malware with a virus. However, that is only partially true. The virus is, in fact, one of the types of Malware. It means all viruses are Malware, but not every Malware is a virus.
After infiltrating your system, a Malware program can create havoc, and damages can be beyond monetary.
Different Malware type performs a distinct level of damage. For example, a browser hijacker would take control of your web browser and manipulate its settings to install a rogue extension or to promote an affiliated page. Similarly, Ransomware would encrypt all your system files and documents that can only be decrypted by a decrypting tool or key gained after paying the ransom.
How does Malware get an entry on your device?
Now we will list out some of the most common ways Malware gets infiltrated on your device.
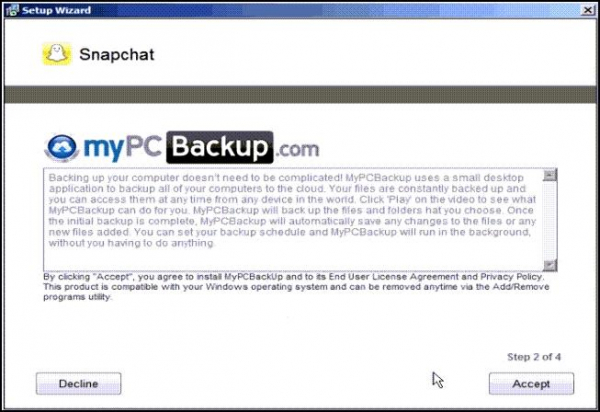
1. Bundled Software
Sometimes when you download a free software program, it might come bundled with an additional application that you might not require. That additional application might be Malware carrying one. Most bundled applications get installed on the system because users forget to decline its installation while installing the primary program.
2. Peer to Peer File Sharing Services
Peer to peer file-sharing services such as torrent are among the top gateways for Malware to enter your system. The files shared through this method travel through many networks and systems, making them vulnerable to malware infection. Moreover, since millions of people use torrents for illegal downloads, cybercriminals usually replace the original files with fake ones containing malicious codes. Therefore, the person downloading it is actually downloading Malware on its device.
3. Clicking on the Intriguing Pop-Ups
While browsing the internet, many times, you might see pop-ups or banner ads with attractive offers that are "too good to be true." Many people in the greed of getting that attractive offer click on the malicious ads, thereby introducing Malware on the system.
4. Downloading Freeware from Unknown Sources
Many people, in anticipation of getting paid software for free, download them from unknown, untrustworthy sources. Such freeware are mostly infected with malicious files that can harm your system in many ways.
5. Spam Emails
Email is one of the oldest mediums to spread malware programs such as viruses and worms. The Malware is usually sent via attachment in the email. The malicious links that lead to Malware downloads are also shared through spam emails.
How to protect your system from Malware?
It is better to prevent Malware from entering the system rather than handling them afterward. Here are a few tips for that.
1. Use a Robust Antimalware Solution
It is better to keep installed a robust antimalware solution on your system to prevent Malware programs from infiltrating your system. Windows users can rely on the in-built Microsoft Defender security suite. However, an added security program would ensure total security.
2. Keep your Software and OS Up to Date
Regularly updating software would fix its vulnerabilities and security loopholes. Similarly, updating the operating system would ensure that the latest security patches are installed on the device and cybercriminals couldn't exploit the vulnerabilities.
3. Backup your Computer
Regular backing up the system would nullify the effect of malware attacks like Ransomware. It would also help you in accidental data loss such as hard disk failure, device stolen, etc.
4. Careful While Opening Email
As already said, emails are the popular way to spread Malware, so it is advised not to open emails from an unknown sender. Even if you opened the mail, don't download the attachments and click on the links.
5. Follow Healthy Browsing practices
To ensure that you don't get Malware while working on the internet, follow healthy browsing practices. That includes:
Avoid clicking on the attractive pop-ups and banner ads.
Avoid downloading from unsecured sources.
Never download anything from torrent sites.


