
- Internet Security - Home
- Internet Security - Overview
- Internet Security - Cookies
- Internet Security - Phishing
- Internet Security - Social Network
- Internet Security - Chrome
- Internet Security - Mozilla
- Internet Security - Explorer
- Internet Security - Safari
- Internet Security - Gaming
- Internet Security - Child Safety
- Internet Security - Spamming
- Internet Security - Chatting
- Internet Security - File Download
- Internet Security - Transactions
- Internet Security - Banking
- Internet Security - e-Commerce
- Internet Security - Certificates
- Internet Security - Email Security
- Internet Security - Identity Theft
- Internet Security - Cybercrime
- Internet Security - Laws
- Internet Security - Checklist
Internet Security - Phishing
Many of us have received similar emails as shown in the following screenshot. They appear as if coming from a genuine source, but in fact if we analyze them a little carefully, they are not. Such emails are called phishing because it depends on the users whether they will follow the procedure that the scammer is requesting or if they (user) will delete that email and be safe.

The links in the email may install malware on the users device or direct them to a malicious website set up to trick them into divulging personal and financial information, such as passwords, account IDs or credit card details. These techniques are too much in use with cybercriminals, as it is far easier to trick someone into clicking a malicious link in the email than trying to break through a computers defenses. Although some phishing emails are poorly written and clearly fake.
How to Detect a Phishing Email?
There are several ways to detect a Phishing Email, some of these methods are discussed here for better understanding.
Spelling and Bad Grammar
Cyber criminals generally make grammar and spelling mistakes because they use dictionary too often to translate in a specific language. If you notice mistakes in an email, it might be a scam.
Links in Email
Links in the email are always with hidden URLs, you don't click on it. Rest your mouse (but don't click) on the link to see if the address matches the link that was typed in the message. In the following example the link reveals the real web address, as shown in the box with the yellow background. The string of cryptic numbers looks nothing like the company's web address.
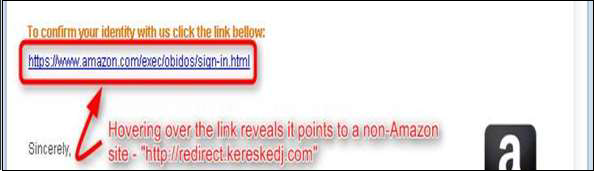
Links also may redirect you to .exe, or zipped files. These are known to spread malicious software.
Threats or They are too Good to be True
Cybercriminals often use threats that your security has been compromised. The above screenshot shows it very well. In our case the subject talking about Suspension.
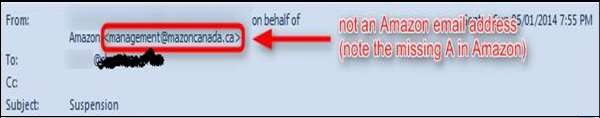
Spoofing Popular Websites or Companies
Scam artists use graphics in email that appear to be connected to legitimate websites, but actually they take you to phony scam sites or legitimate-looking pop-up windows. In our case, there is this email of Amazon which is not a genuine one.
Salutation
Generally, if it is genuine you will have a personalized email like Dear Mr. John, but the cybercriminals, they dont know your name except the email address, so they will use just a part of your email in the salutation or a general salutation.

Got Phished by Mistake?
What to do in case you think that by mistake, you got phished? In such a case, you can take the following measures −
Change the passwords immediately of the account that you think has been hacked.
Check if any money has been withdrawn or any payment done through your account. You can contact your financial institution directly for this.
Contact the authority on whose behalf you got that email. You should also report to your account administrator.
