
- Security Testing Tutorial
- Security Testing - Home
- Security Testing - Overview
- Security Testing - Process
- Security Testing - Malicious Software
- HTTP Protocol Basics
- HTTPS Protocol Basics
- Encoding and Decoding
- Security Testing - Cryptography
- Security Testing - Same Origin Policy
- Security Testing - Cookies
- Hacking Web Applications
- Security Testing - Injection
- Testing Broken Authentication
- Testing Cross Site Scripting
- Insecure Direct Object Reference
- Testing Security Misconfiguration
- Testing Sensitive Data Exposure
- Missing Function Level Access Control
- Cross Site Request Forgery
- Components with Vulnerabilities
- Unvalidated Redirects and Forwards
- Security Testing - Ajax Security
- Testing Security - Web Service
- Security Testing - Buffer Overflows
- Security Testing - Denial of Service
- Testing Malicious File Execution
- Security Testing - Automation Tools
- Security Testing Useful Resources
- Security Testing - Quick Guide
- Security Testing - Useful Resources
- Security Testing - Discussion
Security Testing - Footprinting
Footprinting
Footprinting is the process of gathering the blueprint of a particular system or a network and the devices that are attached to the network under consideration. It is the first step that a penetration tester uses to evaluate the security of a web application.
After footprinting, a penetration tester can understand the pulse of a hacker. It is good to understand the complete system before testing its modules.
Footprinting – Steps
- Information gathering
- Determining the range of the network
- Identifying active machines
- Identifying open ports and access points
- OS fingerprinting
- Fingerprinting services
- Mapping the network
Tools Used in Footprinting
Following are the common set of tools used in footprinting −
- Whois
- SmartWhois
- NsLookup
- Sam Spade
Other Techniques Used in Footprinting
Footprinting may also involve collecting information such as −
- Company contact names, email addresses, and phone numbers
- Company deals and other parties involved
- News on mergers and acquisitions
- Links to other company-related sites
- Company's privacy policies
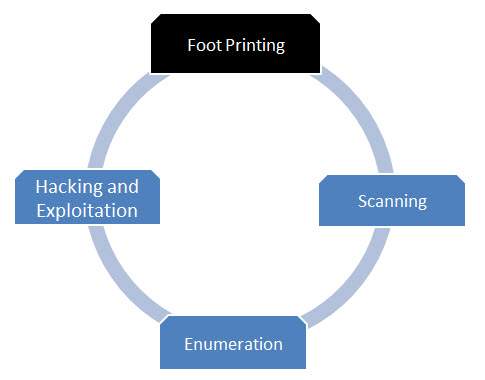
Flow Diagram
Advertisements