- Basics of Computer Science - Home
- Fundamental Concept
- Role of Computer in Today’s World
- Computer System
- Programming Languages
- Hardware and Software
- Analog and Digital
- Operating System
- Internet
- Types of Computer
- Computer Networking Terminology
- Computer Applications
- Generations of Computer
- Data Processing
- Computer Networking
- Computer Related Jobs
- Electronic Commerce
- Software Programming
- Algorithm Flowchart
- Extranet
- Mobile Computer
- Windows Desktop Elements
- Computer Multimedia
- Computer Security
- Computer Threat
- Computer Virus
- Computer Science: Abbreviations
- Computer Science: Development
- Computer Science: Innovators
- Short-cut Keys
Basics of Computer Science - Security
Advancement of computer technology has radically changed the world; resultantly, most of the works whether it is matter of nations security system or buying a shoe online everything depends on computer.
Such increased dependency also raises the issue of security, as most of the data is now stored in the computer system.

Your computer systems store various sorts of data and hence if it is not secured, then you might be in for a big trouble.
Why Do We Computer Security?
Let us now see why do we need Computer security. It is required for the following major reasons −
To prevent damage of the hardware.
To prevent theft or damage of the installed software.
To prevent theft or damage of stored data and information.
To prevent the disruption of service.
Likewise, security system keeps the computer system safe by protecting the installed software and the stored data (information).
Protection of Data and Information
Following are the important steps to protect data −
- Make backup of all your important files.
- Keep your system virus by using anti-virus software.
- Keep updating your computer system.
- Run disk defragmenter and disk cleanup on certain interval of time.
- Use a firewall.
- Use anti-spyware software.
Further, if you use internet, then you need to take greater precaution. Consider the following points to understand the precautions that need to be taken −
Do not click on any link that you dont know (as it may be dangerous for your computer - virus attack).
Do not open unauthorized an unlawful website (it may damage your computer system).
Do not download unsolicited data from unknown website.
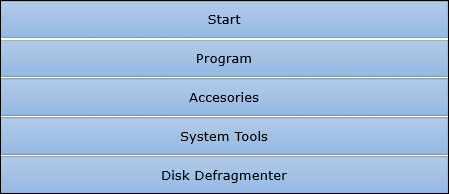
What is Defragmentation?
Frequent saving and deleting of file (data) from the hard disk creates problems in performance and also reduce the space; therefore, defragmentation again clean-up the drive and restore the system to run smoothly.
Following are the simple steps of defragmentation −
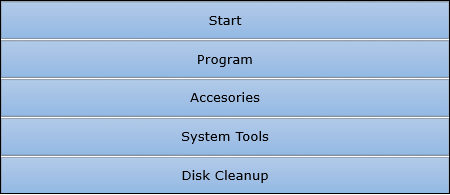
Disk Cleanup
While browsing websites (on internet), many of the files get stored in the hard disk automatically (actually these stored files later help to reopen the website faster); besides some other cookies also get stored in the hard disk. All these stored files create problem along with eating space.
So, disk cleanup process cleans all these files and releases the space occupied by these unwanted files.
Following are the simple steps of disk cleanup −