
- Python - Home
- Python - Overview
- Python - History
- Python - Features
- Python vs C++
- Python - Hello World Program
- Python - Application Areas
- Python - Interpreter
- Python - Environment Setup
- Python - Virtual Environment
- Python - Basic Syntax
- Python - Variables
- Python - Private Variables
- Python - Data Types
- Python - Type Casting
- Python - Unicode System
- Python - Literals
- Python - Operators
- Python - Arithmetic Operators
- Python - Comparison Operators
- Python - Assignment Operators
- Python - Logical Operators
- Python - Bitwise Operators
- Python - Membership Operators
- Python - Identity Operators
- Python - Walrus Operator
- Python - Operator Precedence
- Python - Comments
- Python - User Input
- Python - Numbers
- Python - Booleans
- Python - Floating Points
- Python - Control Flow
- Python - Decision Making
- Python - If Statement
- Python - If else
- Python - Nested If
- Python - Conditional User Inputs
- Python - Match-Case Statement
- Python - Loops
- Python - for Loops
- Python - for-else Loops
- Python - While Loops
- Python - break Statement
- Python - continue Statement
- Python - pass Statement
- Python - Nested Loops
- Python Functions & Modules
- Python - Functions
- Python - Default Arguments
- Python - Keyword Arguments
- Python - Keyword-Only Arguments
- Python - Positional Arguments
- Python - Positional-Only Arguments
- Python - Arbitrary Arguments
- Python - Variables Scope
- Python - Function Annotations
- Python - Modules
- Python - Packing and Unpacking
- Python - Built in Functions
- Python Strings
- Python - Strings
- Python - Slicing Strings
- Python - Modify Strings
- Python - String Concatenation
- Python - String Formatting
- Python - Escape Characters
- Python - String Methods
- Python - String Exercises
- Python Lists
- Python - Lists
- Python - Access List Items
- Python - Change List Items
- Python - Add List Items
- Python - Remove List Items
- Python - Loop Lists
- Python - List Comprehension
- Python - Sort Lists
- Python - Copy Lists
- Python - Join Lists
- Python - List Methods
- Python - List Exercises
- Python Tuples
- Python - Tuples
- Python - Access Tuple Items
- Python - Update Tuples
- Python - Unpack Tuples
- Python - Loop Tuples
- Python - Join Tuples
- Python - Tuple Methods
- Python - Namedtuple
- Python - Tuple Exercises
- Python Sets
- Python - Sets
- Python - Access Set Items
- Python - Add Set Items
- Python - Remove Set Items
- Python - Loop Sets
- Python - Join Sets
- Python - Copy Sets
- Python - Set Operators
- Python - Set Methods
- Python - Set Exercises
- Python Dictionaries
- Python - Dictionaries
- Python - Access Dictionary Items
- Python - Change Dictionary Items
- Python - Add Dictionary Items
- Python - Remove Dictionary Items
- Python - Dictionary View Objects
- Python - Loop Dictionaries
- Python - Copy Dictionaries
- Python - Nested Dictionaries
- Python - Dictionary Methods
- Python - Dictionary Exercises
- Python Arrays
- Python - Arrays
- Python - Access Array Items
- Python - Add Array Items
- Python - Remove Array Items
- Python - Loop Arrays
- Python - Copy Arrays
- Python - Reverse Arrays
- Python - Sort Arrays
- Python - Join Arrays
- Python - Array Methods
- Python - Array Exercises
- Python File Handling
- Python - File Handling
- Python - Write to File
- Python - Read Files
- Python - Renaming and Deleting Files
- Python - Directories
- Python - File Methods
- Python - OS File/Directory Methods
- Python - OS Path Methods
- Object Oriented Programming
- Python - OOPs Concepts
- Python - Classes & Objects
- Python - Class Attributes
- Python - Class Methods
- Python - Static Methods
- Python - Constructors
- Python - Access Modifiers
- Python - Inheritance
- Python - Multiple Inheritance
- Python - Multilevel Inheritance
- Python - Polymorphism
- Python - Method Overriding
- Python - Method Overloading
- Python - Dynamic Binding
- Python - Dynamic Typing
- Python - Abstraction
- Python - Encapsulation
- Python - Interfaces
- Python - Packages
- Python - Inner Classes
- Python - Anonymous Class and Objects
- Python - Singleton Class
- Python - Wrapper Classes
- Python - Enums
- Python - Reflection
- Python - Data Classes
- Python Errors & Exceptions
- Python - Syntax Errors
- Python - Exceptions
- Python - try-except Block
- Python - try-finally Block
- Python - Raising Exceptions
- Python - Exception Chaining
- Python - Nested try Block
- Python - User-defined Exception
- Python - Logging
- Python - Assertions
- Python - Warnings
- Python - Built-in Exceptions
- Python - Debugger (PDB)
- Python Multithreading
- Python - Multithreading
- Python - Thread Life Cycle
- Python - Creating a Thread
- Python - Starting a Thread
- Python - Joining Threads
- Python - Naming Thread
- Python - Thread Scheduling
- Python - Thread Pools
- Python - Main Thread
- Python - Thread Priority
- Python - Daemon Threads
- Python - Synchronizing Threads
- Python Synchronization
- Python - Inter-thread Communication
- Python - Thread Deadlock
- Python - Interrupting a Thread
- Python Networking
- Python - Networking
- Python - Socket Programming
- Python - URL Processing
- Python - Generics
- Python Libraries
- NumPy Tutorial
- Pandas Tutorial
- SciPy Tutorial
- Matplotlib Tutorial
- Django Tutorial
- OpenCV Tutorial
- Python Miscellenous
- Python - Date & Time
- Python - Maths
- Python - Iterators
- Python - Generators
- Python - Generator Expressions
- Python - Lambda Expressions
- Python - Closures
- Python - Decorators
- Python - Recursion
- Python - Reg Expressions
- Python - PIP
- Python - Database Access
- Python - Weak References
- Python - Serialization
- Python - Templating
- Python - Output Formatting
- Python - Performance Measurement
- Python - Data Compression
- Python - CGI Programming
- Python - XML Processing
- Python - GUI Programming
- Python - Command-Line Arguments
- Python - Docstrings
- Python - JSON
- Python - Sending Email
- Python - Further Extensions
- Python - Tools/Utilities
- Python - Odds and Ends
- Python - GUIs
- Python Advanced Concepts
- Python - Abstract Base Classes
- Python - Custom Exceptions
- Python - Higher Order Functions
- Python - Object Internals
- Python - Memory Management
- Python - Metaclasses
- Python - Metaprogramming with Metaclasses
- Python - Mocking and Stubbing
- Python - Monkey Patching
- Python - Signal Handling
- Python - Type Hints
- Python - Automation Tutorial
- Python - Humanize Package
- Python - Context Managers
- Python - Coroutines
- Python - Descriptors
- Python - Diagnosing and Fixing Memory Leaks
- Python - Immutable Data Structures
- Python - Domain Specific Language (DSL)
- Python - Data Model
- Python Useful Resources
- Python - Questions & Answers
- Python - Interview Questions & Answers
- Python - Online Quiz
- Python - Quick Guide
- Python - Reference
- Python - Cheatsheet
- Python - Projects
- Python - Useful Resources
- Python - Discussion
- Python Compiler
- NumPy Compiler
- Matplotlib Compiler
- SciPy Compiler
How to Build a Password Manager in Python
This password manager application will enable the storage and protection of passwords by encrypting them in an organized manner.
This password manager is created using Python and the user interface has been created using Tkinter while ensuring password security using the cryptography library. One of the features of the application is to save and show passwords safely and securely with the help of the strong encryptions.
Installations
First follow these installation steps −
1. Install Python
Ensure you have Python 3.11 or later installed. Download and install it. Read more − Python Environment Setup.
2. Install Required Libraries
Open a terminal or command prompt and install the libraries using pip −
pip install cryptography
Explanation of Password Manager Components
The password manager application consists of several key components: The password manager application consists of several key components −
1. Key Generation and Management
The last is generate_key() function that causes generation of a new encryption key.
This function load_key()as a default function to load an existing key from file if it is available otherwise it creates a new one.
2. Encryption and Decryption
Passwords are encrypted using the Fernet encryption algorithm which is done by the encrypt_message() function while decryption is done using the decrypt_message() function before presentation.
3. Save Password
The save_password() function takes string input from the user for service, username and the password, and then encrypts it before putting it into the JSON file. It deals with file operation and modified the data which is already exist.
4. View Passwords
The view_passwords() function reads encrypted passwords from the JSON file then decrypts them and displays them for the user's convenience.
5. Graphical User Interface (GUI)
Tkinter library is used to implement a basic User interface that consists of entry widgets for Service, Username, and Password and buttons for save and show password.
Read More: Python GUI Programming
Python Code to Build a Password Manager
import tkinter as tk
from tkinter import messagebox
from cryptography.fernet import Fernet
import os
import json
# Key generation and encryption setup
def generate_key():
return Fernet.generate_key()
def load_key():
if os.path.exists("secret.key"):
with open("secret.key", "rb") as key_file:
return key_file.read()
else:
key = generate_key()
with open("secret.key", "wb") as key_file:
key_file.write(key)
return key
def encrypt_message(message, key):
f = Fernet(key)
encrypted_message = f.encrypt(message.encode())
return encrypted_message
def decrypt_message(encrypted_message, key):
f = Fernet(key)
decrypted_message = f.decrypt(encrypted_message).decode()
return decrypted_message
# Initialize the key
key = load_key()
# Application functions
def save_password():
service = service_entry.get()
username = username_entry.get()
password = password_entry.get()
if not service or not username or not password:
messagebox.showwarning("Input Error", "Please fill all fields.")
return
encrypted_password = encrypt_message(password, key)
new_data = {service: {"username": username, "password": encrypted_password}}
if os.path.exists("passwords.json"):
with open("passwords.json", "r") as file:
try:
existing_data = json.load(file)
except (json.JSONDecodeError, TypeError):
existing_data = {}
existing_data.update(new_data)
else:
existing_data = new_data
# Ensure all values in existing_data are serializable
for service, info in existing_data.items():
if isinstance(info.get("password"), bytes):
info["password"] = info["password"].decode() # Convert bytes to string for serialization
with open("passwords.json", "w") as file:
try:
json.dump(existing_data, file, indent=4)
except TypeError as e:
messagebox.showerror("Serialization Error", f"Error serializing data: {e}")
service_entry.delete(0, tk.END)
username_entry.delete(0, tk.END)
password_entry.delete(0, tk.END)
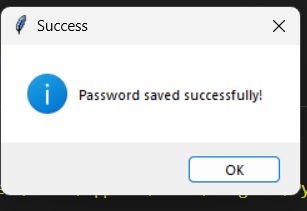
messagebox.showinfo("Success", "Password saved successfully!")
def view_passwords():
if os.path.exists("passwords.json"):
with open("passwords.json", "r") as file:
try:
data = json.load(file)
except json.JSONDecodeError:
data = {}
result = ""
if data:
for service, info in data.items():
username = info.get("username", "N/A")
password = info.get("password", b"")
decrypted_password = decrypt_message(password.encode(), key)
result += f"Service: {service}\nUsername: {username}\nPassword: {decrypted_password}\n\n"
else:
result = "No passwords stored yet."
messagebox.showinfo("Stored Passwords", result)
else:
messagebox.showinfo("No Data", "No passwords stored yet.")
# GUI setup
root = tk.Tk()
root.title("Password Manager")
tk.Label(root, text="Service").grid(row=0, column=0, padx=10, pady=10)
tk.Label(root, text="Username").grid(row=1, column=0, padx=10, pady=10)
tk.Label(root, text="Password").grid(row=2, column=0, padx=10, pady=10)
service_entry = tk.Entry(root, width=50)
service_entry.grid(row=0, column=1, padx=10, pady=10)
username_entry = tk.Entry(root, width=50)
username_entry.grid(row=1, column=1, padx=10, pady=10)
password_entry = tk.Entry(root, width=50, show="*")
password_entry.grid(row=2, column=1, padx=10, pady=10)
tk.Button(root, text="Save Password", command=save_password).grid(row=3, column=0, columnspan=2, pady=10)
tk.Button(root, text="View Passwords", command=view_passwords).grid(row=4, column=0, columnspan=2, pady=10)
root.mainloop()
Output
First you have to write your Service, username, password.

Then you have to click save button for save this −
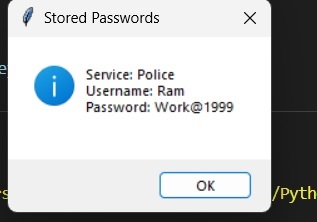
After that you can view the password that you saved −
Again you can create password, username and service −

After saving the password, click View Password, and you will see both usernames that you created previously −
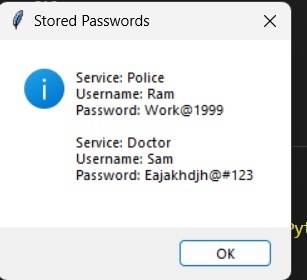
That all passwords will be saved in a JSON file −

Conclusion
This password manager created with the help of Python can be the useful tool to handle passwords with security issues. Using simple encryption, and a friendly graphical user interface it only allows access to authorized users while data security is maintained. As it seen from the installation instructions and source code, users can run their own password manager and improve their online safety.