
- Cloud Computing Basics
- Cloud Computing - Home
- Cloud Computing - Overview
- Cloud Computing - Evolution
- Cloud Computing - Characteristics
- Cloud Computing - Advantages
- Cloud Computing - Planning
- Cloud Computing - Technologies
- Cloud Computing - Architecture
- Cloud Computing - Infrastructure
- Cloud Deployment Models
- Public Cloud Model
- Private Cloud Model
- Hybrid Cloud Model
- Community Cloud Model
- Cloud Service Models
- Infrastructure Service
- Platform Service
- Software ervice
- Identity Service
- Network Service
- IaaS, PaaS, and SaaS
- Cloud Virtualization
- Cloud Computing Virtualization
- Server Virtualization
- Data Virtualization
- Software Virtualization
- Storage Virtualization
- Network Virtualization
- Linux Virtualization
- Cloud Advanced Concepts
- Cloud Computing - Management
- Cloud Computing - Data Storage
- Cloud Computing - Security
- Cloud Computing - Operation
- Cloud Computing - Applications
- Cloud Computing - Providers
- Cloud Computing - Challenges
- Cloud Computing - Mobile
- Google Cloud Platform
- Cloud Computing - Multitenancy
- Hypervisor Security
- Cloud Computing - Principles
- Security Architecture
- Fault Tolerance
- Cloud Computing - Resiliency
- Service Level Agreements
- Cloud Networking
- Server Consolidation
- Cloud Computing - Scaling
- Autoscaling vs Load Balancer
- Scalability and Elasticity
- Cloud Bursting vs Cloud Scaling
- Resource Pooling
- Load Balancing
- Security Threats in Implementation SaaS
- Cloud Computing - Data Center
- Cloud Computing - Aneka
- Cloud Computing - Rapid Elasticity
- Cloud Computing - Xaas
- Cloud Computing - DaaS
- Cloud Computing - CaaS
- Cloud Computing - Roots
- Cloud Hosting vs Web Hosting
- Colocation vs Cloud
- iCloud Drive vs Dropbox
- SAP vs Oracle Cloud
- Cloud Computing vs Data Science
- Cloud Integration Platform
- Onedrive and iCloud
- Private Cloud and On-premise
- What is Cloudcraft
- Bitbucket Cloud API
- Akamai vs Cloudflare
- AWS CloudWatch vs Datadog
- Cloud Burst
- Cloudflare vs CloudFront
- Elastic Cloud on Azure
- Cloud Useful Resources
- Cloud Computing - Quick Guide
- Cloud Computing - Useful Resources
- Cloud Computing - Discussion
Cloud Computing Challenges
Cloud computing, anemergent technology, has placed many challenges in different aspects of data and information handling. Some of these are shown in the following diagram:
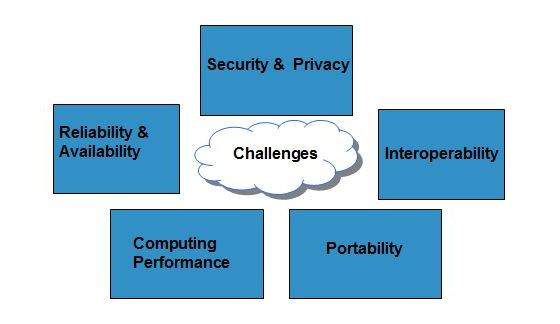
Security and Privacy
Security and Privacy of information is the biggest challenge to cloud computing. Security and privacy issues can be overcome by employing encryption, security hardware and security applications.
Portability
This is another challenge to cloud computing that applications should easily be migrated from one cloud provider to another. There must not be vendor lock-in. However, it is not yet made possible because each of the cloud provider uses different standard languages for their platforms.
Interoperability
It means the application on one platform should be able to incorporate services from the other platforms. It is made possible via web services, but developing such web services is very complex.
Computing Performance
Data intensive applications on cloud requires high network bandwidth, which results in high cost. Low bandwidth does not meet the desired computing performance of cloud application.
Reliability and Availability
It is necessary for cloud systems to be reliable and robust because most of the businesses are now becoming dependent on services provided by third-party.
