
- Cloud Computing Basics
- Cloud Computing - Home
- Cloud Computing - Overview
- Cloud Computing - Evolution
- Cloud Computing - Characteristics
- Cloud Computing - Advantages
- Cloud Computing - Planning
- Cloud Computing - Technologies
- Cloud Computing - Architecture
- Cloud Computing - Infrastructure
- Cloud Deployment Models
- Public Cloud Model
- Private Cloud Model
- Hybrid Cloud Model
- Community Cloud Model
- Cloud Service Models
- Infrastructure Service
- Platform Service
- Software ervice
- Identity Service
- Network Service
- IaaS, PaaS, and SaaS
- Cloud Virtualization
- Cloud Computing Virtualization
- Server Virtualization
- Data Virtualization
- Software Virtualization
- Storage Virtualization
- Network Virtualization
- Linux Virtualization
- Cloud Advanced Concepts
- Cloud Computing - Management
- Cloud Computing - Data Storage
- Cloud Computing - Security
- Cloud Computing - Operation
- Cloud Computing - Applications
- Cloud Computing - Providers
- Cloud Computing - Challenges
- Cloud Computing - Mobile
- Google Cloud Platform
- Cloud Computing - Multitenancy
- Hypervisor Security
- Cloud Computing - Principles
- Security Architecture
- Fault Tolerance
- Cloud Computing - Resiliency
- Service Level Agreements
- Cloud Networking
- Server Consolidation
- Cloud Computing - Scaling
- Autoscaling vs Load Balancer
- Scalability and Elasticity
- Cloud Bursting vs Cloud Scaling
- Resource Pooling
- Load Balancing
- Security Threats in Implementation SaaS
- Cloud Computing - Data Center
- Cloud Computing - Aneka
- Cloud Computing - Rapid Elasticity
- Cloud Computing - Xaas
- Cloud Computing - DaaS
- Cloud Computing - CaaS
- Cloud Computing - Roots
- Cloud Hosting vs Web Hosting
- Colocation vs Cloud
- iCloud Drive vs Dropbox
- SAP vs Oracle Cloud
- Cloud Computing vs Data Science
- Cloud Integration Platform
- Onedrive and iCloud
- Private Cloud and On-premise
- What is Cloudcraft
- Bitbucket Cloud API
- Akamai vs Cloudflare
- AWS CloudWatch vs Datadog
- Cloud Burst
- Cloudflare vs CloudFront
- Elastic Cloud on Azure
- Cloud Useful Resources
- Cloud Computing - Quick Guide
- Cloud Computing - Useful Resources
- Cloud Computing - Discussion
Cloud Computing Security
Security in cloud computing is a major concern. Data in cloud should be stored in encrypted form. To restrict client from accessing the shared data directly, proxy and brokerage services should be employed.
Security Planning
Before deploying a particular resource to cloud, one should need to analyze several aspects of the resource such as:
Select resource that needs to move to the cloud and analyze its sensitivity to risk.
Consider cloud service models such asIaaS, PaaS, andSaaS. These models require customer to be responsible for security at different levels of service.
Consider the cloud type to be used such aspublic, private, communityorhybrid.
Understand the cloud service provider's system about data storage and its transfer into and out of the cloud.
The risk in cloud deployment mainly depends upon the service models and cloud types.
Understanding Security of Cloud
Security Boundaries
A particular service model defines the boundary between the responsibilities of service provider and customer.Cloud Security Alliance (CSA)stack model defines the boundaries between each service model and shows how different functional units relate to each other. The following diagram shows the CSA stack model:
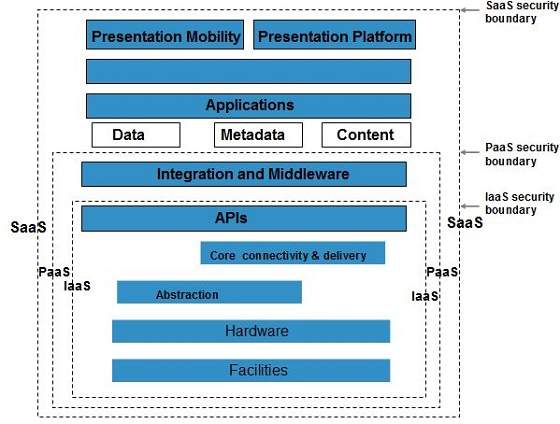
Key Points to CSA Model
IaaS is the most basic level of service with PaaS and SaaS next two above levels of services.
Moving upwards, each of the service inherits capabilities and security concerns of the model beneath.
IaaS provides the infrastructure, PaaS provides platform development environment, and SaaS provides operating environment.
IaaS has the least level of integrated functionalities and integrated security while SaaS has the most.
This model describes the security boundaries at which cloud service provider's responsibilities end and the customer's responsibilities begin.
Any security mechanism below the security boundary must be built into the system and should be maintained by the customer.
Although each service model has security mechanism, the security needs also depend upon where these services are located, in private, public, hybrid or community cloud.
Understanding Data Security
Since all the data is transferred using Internet, data security is of major concern in the cloud. Here are key mechanisms for protecting data.
- Access Control
- Auditing
- Authentication
- Authorization
All of the service models should incorporate security mechanism operating in all above-mentioned areas.
Isolated Access to Data
Since data stored in cloud can be accessed from anywhere, we must have a mechanism to isolate data and protect it from clients direct access.
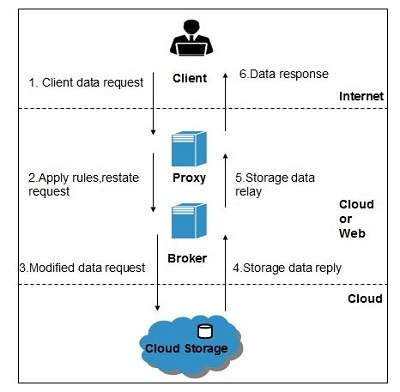
Brokered Cloud Storage Accessis an approach for isolating storage in the cloud. In this approach, two services are created:
A broker with full access to storage but no access to client.
A proxy with no access to storage but access to both client and broker.
Working Of Brokered Cloud Storage Access System
When the client issues request to access data:
The client data request goes to the external service interface of proxy.
The proxy forwards the request to the broker.
The broker requests the data from cloud storage system.
The cloud storage system returns the data to the broker.
The broker returns the data to proxy.
Finally the proxy sends the data to the client.
All of the above steps are shown in the following diagram:
Encryption
Encryption helps to protect data from being compromised. It protects data that is being transferred as well as data stored in the cloud. Although encryption helps to protect data from any unauthorized access, it does not prevent data loss.