Data Structure
Data Structure Networking
Networking RDBMS
RDBMS Operating System
Operating System Java
Java MS Excel
MS Excel iOS
iOS HTML
HTML CSS
CSS Android
Android Python
Python C Programming
C Programming C++
C++ C#
C# MongoDB
MongoDB MySQL
MySQL Javascript
Javascript PHP
PHP
- Selected Reading
- UPSC IAS Exams Notes
- Developer's Best Practices
- Questions and Answers
- Effective Resume Writing
- HR Interview Questions
- Computer Glossary
- Who is Who
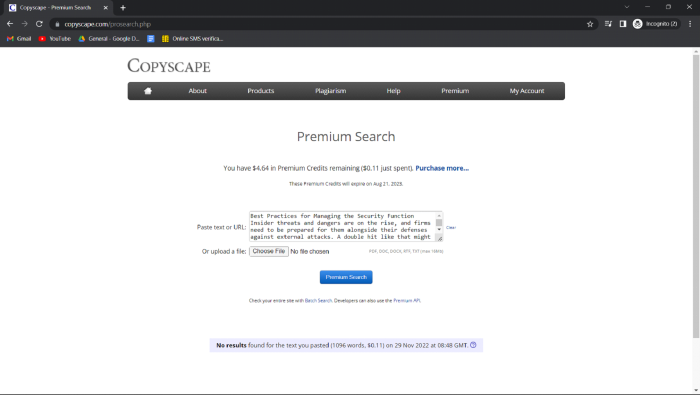
Best Practices for Managing the Security Function
Insider threats and dangers are on the rise, and firms need to be prepared for them alongside their defenses against external attacks. A double hit like that might have devastating results and can be fatal for a small company.
The average cost of a cyber incident to a company is $200,000, according to statistics, implying that some businesses could go bankrupt within six months if they experience even a moderate amount of cyber activity.
To assist you in strengthening your company's cyber defense and stopping breaches, we've compiled a list of eight recommended practices for managing network security.
1. Adopt a Formal Information Security Governance Framework
The success of any network security plan hinges on the implementation of a comprehensive information security governance framework.
This framework will assist your team in becoming adept at recognizing attacks, conducting in-depth investigations into them, and taking preventative measures in response to them.
The term "cyber security program" describes your company's approach to developing, implementing, and managing a comprehensive set of rules and practices designed to protect against cyber threats. Governance over information security ensures that your business follows best practices for handling sensitive data.
For instance, businesses must have secure data retention policies that align with their industry standards and store all email, text message, and social media correspondence in an easily searchable, immutable format. Information security governance controls all of this and ensures compliance with current privacy and security regulations.
With such a thorough commitment to compliance, you can rest assured that your data security measures will pass any audits that may be conducted.
2. Prevent Data Loss
Employee trust should not be placed above all else when it comes to network security.
Employee loyalty is appreciated, but it won't help prevent the theft of sensitive information from within the company. New research shows a 40% increase in data exposure instances between 2020 and 2021, demonstrating the tremendous damage caused by employees who accidentally release or even steal data.
Data loss prevention (DLP) software is essential because it can monitor your network and alert you if an employee is transferring sensitive data to an unauthorized machine or making an unauthorized copy.
Through the DLP, you may restrict access to sensitive information and keep tabs on the actions of your staff, partners, and vendors to forestall any unintentional or malicious disclosures.
3. Perform Regular Data Backups
Losing any of the vast volumes of data that businesses acquire, produce, and the store might be disastrous. Data backups are an additional layer of protection against loss of information and a solid network security practice.
The security of your data against ransomware, accidental deletion, and corruption is ensured by maintaining regular backups.
One of the finest network security management practices is to make at least three copies of your files, one of which will be stored off-site, so that your important company data is protected from any of these incidents. Your data is safe when backed up on the cloud, but you should still keep a copy of it locally, just in case.
4. Watch Out for Social Engineering Attacks
Social engineering is a complex and covert technique used by cybercriminals to steal sensitive information, such as usernames, passwords, and banking details.
The problem is that social engineering doesn't use the usual hacking methods to steal sensitive information. Human mistake is inevitable, making it hard to prevent even with your company's data protection standards and cutting-edge software.
Social engineering is a technique used by hackers to gain the trust of their targets in order to steal information from their targets without their knowledge. Threats of this nature may arrive via email, phone, or any other means of contact.
As there are currently no technologies designed specifically to counter social engineering, this section will focus on one of the most useful recommendations for securing your computer network.
5. Educate Your Employees
Social engineering assaults and other dangers which exploit employees' lack of technical knowledge, can be mitigated by proper education and training.
Keeping your staff informed about the most recent developments in the fight against cybercrime is crucial as the sophistication of cyber threats continues to rise, and more people are at risk of falling for fraud.
Don't take it for granted that your staff already knows how to keep their systems secure; instead, provide them with training on the following ?
Building secure passwords,
Learn the definition of phishing and the characteristics of a phishing email.
The workings of potentially harmful applications
Regulations, guidelines, and processes for data security.
6. Onboard New Employees and Third-Party Users
Best practices for managing network security should be part of the onboarding process for all new employees, vendors, and contractors.
This will eliminate any concerns you may have had regarding their familiarity with cyber security threats and procedures.
In addition, employment agreements should detail applicable rules and procedures that spell out each party's responsibilities in detail. It is crucial to the safety of your business that everyone be on the same page with regard to IT security procedures.
7. Keep Your Software Up to Date
The failure to constantly update your software is a very serious error.
Keep in mind that hackers are always developing new methods and tools to find security holes in systems and breach into corporate networks.
Patching your system and updating your software on a regular basis will protect it from these dangers.
8. Build an Incident Response Plan
A system breach is possible even if you've implemented all the precautions we've mentioned so far.
Having a pre-made plan for handling an occurrence can help avert disaster. If you and your staff are able to react fast, you can lessen the impact of the breach and get the recovery process underway sooner rather than later.
Conclusion
You can see now how broad the scope of data protection is. Maintaining an up-to-date security toolkit and employing sound policy management is essential for every competent network administrator or security expert. The sheer volume of regulations to uphold and software to maintain might make this task appear insurmountable to any security team.
One difficulty in data security is reducing the burden on end users. Antivirus software, personal firewalls, and threat detection systems all have the negative side effect of reducing available resources for critical user operations. As a result, it's important to consider a program's memory usage and footprint size while making a decision on how to best secure the end-user experience.