
- Security Testing Tutorial
- Security Testing - Home
- Security Testing - Overview
- Security Testing - Process
- Security Testing - Malicious Software
- HTTP Protocol Basics
- HTTPS Protocol Basics
- Encoding and Decoding
- Security Testing - Cryptography
- Security Testing - Same Origin Policy
- Security Testing - Cookies
- Hacking Web Applications
- Security Testing - Injection
- Testing Broken Authentication
- Testing Cross Site Scripting
- Insecure Direct Object Reference
- Testing Security Misconfiguration
- Testing Sensitive Data Exposure
- Missing Function Level Access Control
- Cross Site Request Forgery
- Components with Vulnerabilities
- Unvalidated Redirects and Forwards
- Security Testing - Ajax Security
- Testing Security - Web Service
- Security Testing - Buffer Overflows
- Security Testing - Denial of Service
- Testing Malicious File Execution
- Security Testing - Automation Tools
- Security Testing Useful Resources
- Security Testing - Quick Guide
- Security Testing - Useful Resources
- Security Testing - Discussion
Security Testing - Exploitation
Exploitation
Exploitation is the last phase where a security tester actively exploits the security weaknesses present in the system under consideration. Once the attack is successful, it is possible to penetrate more systems in the domain, because the penetration testers then have the access to more potential targets that were not available before.
Techniques Used in Exploitation
The types of exploitation are segregated into three different categories −
Attack Against WEB-SERVERS
- SQL Injection
- Cross-site Scripting
- Code Injection
- Session Hijacking
- Directory Traversal
Attack against NETWORKS
- Man in the Middle Attack
- Spoofing
- Firewall Traversal
- WLAN
- ARP Poisoning
Attack against SERVICES
- Buffer Overflows
- Format Strings
- Dos
- Authentication flaws
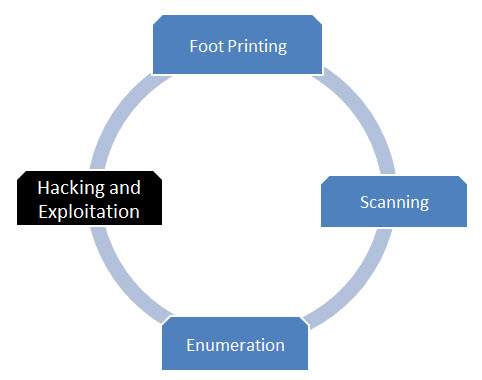
Flow Diagram
Advertisements
To Continue Learning Please Login