
- SAP Security - Home
- SAP Security - Overview
- User Authentication & Management
- Network Communication Security
- Protecting Standard Users
- Un-authorizing Logons Protections
- System Authorization Concept
- SAP Security - Unix Platform
- SAP Security - Windows Platform
- SAP Security - Databases
- User Authentication & Single SignOn
- SAP Security - Logon Tickets
Un-authorizing Logons Protections
To implement security in a SAP system, it is required to monitor unsuccessful login in a SAP environment. When someone tries to login to a system using an incorrect password, the system should either lock the username for some time or that session should be terminated after a defined number of attempts.
Various security parameters can be set for unauthorized logon attempts −
- Terminating a Session
- Locking User
- Activating Screen Savers
- Monitoring unsuccessful logon attempts
- Recording logon attempts
Let us now discuss each of these in detail.
Terminating a Session
When there are a multiple number of unsuccessful login attempts made on a single user id, the system ends the session for that user. This should be sent using a Profile parameter − login/fails_to_session_end.
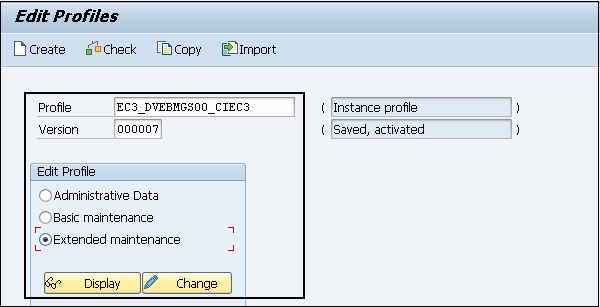
To change the Parameter value, run Transaction RZ10 and select the Profile as shown in the following screenshot. Select Extended Maintenance and click on Display.
Select the parameter that you want to change and click on the Parameter button at the top as shown below.
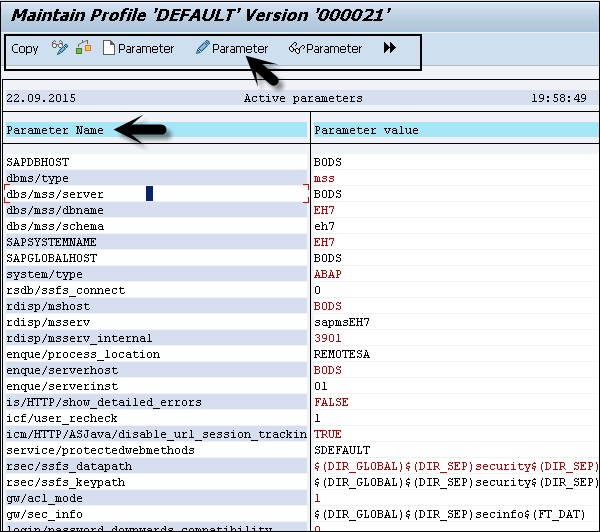
When you click on the Parameter tab, you can change the value of the parameter in a new window. You can also create the new parameter by clicking on the Create (F5) button.
To see the details of this parameter, run Transaction Code: RZ11 and enter the profile name login/fails_to_session_end and the click on Display Document.
Parameter − login/fails_to_session_end
Short text − Number of invalid login attempts until the session ends.
Parameter Description − Number of invalid login attempts that can be made with a user master record until the logon procedure is terminated.
Application Area − Logon
Default Value − 3
Who is permitted to make changes? − Customer
Operating System Restrictions − None
Database System Restrictions − None
Are other parameters affected or dependent? − None
Values allowed − 1 - 99
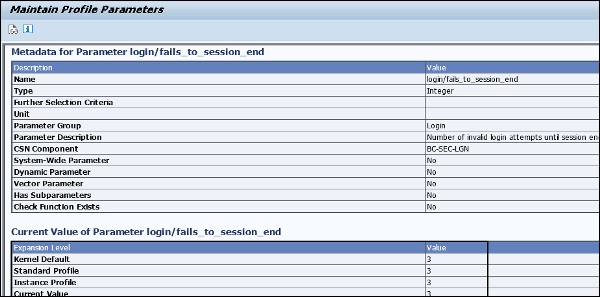
In the above screenshot, you can see value of this parameter is set to 3, i.e. the default value too. After 3 unsuccessful login attempts, session will be terminated for a single user.
Locking User
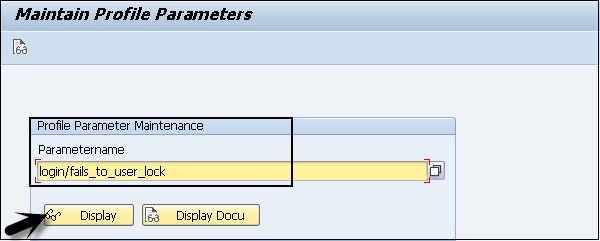
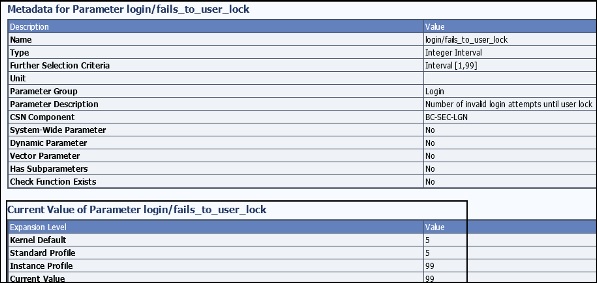
You can also put a check on a specific User Id, if a set number of consecutive unsuccessful attempts to logon is exceeded under a single User Id. Set the number of invalid logon attempts that are allowed in the profile parameter: login/fails_to_user_lock.
It is possible to set a lock on specific User IDs.
Locks are applied on a User Id till midnight. However, it can also be removed manually at any time by a System Administrator.
In a SAP system, you can also set a parameter value that allows lock to be placed on the User Id till they are manually removed. Parameter name: login/failed_user_auto_unlock.
Profile parameter: login/fails_to_user_lock
Every time an incorrect logon password is entered, the failed logon counter for the relevant user master record is increased. The logon attempts can be logged in the Security Audit Log. If the limit specified by this parameter is exceeded, the relevant user is locked. This process is also logged in Syslog.
The lock is no longer valid after the current day is over. (Other Condition −login/failed_user_auto_unlock)
The failed logon counter is reset once the user logs on using the correct password. Logons that are not password-based do not have any effect on the failed logon counter. However, active logon locks are checked for every logon.
Values allowed − 1 99
To see the current value of this parameter, use T-Code: RZ11.
Parameter name − login/failed_user_auto_unlock
Short text − Disable automatic unlocking of locked user at midnight.
Parameter Description − Controls the unlocking of users locked by logging on incorrectly. If the parameter is set to 1, locks that were set due to failed password logon attempts only apply on the same day (as the locking). If the parameter is set to 0, the locks remain in effect.
Application Area − Logon.
Default Value − 0.
Activating Screen Savers
System administrators can also enable screen savers to protect the frontend screen from any unauthorized access. These screensavers can be password protected.
Monitoring Unsuccessful Logon Attempts and Recording Logon Attempts
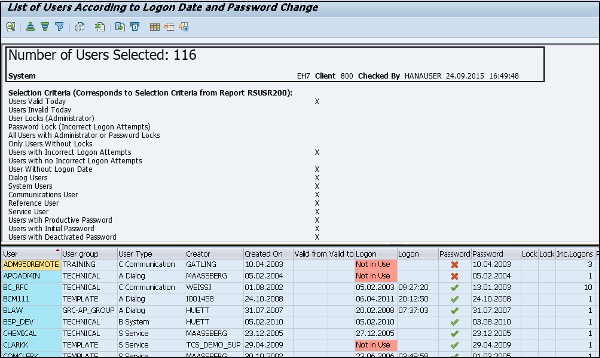
In a SAP system, you can use report RSUSR006 to check if there are users who have tried any unsuccessful logon attempts in the system. This report contains detail about the number of incorrect login attempts by a user and the user locks and you can schedule this report as per your requirement.
Go to ABAP Editor SE38 and enter the report name and then click on EXECUTE.
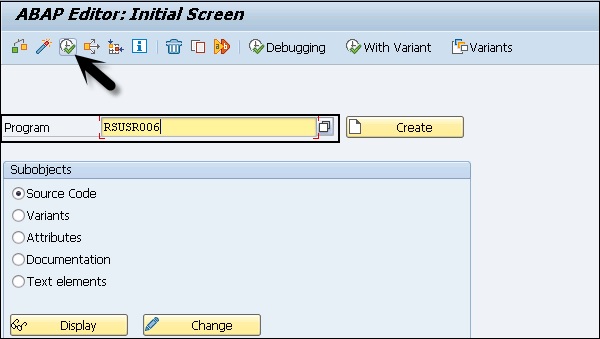
In this report, you have different details like Username, Type, Created On, Creator, Password, Lock and Incorrect Login Details.
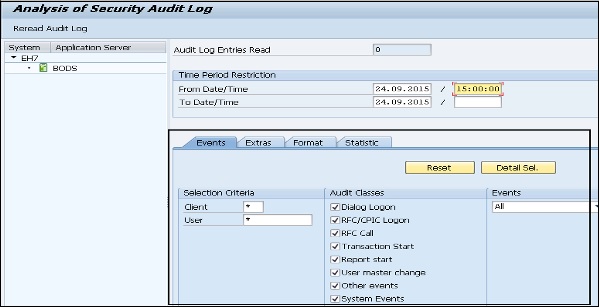
In a SAP system, it is also possible that you use Security Audit Log (transactions SM18, SM19 and SM20) to record all the successful and unsuccessful logon attempts. You can analyze the security audit logs using SM20 transaction, but security audit should be activated in the system to monitor security audit logs.
Logging off Idle Users
When a user is already logged into a SAP system and session is inactive for a specific period, you can also set them to logoff to avoid any unauthorized access.
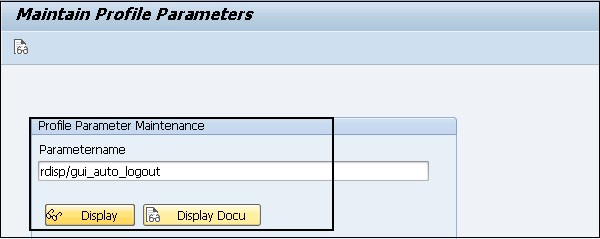
To enable this setting, you need to specify this value in the profile parameter: rdisp/gui_auto_logout.
Parameter Description − You can define that inactive SAP GUI users are automatically logged off from a SAP system after a predefined period. The parameter configures this time. Automatic logoff in the SAP system is deactivated by default (value 0), that is, the users are not logged off even if they do not execute any actions for a longer period.
Values allowed − n [unit], where n >= 0 and Unit = S | M | H | D
To see the current value of parameter, run T-Code: RZ11.

The following table shows you the list of key parameters, their default and permitted value in a SAP system −
| Parameter | Description | Default | Permitted Value |
|---|---|---|---|
| Login/fails_to_session_end | Number of invalid login attempts until session end | 3 | 1-99 |
| Login/fails_to_user_lock | Number of invalid login attempts until user lock | 12 | 1-99 |
| Login/failed_user_auto_unlock | When sets t 1: Locks apply on the day that they are set.They are removed the next day when the user logs on | 1 | 0 or 1 |
| rdisp/gui_auto_output | Maximum idle time for a user in number of seconds | 0(no limit) | unrestricted |
