
- SAP Security - Home
- SAP Security - Overview
- User Authentication & Management
- Network Communication Security
- Protecting Standard Users
- Un-authorizing Logons Protections
- System Authorization Concept
- SAP Security - Unix Platform
- SAP Security - Windows Platform
- SAP Security - Databases
- User Authentication & Single SignOn
- SAP Security - Logon Tickets
SAP Security - Logon Tickets
You can configure the digitally signed SAP logon tickets to configure with a Single Sign-On to access integrated applications in a SAP environment. You can configure a portal to issue SAP logon tickets to the users and the users need to authenticate this system for initial access. When SAP logon tickets are issued to users they are saved in web browsers and allows the user to login to different systems with use of SSO.
In an ABAP application server, there are two different types of Logon ticket that can be configured −
Logon Tickets − These tickets allow web based access using SSO method.
Authentication Assertion Tickets − These tickets are used for system to system communication.
To configure SAP logon tickets, the following parameters should be set in the User profile.
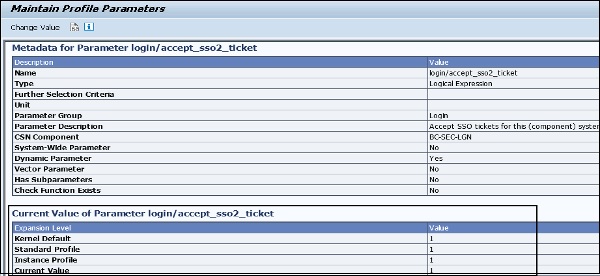
login/accept_sso2_ticket
You can use Single Sign-On (SSO) tickets to allow an SSO between SAP systems and even beyond the non-SAP systems. An SSO ticket can be a logon ticket or an assertion ticket. The logon ticket is transferred as a cookie with the name MYSAPSSO2. The assertion ticket is transferred as an HTTP header variable with the name MYSAPSSO2.
Note − This requires additional configuration steps for issuing and accepting the systems. The SSO component systems should permit logon by an SSO ticket (login/accept_sso2_ticket = 1).
If only the procedure (X.509 client certificate) is used for a Single Sign-On, or if you do not want to use the Single Sign-On for this system, you can deactivate this logon by SSO ticket (login/accept_sso2_ticket = 0).
To set the parameter, use Transaction RZ11
Values allowed − 0 / 1
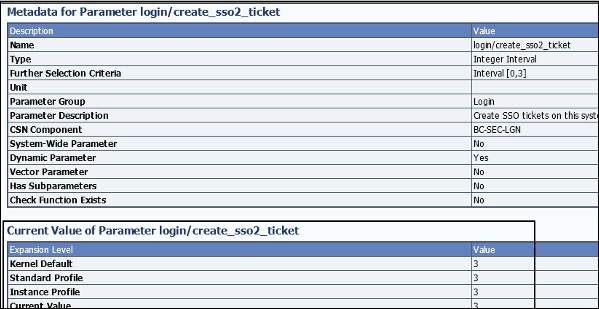
login/create_sso2_ticket
You can use the Single Sign-On (SSO) tickets to allow an SSO between SAP systems and even beyond to non-SAP systems. An SSO ticket can be a logon ticket or an assertion ticket. The logon ticket is transferred as a cookie with the name MYSAPSSO2. The assertion ticket is transferred as an HTTP header variable with the name MYSAPSSO2.
Note − This requires additional configuration steps for the issuing and accepting the systems.
The issuing system should permit the generation of an SSO ticket −
login/create_sso2_ticket = 1 : SSO ticket including certificate
login/create_sso2_ticket = 2 : SSO ticket without certificate
login/create_sso2_ticket = 3 : Generate only assertion tickets
Values allowed− 0 / 1 / 2 / 3
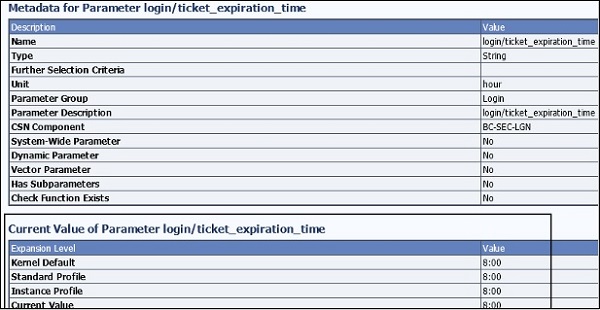
login/ticket_expiration_time
To make it possible to have a Single Sign-On (SSO) when using mySAP.com Workplace, SSO tickets can be used. When creating an SSO ticket, you can set the validity period. Once this has expired, the SSO ticket cannot be used any more to log on to workplace component systems. The user then needs to log on to the workplace server again to obtain a new SSO ticket.
Values allowed − <Hours>[:<Minutes>]
If incorrect values are entered, the default value is used (8 hours).
The correct values will be as shown below −
- 24 → 24 hours
- 1:30 → 1 hours, 30 minutes
- 0:05 → 5 minutes
The incorrect values will be as follows −
- 40 (0:40 would be correct)
- 0:60 (1 would be correct)
- 10:000 (10 would be correct)
- 24: (24 would be correct)
- 1:A3
X.509 Client Certificates
Using an SSO method, you can use X.509 client certificates to authenticate the NetWeaver Application Server. The client certificates use very strong cryptography methods to secure user access to the NetWeaver Application server, so your NetWeaver Application Server should be enabled with strong cryptography techniques.
You should have SSL configured on your SAP NetWeaver application servers as the authentication occurs using the SSL protocol without entering any username and password. To use the SSL protocol, it requires an HTTPS connection to communicate between the Web browser and the NetWeaver ABAP Application Server.
Security Assertion Markup Language (SAML2.0)
The SAML2.0 can be used as authentication with Single Sign-On SSO and it enables SSO across different domains. SAML 2.0 is developed by an organization name OASIS. It also provides a Single Log-Out option, which means that when a user logs off from all the systems, the service provider in the SAP system notifies the identity providers which in turn logs off all the sessions.
The following are the advantages of using SAML2.0 authentication −
You can decrease the overhead of maintaining authentication for the system hosting the application to other system.
You can also maintain authentication for external service providers without maintaining user identities in systems.
Single Logout option in all systems.
To map the user accounts automatically.
Kerberos Authentication
You can also user Kerberos Authentication for SAP NetWeaver Application server using access via web clients and web browsers. It uses Simple and Protected GSS API Negotiation mechanism SPNego which also requires a Single Sign-On SSO 2.0 or higher version with additional licenses to use this authentication. The SPNego doesnt support Transport Layer security, so it is recommended to use SSL protocol to add transport layer security to communicate with NetWeaver Application Server.
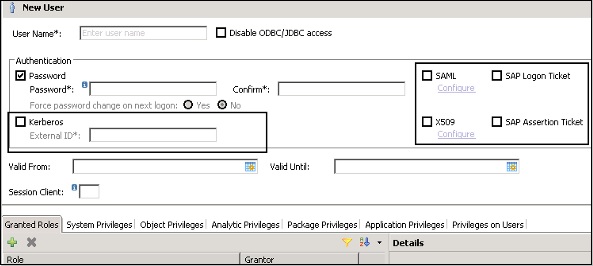
In above screenshot, you can see different authentication methods that can be configured in a user profile for authentication purposes.
Each authentication method in SAP has its own advantages and can be used in different scenarios.
