- Computer Security - Home
- Computer Security - Overview
- Computer Security - Elements
- Computer Security - Terminologies
- Computer Security - Layers
- Computer Security - Securing OS
- Computer Security - Antiviruses
- Computer Security - Malwares
- Computer Security - Encryption
- Computer Security - Data Backup
- Disaster Recovery
- Computer Security - Network
- Computer Security - Policies
- Computer Security - Checklist
- Legal Compliance
Computer Security - Network
In this chapter we will discuss regarding the network from the view of security. We will also look into which are the systems that help us as system administrators to increase the security.
For example − We are system administrators of a large chain of super markets, but our company wants to go online by launching an online selling platform. We have done the configuration and the system is up and working, but after a week we hear that the platform was hacked.
We ask a question to ourselves What did we do wrong? We skipped the security of the network which is as important as the set up because this hacking can directly influence the companys reputation resulting in decrease of sales and market value.
Devices that Help us with Network Security
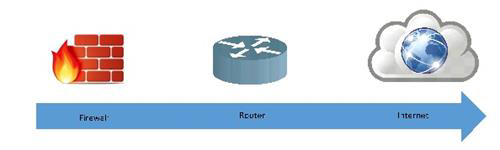
Firewalls − They can be software or applications which operate at the network level. They protect Private networks from external users and other networks. Generally, they are a compound of programs and their main function is to monitor the traffic flow from outside to inside and vice versa. Their position is generally behind a router or in front of the router depending on the network topologies.
They are also called Intrusion detection devices; their traffic rules are configured according to the company policy rules. For example, you block all incoming traffic to port POP because you dont want to receive a mail so as to be secured from all possible mail attacks. They log all the network attempts for a latter audit for you.
They also can work as packet filters this means that the firewall takes the decisions to forward or not the packet based on source and destination addresses and ports.
Some of the recommended brands are −
- Cisco ASA Series
- Checkpoint
- Fortinet
- Juniper
- SonicWALL
- pfSense
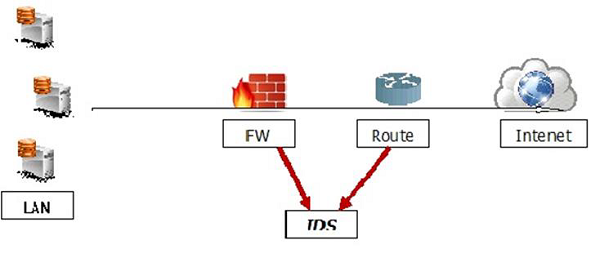
Intrusion Detection Systems
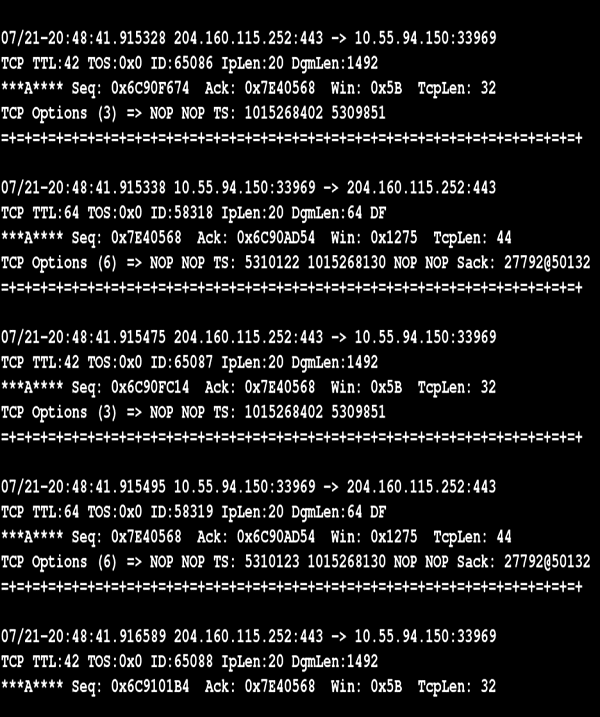
Intrusion Detection Systems are also as important as the firewall because they help us to detect the type of attack that is being done to our system and then to make a solution to block them. The monitoring part like tracing logs, looking for doubtful signatures and keeping history of the events triggered. They help also the network administrators to check the connection integrity and authenticity that occur.
Let us see the schema of their positions −
Intrusion Detection Tools
One of the best intrusion detection tool is Snort, you can take information and download the same from − www.snort.org
It is software based, but is an opensource so it is free and easy to configure. It has a real time signature based network IDS, which notifies the system administrators or attacks like port scanners, DDOS attacks, CGI attacks, backdoors, OS finger printing.
The other IDS are −
- BlackICE Defender
- CyberCop Monitor
- Check point RealSecure
- Cisco Secure IDS
- Vanguard Enforcer
- Lucent RealSecure.
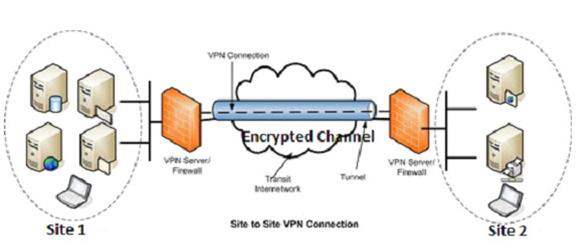
Virtual Private Network
This type of a network is widely used in a small business or enterprise networks. It helps to send and receive data across the internet, but in a secure and encrypted way. Generally, this network is created between two secure network devices like two firewalls.
An example is a connection between two ASA 5505 firewalls as shown in the following image.