
- Cryptography - Home
- Cryptography - Origin
- Cryptography - History
- Cryptography - Principles
- Cryptography - Applications
- Cryptography - Benefits & Drawbacks
- Cryptography - Modern Age
- Cryptography - Traditional Ciphers
- Cryptography - Need for Encryption
- Cryptography - Double Strength Encryption
- Cryptosystems
- Cryptosystems
- Cryptosystems - Components
- Attacks On Cryptosystem
- Cryptosystems - Rainbow table attack
- Cryptosystems - Dictionary attack
- Cryptosystems - Brute force attack
- Cryptosystems - Cryptanalysis Techniques
- Types of Cryptography
- Cryptosystems - Types
- Public Key Encryption
- Modern Symmetric Key Encryption
- Cryptography Hash functions
- Key Management
- Cryptosystems - Key Generation
- Cryptosystems - Key Storage
- Cryptosystems - Key Distribution
- Cryptosystems - Key Revocation
- Block Ciphers
- Cryptosystems - Stream Cipher
- Cryptography - Block Cipher
- Cryptography - Feistel Block Cipher
- Block Cipher Modes of Operation
- Block Cipher Modes of Operation
- Electronic Code Book (ECB) Mode
- Cipher Block Chaining (CBC) Mode
- Cipher Feedback (CFB) Mode
- Output Feedback (OFB) Mode
- Counter (CTR) Mode
- Classic Ciphers
- Cryptography - Reverse Cipher
- Cryptography - Caesar Cipher
- Cryptography - ROT13 Algorithm
- Cryptography - Transposition Cipher
- Cryptography - Encryption Transposition Cipher
- Cryptography - Decryption Transposition Cipher
- Cryptography - Multiplicative Cipher
- Cryptography - Affine Ciphers
- Cryptography - Simple Substitution Cipher
- Cryptography - Encryption of Simple Substitution Cipher
- Cryptography - Decryption of Simple Substitution Cipher
- Cryptography - Vigenere Cipher
- Cryptography - Implementing Vigenere Cipher
- Modern Ciphers
- Base64 Encoding & Decoding
- Cryptography - XOR Encryption
- Substitution techniques
- Cryptography - MonoAlphabetic Cipher
- Cryptography - Hacking Monoalphabetic Cipher
- Cryptography - Polyalphabetic Cipher
- Cryptography - Playfair Cipher
- Cryptography - Hill Cipher
- Polyalphabetic Ciphers
- Cryptography - One-Time Pad Cipher
- Implementation of One Time Pad Cipher
- Cryptography - Transposition Techniques
- Cryptography - Rail Fence Cipher
- Cryptography - Columnar Transposition
- Cryptography - Steganography
- Symmetric Algorithms
- Cryptography - Data Encryption
- Cryptography - Encryption Algorithms
- Cryptography - Data Encryption Standard
- Cryptography - Triple DES
- Cryptography - Double DES
- Advanced Encryption Standard
- Cryptography - AES Structure
- Cryptography - AES Transformation Function
- Cryptography - Substitute Bytes Transformation
- Cryptography - ShiftRows Transformation
- Cryptography - MixColumns Transformation
- Cryptography - AddRoundKey Transformation
- Cryptography - AES Key Expansion Algorithm
- Cryptography - Blowfish Algorithm
- Cryptography - SHA Algorithm
- Cryptography - RC4 Algorithm
- Cryptography - Camellia Encryption Algorithm
- Cryptography - ChaCha20 Encryption Algorithm
- Cryptography - CAST5 Encryption Algorithm
- Cryptography - SEED Encryption Algorithm
- Cryptography - SM4 Encryption Algorithm
- IDEA - International Data Encryption Algorithm
- Public Key (Asymmetric) Cryptography Algorithms
- Cryptography - RSA Algorithm
- Cryptography - RSA Encryption
- Cryptography - RSA Decryption
- Cryptography - Creating RSA Keys
- Cryptography - Hacking RSA Cipher
- Cryptography - ECDSA Algorithm
- Cryptography - DSA Algorithm
- Cryptography - Diffie-Hellman Algorithm
- Data Integrity in Cryptography
- Data Integrity in Cryptography
- Message Authentication
- Cryptography Digital signatures
- Public Key Infrastructure
- Hashing
- MD5 (Message Digest Algorithm 5)
- SHA-1 (Secure Hash Algorithm 1)
- SHA-256 (Secure Hash Algorithm 256-bit)
- SHA-512 (Secure Hash Algorithm 512-bit)
- SHA-3 (Secure Hash Algorithm 3)
- Hashing Passwords
- Bcrypt Hashing Module
- Modern Cryptography
- Quantum Cryptography
- Post-Quantum Cryptography
- Cryptographic Protocols
- Cryptography - SSL/TLS Protocol
- Cryptography - SSH Protocol
- Cryptography - IPsec Protocol
- Cryptography - PGP Protocol
- Image & File Cryptography
- Cryptography - Image
- Cryptography - File
- Steganography - Image
- File Encryption and Decryption
- Cryptography - Encryption of files
- Cryptography - Decryption of files
- Cryptography in IoT
- IoT security challenges, Threats and Attacks
- Cryptographic Techniques for IoT Security
- Communication Protocols for IoT Devices
- Commonly Used Cryptography Techniques
- Custom Building Cryptography Algorithms (Hybrid Cryptography)
- Cloud Cryptography
- Quantum Cryptography
- DNA Cryptography
- One Time Password (OTP) algorithm in Cryptography
- Difference Between
- Cryptography - MD5 vs SHA1
- Cryptography - RSA vs DSA
- Cryptography - RSA vs Diffie-Hellman
- Cryptography vs Cryptology
- Cryptography - Cryptology vs Cryptanalysis
- Cryptography - Classical vs Quantum
- Cryptography vs Steganography
- Cryptography vs Encryption
- Cryptography vs Cyber Security
- Cryptography - Stream Cipher vs Block Cipher
- Cryptography - AES vs DES ciphers
- Cryptography - Symmetric vs Asymmetric
Cryptography - Symmetric vs Asymmetric
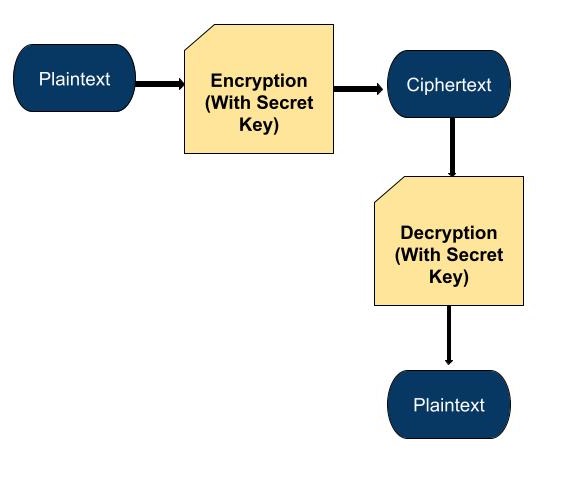
In this chapter we will be discussing about the Symmetric and Asymmetric Encryption and also see the differences between these two encryption systems. So let us begin first with the Symmetric Encryption.
What is Symmetric Encryption?
Symmetric cryptography is based on techniques that encrypt and decrypt data with the same key. In other words, the sender uses a secret key to encrypt the communication. The recipients then use the same key to decrypt and read the contents. As a result, the key must be shared with all people authorised to decrypt the message.
Benefits of symmetric encryption include the following −
- Security − Since the same key is used for both encryption and decryption, symmetric encryption offers robust data security. Unauthorised users find it more difficult to access the data as a result.
- Speed − Because symmetric encryption uses the same key for both encryption and decryption, it is typically faster than other encryption methods. For applications that need quick data encryption and decryption, this makes it a solid option.
- Efficiency − Symmetric encryption can save time and money by requiring less computing power and resources for both data encryption and decryption.
- Simplicity − Since symmetric encryption only needs one key for both encryption and decryption, it is simple to set up and operate. This makes it a well-liked option for applications that need plain-spoken encryption.
Symmetric encryption can be less secure than asymmetric encryption, which is a drawback. Should the key get up in the wrong hands, there could be a compromise of the data. As a result, it's critical to make sure the key is maintained safe and distributed to approved users only.
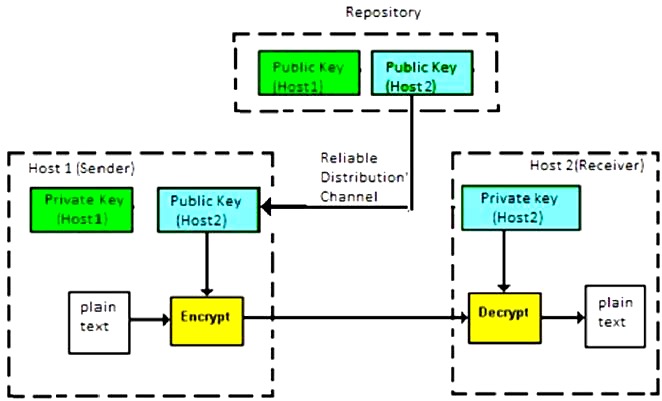
What is Asymmetric Encryption?
Asymmetric cryptography is based on two independent keys that are related mathematically. A public key is the first of them. It can be shared with the public and is used to encrypt messages. The private key is the second one. Its task is to decode the information. The private key must be kept in a safe place and must never be shared. While it is theoretically feasible, it is practically almost impossible to calculate the private key based on the public one.
Compared to other encryption methods, asymmetric encryption has the following features −
- Security − Since the private key needed for decryption is kept private and not shared with anybody, asymmetric encryption offers robust data security. Unauthorised users find it more difficult to access the data as a result.
- Authentication − Since the public key can be used to confirm the sender's identity, asymmetric encryption can also be used for authentication. This aids in deterring fraud and safeguarding against malevolent assaults.
- Key distribution − Since each user has a distinct set of public and private keys, asymmetric encryption does not require a secure channel for key distribution. This facilitates key distribution and access control for encrypted data.
- Non-repudiation − It is a feature of asymmetric encryption, which means that a message's sender cannot retract its transmission because it can be linked to their specific private key.
- Flexibility − Asymmetric encryption is adaptable and suitable for a variety of uses, such as safe online banking, secure email exchanges, and safe system and network access.
Differences between Symmetric and Asymmetric Encryption
Here is the table provided to show the differences between these two encryption methods −
| Aspect | Symmetric Encryption | Asymmetric Encryption |
|---|---|---|
| Key Usage | Uses a single key for both encryption and decryption. | Uses a pair of keys: one for encryption (public key) and one for decryption (private key). |
| Key Distribution | Key distribution can be challenging. | Key distribution is easier as the public key can be shared openly. |
| Speed | Generally faster compared to asymmetric encryption. | Slower compared to symmetric encryption due to complex algorithms. |
| Security | Vulnerable to key distribution risks and requires secure channels. | More secure as the private key is kept secret, and there's no need to share it. |
| Use Cases | Suitable for encrypting large volumes of data securely. | Ideal for securing communication channels and authenticating identities. |
| Examples | AES (Advanced Encryption Standard), DES (Data Encryption Standard). | RSA, ECC (Elliptic Curve Cryptography). |
Summary
Symmetric encryption uses the same key for both encryption and decryption, which is faster but needs secure key exchange. Asymmetric encryption uses a pair of keys to improve security and facilitate key sharing. Asymmetric encryption is ideal for secure communication and authentication, but symmetric encryption is best for handling huge data volumes. Examples are AES and RSA, respectively.
