
- System Analysis and Design - Home
- System Analysis & Design - Overview
- Differences between System Analysis and System Design
- System Analysis and Design - Communication Protocols
- Horizontal and Vertical Scaling in System Design
- Capacity Estimation in Systems Design
- Roles of Web Server and Proxies in Designing Systems
- Clustering and Load Balancing
- System Development Life Cycle
- System Analysis and Design - Requirement Determination
- System Analysis and Design - Systems Implementation
- System Analysis and Design - System Planning
- System Analysis and Design - Structured Analysis
- System Design
- System Analysis and Design - Design Strategies
- System Analysis and Design - Software Deployment
- Software Deployment Example Using Docker
- Functional Vs. Non-functional Requirements
- Data Flow Diagrams(DFD)
- Data Flow Diagram - What It Is?
- Data Flow Diagram - Types and Components
- Data Flow Diagram - Development
- Data Flow Diagram - Balancing
- Data Flow Diagram - Decomposition
- Databases in System Design
- System Design - Databases
- System Design - Database Sharding
- System Design - Database Replication
- System Design - Database Federation
- System Design - Designing Authentication System
- Database Design Vs. Database Architecture
- Database Federation Vs. Database Sharding
- High Level Design(HLD)
- System Design - High Level Design
- System Design - Availability
- System Design - Consistency
- System Design - Reliability
- System Design - CAP Theorem
- System Design - API Gateway
- Low Level Design(LLD)
- System Design - Low Level Design
- System Design - Authentication Vs. Authorization
- System Design - Performance Optimization Techniques
- System Design - Containerization Architecture
- System Design - Modularity and Interfaces
- System Design - CI/CD Pipelines
- System Design - Data Partitioning Techniques
- System Design - Essential Security Measures
- System Implementation
- Input / Output & Forms Design
- Testing and Quality Assurance
- Implementation & Maintenance
- System Security and Audit
- Object-Oriented Approach
- System Analysis & Design Resources
- Quick Guide
- Useful Resources
- Discussion
System Security and Audit
System Audit
It is an investigation to review the performance of an operational system. The objectives of conducting a system audit are as follows −
To compare actual and planned performance.
To verify that the stated objectives of system are still valid in current environment.
To evaluate the achievement of stated objectives.
To ensure the reliability of computer based financial and other information.
To ensure all records included while processing.
To ensure protection from frauds.
Audit of Computer System Usage
Data processing auditors audits the usage of computer system in order to control it. The auditor need control data which is obtained by computer system itself.
The System Auditor
The role of auditor begins at the initial stage of system development so that resulting system is secure. It describes an idea of utilization of system that can be recorded which helps in load planning and deciding on hardware and software specifications. It gives an indication of wise use of the computer system and possible misuse of the system.
Audit Trial
An audit trial or audit log is a security record which is comprised of who has accessed a computer system and what operations are performed during a given period of time. Audit trials are used to do detailed tracing of how data on the system has changed.
It provides documentary evidence of various control techniques that a transaction is subject to during its processing. Audit trials do not exist independently. They are carried out as a part of accounting for recovering lost transactions.
Audit Methods
Auditing can be done in two different ways −
Auditing around the Computer
- Take sample inputs and manually apply processing rules.
- Compare outputs with computer outputs.
Auditing through the Computer
- Establish audit trial which allows examining selected intermediate results.
- Control totals provide intermediate checks.
Audit Considerations
Audit considerations examine the results of the analysis by using both the narratives and models to identify the problems caused due to misplaced functions, split processes or functions, broken data flows, missing data, redundant or incomplete processing, and nonaddressed automation opportunities.
The activities under this phase are as follows −
- Identification of the current environment problems
- Identification of problem causes
- Identification of alternative solutions
- Evaluation and feasibility analysis of each solution
- Selection and recommendation of most practical and appropriate solution
- Project cost estimation and cost benefit analysis
Security
System security refers to protecting the system from theft, unauthorized access and modifications, and accidental or unintentional damage. In computerized systems, security involves protecting all the parts of computer system which includes data, software, and hardware. Systems security includes system privacy and system integrity.
System privacy deals with protecting individuals systems from being accessed and used without the permission/knowledge of the concerned individuals.
System integrity is concerned with the quality and reliability of raw as well as processed data in the system.
Control Measures
There are variety of control measures which can be broadly classified as follows −
Backup
Regular backup of databases daily/weekly depending on the time criticality and size.
Incremental back up at shorter intervals.
Backup copies kept in safe remote location particularly necessary for disaster recovery.
Duplicate systems run and all transactions mirrored if it is a very critical system and cannot tolerate any disruption before storing in disk.
Physical Access Control to Facilities
- Physical locks and Biometric authentication. For example, finger print
- ID cards or entry passes being checked by security staff.
- Identification of all persons who read or modify data and logging it in a file.
Using Logical or Software Control
- Password system.
- Encrypting sensitive data/programs.
- Training employees on data care/handling and security.
- Antivirus software and Firewall protection while connected to internet.
Risk Analysis
A risk is the possibility of losing something of value. Risk analysis starts with planning for secure system by identifying the vulnerability of system and impact of this. The plan is then made to manage the risk and cope with disaster. It is done to accesses the probability of possible disaster and their cost.
Risk analysis is a teamwork of experts with different backgrounds like chemicals, human error, and process equipment.
The following steps are to be followed while conducting risk analysis −
Identification of all the components of computer system.
Identification of all the threats and hazards that each of the components faces.
Quantify risks i.e. assessment of loss in the case threats become reality.
Risk Analysis Main Steps
As the risks or threats are changing and the potential loss are also changing, management of risk should be performed on periodic basis by senior managers.
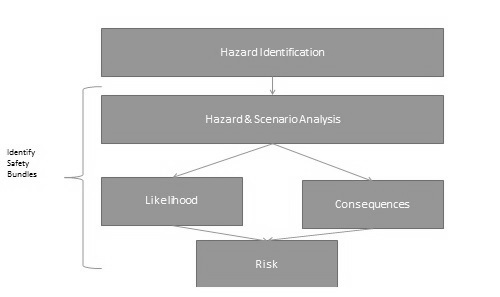
Risk management is a continuous process and it involves the following steps −
Identification of security measures.
Calculation of the cost of implementation of security measures.
Comparison of the cost of security measures with the loss and probability of threats.
Selection and implementation of security measures.
Review of the implementation of security measures.
