
- Penetration Testing - Home
- Penetration Testing - Introduction
- Penetration Testing - Method
- Testing Vs. Vulnerability Assessment
- Penetration Testing - Types
- Manual and Automated
- Penetration Testing - Tools
- Penetration Testing - Infrastructure
- Penetration Testing - Testers
- Penetration Testing - Report Writing
- Penetration Testing - Ethical Hacking
- Pen Testing Vs. Ethical Hacking
- Penetration Testing - Limitations
- Penetration Testing - Remediation
- Penetration Testing - Legal Issues
Types of Penetration Testing
The type of penetration testing normally depends on the scope and the organizational wants and requirements. This chapter discusses about different types of Penetration testing. It is also known as Pen Testing.
Types of Pen Testing
Following are the important types of pen testing −
- Black Box Penetration Testing
- White Box Penetration Testing
- Grey Box Penetration Testing
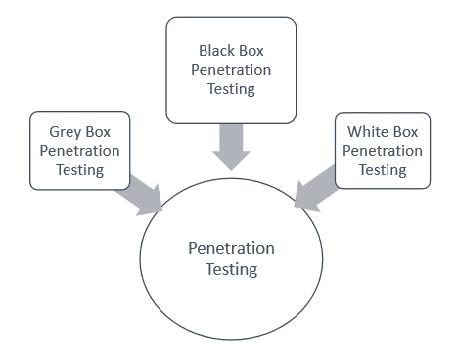
For better understanding, let us discuss each of them in detail −
Black Box Penetration Testing
In black box penetration testing, tester has no idea about the systems that he is going to test. He is interested to gather information about the target network or system. For example, in this testing, a tester only knows what should be the expected outcome and he does not know how the outcomes arrives. He does not examine any programming codes.
Advantages of Black Box Penetration Testing
It has the following advantages −
Tester need not necessarily be an expert, as it does not demand specific language knowledge
Tester verifies contradictions in the actual system and the specifications
Test is generally conducted with the perspective of a user, not the designer
Disadvantages of Black Box Penetration Testing
Its disadvantages are −
Particularly, these kinds of test cases are difficult to design.
Possibly, it is not worth, incase designer has already conducted a test case.
It does not conduct everything.
White Box Penetration Testing
This is a comprehensive testing, as tester has been provided with whole range of information about the systems and/or network such as Schema, Source code, OS details, IP address, etc. It is normally considered as a simulation of an attack by an internal source. It is also known as structural, glass box, clear box, and open box testing.
White box penetration testing examines the code coverage and does data flow testing, path testing, loop testing, etc.
Advantages of White Box Penetration Testing
It carries the following advantages −
It ensures that all independent paths of a module have been exercised.
It ensures that all logical decisions have been verified along with their true and false value.
It discovers the typographical errors and does syntax checking.
It finds the design errors that may have occurred because of the difference between logical flow of the program and the actual execution.
Grey Box Penetration Testing
In this type of testing, a tester usually provides partial or limited information about the internal details of the program of a system. It can be considered as an attack by an external hacker who had gained illegitimate access to an organization's network infrastructure documents.
Advantages of Grey Box Penetration Testing
It has the following advantages −
As the tester does not require the access of source code, it is non-intrusive and unbiased
As there is clear difference between a developer and a tester, so there is least risk of personal conflict
You dont need to provide the internal information about the program functions and other operations
Areas of Penetration Testing
Penetration testing is normally done in the following three areas −
Network Penetration Testing − In this testing, the physical structure of a system needs to be tested to identify the vulnerability and risk which ensures the security in a network. In the networking environment, a tester identities security flaws in design, implementation, or operation of the respective company/organizations network. The devices, which are tested by a tester can be computers, modems, or even remote access devices, etc
Application Penetration Testing − In this testing, the logical structure of the system needs to be tested. It is an attack simulation designed to expose the efficiency of an applications security controls by identifying vulnerability and risk. The firewall and other monitoring systems are used to protect the security system, but sometime, it needs focused testing especially when traffic is allowed to pass through the firewall.
The response or workflow of the system − This is the third area that needs to be tested. Social engineering gathers information on human interaction to obtain information about an organization and its computers. It is beneficial to test the ability of the respective organization to prevent unauthorized access to its information systems. Likewise, this test is exclusively designed for the workflow of the organization/company.
