
- Penetration Testing - Home
- Penetration Testing - Introduction
- Penetration Testing - Method
- Testing Vs. Vulnerability Assessment
- Penetration Testing - Types
- Manual and Automated
- Penetration Testing - Tools
- Penetration Testing - Infrastructure
- Penetration Testing - Testers
- Penetration Testing - Report Writing
- Penetration Testing - Ethical Hacking
- Pen Testing Vs. Ethical Hacking
- Penetration Testing - Limitations
- Penetration Testing - Remediation
- Penetration Testing - Legal Issues
Penetration Testing - Manual & Automated
Both manual penetration testing and automated penetration testing are conducted for the same purpose. The only difference between them is the way they are conducted. As the name suggests, manual penetration testing is done by human beings (experts of this field) and automated penetration testing is done by machine itself.
This chapter will help you learn the concept, differences, and applicability of both the terms.
What is Manual Penetration Testing?
Manual penetration testing is the testing that is done by human beings. In such type of testing, vulnerability and risk of a machine is tested by an expert engineer.
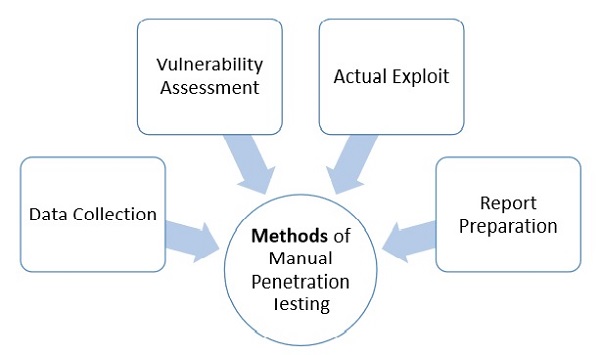
Generally, testing engineers perform the following methods −
Data Collection − Data collection plays a key role for testing. One can either collect data manually or can use tool services (such as webpage source code analysis technique, etc.) freely available online. These tools help to collect information like table names, DB versions, database, software, hardware, or even about different third party plugins, etc
Vulnerability Assessment − Once the data is collected, it helps the testers to identify the security weakness and take preventive steps accordingly.
Actual Exploit − This is a typical method that an expert tester uses to launch an attack on a target system and likewise, reduces the risk of attack.
Report Preparation − Once the penetration is done, the tester prepares a final report that describes everything about the system. Finally the report is analyzed to take corrective steps to protect the target system.
Types of Manual Penetration Testing
Manual penetration testing is normally categorized in two following ways −
Focused Manual Penetration Testing − It is a much focused method that tests specific vulnerabilities and risks. Automated penetration testing cannot perform this testing; it is done only by human experts who examine specific application vulnerabilities within the given domains.
Comprehensive Manual Penetration Testing − It is through testing of whole systems connected with each other to identify all sorts of risk and vulnerability. However, the function of this testing is more situational, such as investigating whether multiple lower-risk faults can bring more vulnerable attack scenario, etc
What is Automated Penetration Testing?
Automated penetration testing is much faster, efficient, easy, and reliable that tests the vulnerability and risk of a machine automatically. This technology does not require any expert engineer, rather it can be run by any person having least knowledge of this field.
Tools for automated penetration testing are Nessus, Metasploit, OpenVAs, backtract (series 5), etc. These are very efficient tools that changed the efficiency and meaning of penetration testing.
However, the following table illustrates the fundamental difference between the manual and automated penetration testing −
| Manual Penetration Testing | Automated Penetration Testing |
|---|---|
| It requires expert engineer to perform the test. | It is automated so even a learner can run the test. |
| It requires different tools for the testing. | It has integrated tools does required anything from outside. |
| In this type of testing, results can vary from test to test. | It has fixed result. |
| This test requires to remember cleaning up memory by the tester. | It does not. |
| It is exhaustive and time taking. | It is more efficient and fast. |
| It has additional advantages i.e. if an expert does pen test, then he can analyze better, he can think what a hacker can think and where he can attack. Hence, he can put security accordingly. | It cannot analyze the situation. |
| As per the requirement, an expert can run multiple testing. | It cannot. |
| For critical condition, it is more reliable. | It is not. |
