- Malware Removal - Home
- Malware Removal - Overview
- Malware Removal - How It Works
- Malware Removal - Types
- Detection Techniques
- Preparation for Removal
- Malware Removal - Process
- Malware Removal - Protection
- Malware Removal - Removal Tools
Malware Removal - Types
Malwares are diverse; they come from different functions and behave differently under various situations. Some of the most infamous and dangerous types of malwares are given below:
- Virus
- Adware
- Spyware
- Trojan
- Rootkits
- Botnets
- Ransom Ware
Let us understand each of these in detail.
Virus
Virus is a malware program that acts in an interesting way. This program executes or replicates itself by putting-in some copies of itself in other computer programs, boot sector, data files, hard disk, etc. When the replication process is done, then the areas that are affected are said to be the infected ones.
Viruses are built to perform some of the most harmful activities on the hosts when they are infected. They can steal the CPU time or even the space in the hard disk. They can also corrupt the data and can put some funny messages on the screen of the system.
Adware
This software is mainly the advertising supporting software. A package that comes automatically with the advertisements inside. Hence, it can generate some good income for the owner.
Spyware
Spyware is a software that is mainly used for the gathering of information about some organization or a person. That information is gathered without anyone getting to know that the information is being fathered from his or her system.
Trojan
Trojan is a non-self-replicating type of malware. It contains some malicious code, which carries out some actions that are determined by the nature of that specific Trojan. This happens upon the execution only. The result of the action is normally the data loss and it can also harm the system in many ways.
Rootkits
Rootkits are the stealth type of malware. They are designed in some special way that they can actually hide themselves very well and it is quite difficult to detect them in a system. The normal methods of detection do not work on them.
Botnets
Botnet is a software installed on a computer that is connected through the internet and it can help one communicate with the other same type of programs, so that some actions can be performed. They can be same as keeping control of some IRC, which are Internet Related Charts. In addition, it can be utilized for sending out some spam emails or to participate in some distribution of denial of services attacks.
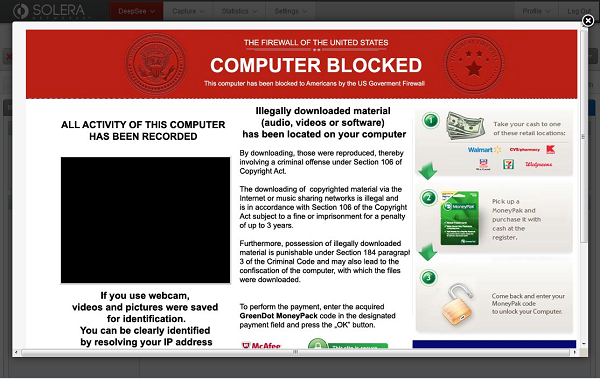
Ransom Ware
Ransom ware is a software that encrypts files, which are on the hard drives. Some of them can even end up with simply showing some message about payment of money to the person, who has implemented this program.