
- Collaborative Management Home
- Introduction
- Collaboration System
- Leadership Styles
- Collaborative Approach
- Collaborative Tools
- The Arc's Model
- The ESSIM Initiative
- Collaborative System
- Change Management
- Collaborative Project Management
- Project Management Architecture
- Application & Implementations
- Conflict Management
- Case Study
Change Management
Change management is a process, an enterprise specialty, and a body of knowledge. The notion of change management as a process or task can be described as a double-edged sword.
The first edge is applied to internal change in a sequential fashion within an ongoing company. The aim is to implement new methods and controlled systems more effectively in a company.
The second edge of the change management sword is applicable to the changes over which the company practices little or no control (like legislation, social and political upheaval, etc.).
Change as a System
A systems approach involves two important foundations −
First, it establishes that nothing can change without affecting every part of the system to which it belongs.
Second, change in any single part of a system influences every other part of the system.
Systems can be categorized as either open or closed system.
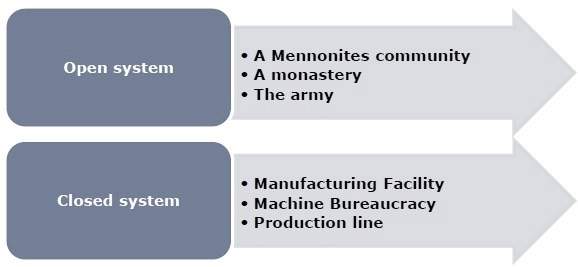
Open systems are highly responsive to the external environment. In contrast, closed systems are poorly responsive to environmental impacts. No system can be completely closed − the degree to which a system is open or closed is determined by the extent to which changes can be controlled.
The Change Problem
The change Problem includes one or more divisions or groups, the entire enterprise, or one or more aspects of the companys environment.
The foundation of the system requires answers to at least these five Ws and one H (Who, What, Why, Where, and Whenthen How).
The following few examples can be used to formulate specific questions −
- Who from the company needs to be involved in the change?
- What exercises need to be changed?
- Why do we need to change our ongoing practices?
- Where the changes are needed the most?
- When will the company consider implementation?
- How to change our traditional practices for better?
Change Program Phase
The process model is structured in three phases −
Phase 1 − Creating the change foundation − It focuses on aligning business elements and leadership through the making of new customer-focused goals, establishing sponsorships, and securing commitment and capabilities.
Phase 2 − Designing the change plan − It focuses on aligning the corporate mission with the change plan and determining the challenges.
Phase 3 − Implementing the change plan − It focuses on deploying change with the help of an effective communication program and client management.
Communication Process and Strategy
Communication plays a vital role in strategic, tactical, and personal levels in creating change. Communication is important to −
Align employee and enterprise performance with business objectives.
Enable clients to understand, and embrace change through education and persuasion.
Deliver specific notes on the change (five Ws and one H)
Support feedback, review, and interaction to ensure ownership and success.
Motivate to act.
Involve through a strong whats in it for me approach.
To be effective and efficient, a change management team includes minimum one communication expert, who is then supported by a team of communication specialists.
The duties of the change communication team include −
- Identification of issues that affects each segment having an impact due to the change.
- Determination of the combined communication tools needed.
- Assuring that appropriate feedback and review mechanisms exist.
- Creation of effective measures to assess communication efficiency and effectiveness.
Final Recommendations
These recommendations follow to-do list of tactics that can be deployed in managing change.
Be open to change − Change is inevitable − its how people handle and control it that gives a positive rather than a negative outcome for enterprise or individuals.
Remember − The function of change management is to bring order to a chaotic and messy situation, not to pretend that it is already well organized, structured, and disciplined.
