
- Ethical Hacking - Home
- Ethical Hacking - Overview
- Ethical Hacking - Hacker Types
- Ethical Hacking - Famous Hackers
- Ethical Hacking - Terminologies
- Ethical Hacking - Tools
- Ethical Hacking - Skills
- Ethical Hacking - Process
- Ethical Hacking - Reconnaissance
- Ethical Hacking - Footprinting
- Ethical Hacking - Fingerprinting
- Ethical Hacking - Sniffing
- Ethical Hacking - Sniffing Tools
- Ethical Hacking - ARP Poisoning
- Ethical Hacking - DNS Poisoning
- Ethical Hacking - Exploitation
- Ethical Hacking - Enumeration
- Ethical Hacking - Metasploit
- Ethical Hacking - Trojan Attacks
- Ethical Hacking - TCP/IP Hijacking
- Ethical Hacking - Email Hijacking
- Ethical Hacking - Password Hacking
- Ethical Hacking - Wireless Hacking
- Ethical Hacking - Social Engineering
- Ethical Hacking - DDOS Attacks
- Ethical Hacking - Cross Site Scripting
- Ethical Hacking - SQL Injection
- Ethical Hacking - Pen Testing
Ethical Hacking - Cross-Site Scripting
Cross-site scripting (XSS) is a code injection attack that allows an attacker to execute malicious JavaScript in another user's browser.
The attacker does not directly target his victim. Instead, he exploits a vulnerability in a website that the victim visits, in order to get the website to deliver the malicious JavaScript for him. To the victim's browser, the malicious JavaScript appears to be a legitimate part of the website, and the website has thus acted as an unintentional accomplice to the attacker. These attacks can be carried out using HTML, JavaScript, VBScript, ActiveX, Flash, but the most used XSS is malicious JavaScript.
These attacks also can gather data from account hijacking, changing of user settings, cookie theft/poisoning, or false advertising and create DoS attacks.
Example
Lets take an example to understand how it works. We have a vulnerable webpage that we got by the metasploitable machine. Now we will test the field that is highlighted in red arrow for XSS.
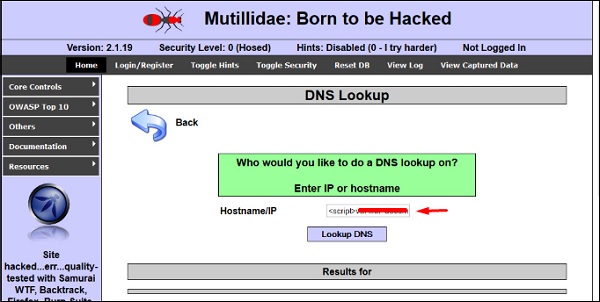
First of all, we make a simple alert script
<script> alert(I am Vulnerable) </script>
It will produce the following output −

Types of XSS Attacks
XSS attacks are often divided into three types −
Persistent XSS, where the malicious string originates from the website's database.
Reflected XSS, where the malicious string originates from the victim's request.
DOM-based XSS, where the vulnerability is in the client-side code rather than the server-side code.
Generally, cross-site scripting is found by vulnerability scanners so that you dont have to do all the manual job by putting a JavaScript on it like
<script>
alert('XSS')
</script>
Burp Suite and acunetix are considered as the best vulnerability scanners.
Quick Tip
To prevent XSS attacks, keep the following points in mind −
Check and validate all the form fields like hidden forms, headers, cookies, query strings.
Implement a stringent security policy. Set character limitation in the input fields.
