
- Cloud Computing Basics
- Cloud Computing - Home
- Cloud Computing - Overview
- Cloud Computing - Evolution
- Cloud Computing - Characteristics
- Cloud Computing - Advantages
- Cloud Computing - Planning
- Cloud Computing - Technologies
- Cloud Computing - Architecture
- Cloud Computing - Infrastructure
- Cloud Deployment Models
- Public Cloud Model
- Private Cloud Model
- Hybrid Cloud Model
- Community Cloud Model
- Cloud Service Models
- Infrastructure Service
- Platform Service
- Software ervice
- Identity Service
- Network Service
- IaaS, PaaS, and SaaS
- Cloud Virtualization
- Cloud Computing Virtualization
- Server Virtualization
- Data Virtualization
- Software Virtualization
- Storage Virtualization
- Network Virtualization
- Linux Virtualization
- Cloud Advanced Concepts
- Cloud Computing - Management
- Cloud Computing - Data Storage
- Cloud Computing - Security
- Cloud Computing - Operation
- Cloud Computing - Applications
- Cloud Computing - Providers
- Cloud Computing - Challenges
- Cloud Computing - Mobile
- Google Cloud Platform
- Cloud Computing - Multitenancy
- Hypervisor Security
- Cloud Computing - Principles
- Security Architecture
- Fault Tolerance
- Cloud Computing - Resiliency
- Service Level Agreements
- Cloud Networking
- Server Consolidation
- Cloud Computing - Scaling
- Autoscaling vs Load Balancer
- Scalability and Elasticity
- Cloud Bursting vs Cloud Scaling
- Resource Pooling
- Load Balancing
- Security Threats in Implementation SaaS
- Cloud Computing - Data Center
- Cloud Computing - Aneka
- Cloud Computing - Rapid Elasticity
- Cloud Computing - Xaas
- Cloud Computing - DaaS
- Cloud Computing - CaaS
- Cloud Computing - Roots
- Cloud Hosting vs Web Hosting
- Colocation vs Cloud
- iCloud Drive vs Dropbox
- SAP vs Oracle Cloud
- Cloud Computing vs Data Science
- Cloud Integration Platform
- Onedrive and iCloud
- Private Cloud and On-premise
- What is Cloudcraft
- Bitbucket Cloud API
- Akamai vs Cloudflare
- AWS CloudWatch vs Datadog
- Cloud Burst
- Cloudflare vs CloudFront
- Elastic Cloud on Azure
- Cloud Useful Resources
- Cloud Computing - Quick Guide
- Cloud Computing - Useful Resources
- Cloud Computing - Discussion
Cloud Computing Overview
Cloud Computing provides us means of accessing the applications as utilities over the Internet. It allows us to create, configure, and customize the applications online.
What is Cloud?
The termCloudrefers to aNetworkorInternet. In other words, we can say that Cloud is something, which is present at remote location. Cloud can provide services over public and private networks, i.e., WAN, LAN or VPN.
Applications such ase-mail, web conferencing, customer relationship management (CRM) execute on cloud.
What is Cloud Computing?
Cloud Computingrefers tomanipulating, configuring,andaccessingthe hardware and software resources remotely. It offers online data storage, infrastructure, and application.

Cloud computing offers platform independency, as the software is not required to be installed locally on the PC. Hence, the Cloud Computing is making our business applicationsmobileandcollaborative.
Basic Concepts
There are certain services and models working behind the scene making the cloud computing feasible and accessible to end users. Following are the working models for cloud computing:
- Deployment Models
- Service Models
Deployment Models
Deployment models define the type of access to the cloud, i.e., how the cloud is located? Cloud can have any of the four types of access: Public, Private, Hybrid, and Community.
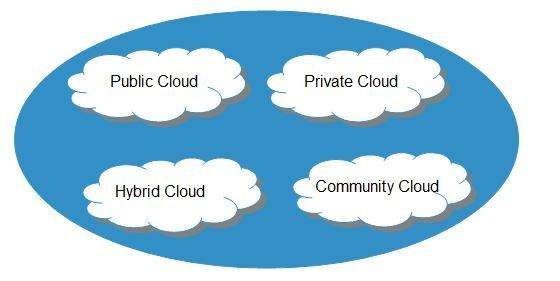
Public Cloud
Thepublic cloudallows systems and services to be easily accessible to the general public. Public cloud may be less secure because of its openness.
Private Cloud
Theprivate cloudallows systems and services to be accessible within an organization. It is more secured because of its private nature.
Community Cloud
Thecommunity cloudallows systems and services to be accessible by a group of organizations.
Hybrid Cloud
Thehybrid cloudis a mixture of public and private cloud, in which the critical activities are performed using private cloud while the non-critical activities are performed using public cloud.
Service Models
Cloud computing is based on service models. These are categorized into three basic service models which are -
- Infrastructure-asa-Service (IaaS)
- Platform-as-a-Service (PaaS)
- Software-as-a-Service (SaaS)
Anything-as-a-Service (XaaS) is yet another service model, which includes Network-as-a-Service, Business-as-a-Service, Identity-as-a-Service, Database-as-a-ServiceorStrategy-as-a-Service.
TheInfrastructure-as-a-Service (IaaS)is the most basic level of service. Each of the service models inherit the security and management mechanism from the underlying model, as shown in the following diagram:
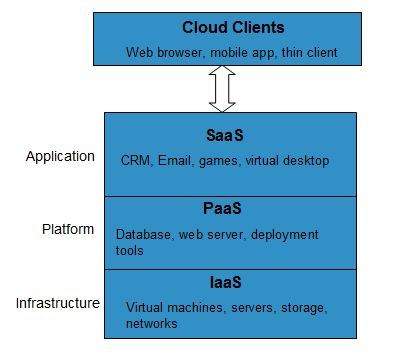
Infrastructure-as-a-Service (IaaS)
IaaSprovides access to fundamental resources such as physical machines, virtual machines, virtual storage, etc.
Platform-as-a-Service (PaaS)
PaaS provides the runtime environment for applications, development and deployment tools, etc.
Software-as-a-Service (SaaS)
SaaSmodel allows to use software applications as a service to end-users.
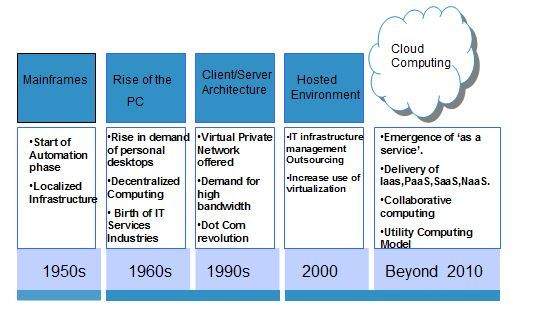
History of Cloud Computing
The concept ofCloud Computingcame into existence in the year 1950 with implementation of mainframe computers, accessible viathin/static clients. Since then, cloud computing has been evolved from static clients to dynamic ones and from software to services. The following diagram explains the evolution of cloud computing:
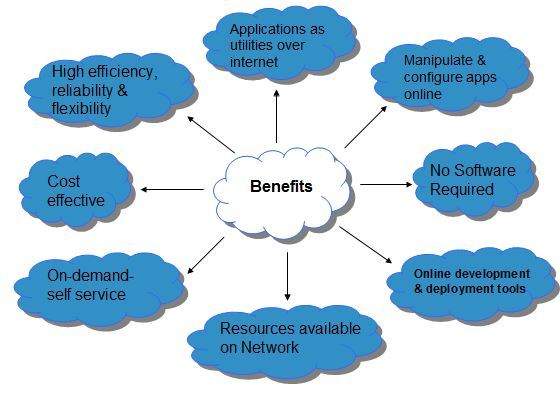
Benefits
Cloud Computing has numerous advantages. Some of them are listed below -
One can access applications as utilities, over the Internet.
One can manipulate and configure the applications online at any time.
It does not require to install a software to access or manipulate cloud application.
Cloud Computing offers online development and deployment tools, programming runtime environment throughPaaS model.
Cloud resources are available over the network in a manner that provide platform independent access to any type of clients.
Cloud Computing offerson-demand self-service. The resources can be used without interaction with cloud service provider.
Cloud Computing is highly cost effective because it operates at high efficiency with optimum utilization. It just requires an Internet connection
Cloud Computing offers load balancing that makes it more reliable.
Risks related to Cloud Computing
Although cloud Computing is a promising innovation with various benefits in the world of computing, it comes with risks. Some of them are discussed below:
Security and Privacy
It is the biggest concern about cloud computing. Since data management and infrastructure management in cloud is provided by third-party, it is always a risk to handover the sensitive information to cloud service providers.
Although the cloud computing vendors ensure highly secured password protected accounts, any sign of security breach may result in loss of customers and businesses.
Lock In
It is very difficult for the customers to switch from oneCloud Service Provider (CSP)to another. It results in dependency on a particular CSP for service.
Isolation Failure
This risk involves the failure of isolation mechanism that separates storage, memory, and routing between the different tenants.
Management Interface Compromise
In case of public cloud provider, the customer management interfaces are accessible through the Internet.
Insecure or Incomplete Data Deletion
It is possible that the data requested for deletion may not get deleted. It happens because either of the following reasons
Extra copies of data are stored but are not available at the time of deletion
Disk that stores data of multiple tenants is destroyed.
Characteristics of Cloud Computing
There are four key characteristics of cloud computing. They are shown in the following diagram:
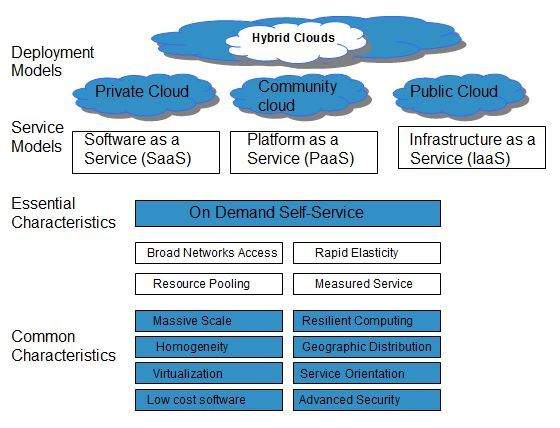
On Demand Self Service
Cloud Computing allows the users to use web services and resources on demand. One can logon to a website at any time and use them.
Broad Network Access
Since cloud computing is completely web based, it can be accessed from anywhere and at any time.
Resource Pooling
Cloud computing allows multiple tenants to share a pool of resources. One can share single physical instance of hardware, database and basic infrastructure.
Rapid Elasticity
It is very easy to scale the resources vertically or horizontally at any time. Scaling of resources means the ability of resources to deal with increasing or decreasing demand.
The resources being used by customers at any given point of time are automatically monitored.
Measured Service
In this service cloud provider controls and monitors all the aspects of cloud service. Resource optimization, billing, and capacity planning etc. depend on it.
