
- CICS - Home
- CICS - Overview
- CICS - Environment
- CICS - Basic Terms
- CICS - Nucleus
- CICS - Transactions
- CICS - COBOL Basics
- CICS - BMS
- CICS - MAP
- CICS - Interface Block
- CICS - Pseudo Programming
- CICS - Aid Keys
- CICS - File Handling
- CICS - Error Handling
- CICS - Control Operations
- CICS - Temporary Storage
- CICS - Intercommunication
- CICS - Status Codes
- CICS - Interview Questions
CICS - Transactions
CICS transactions are used to perform multiple operations in the CICS region. We will be discussing the important CICS transactions supplied by IBM in detail.
CESN
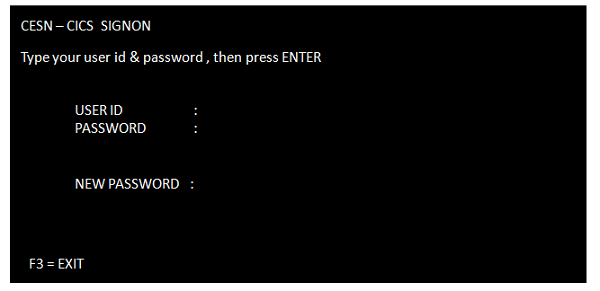
CESN is known as CICS Execute Sign On.
CESN is used to Sign on to the CICS region.
We need to provide the User-Id and Password given by the CICS administrator to log on to CICS. The following screenshot shows how the sign-on screen looks like −
CEDA
CEDA is known as CICS Execute Definition and Administration. It is used by CICS System Administrators to define CICS table entries and other administration activities.
CEMT
CEMT is known as CICS Execute Master Terminal. It is used to inquire and update the status of CICS environments and also for other system operations.
Using CEMT command, we can manage transactions, tasks, files, programs, etc.
To get all the possible options, type CEMT and press ENTER. It will display all the options.
CEMT is basically used for loading a new program into the CICS or for loading a new copy of the program into the CICS after the program or mapset is changed.
Example
One can overwrite the status of the file displayed to change it. Following example shows how to close a file −
CEMT ** Press ENTER & Following Screen is displayed ** STATUS: ENTER ONE OF THE FOLLOWING Inquire Perform Set ** Command to close a file ** CEMT SET FILE (file-name) CEMT I FILE (file-name)
CECI
CECI is known as CICS Execute Command Interpreter. Many CICS commands can be executed using CECI.
CECI is used to check the syntax of the command. It executes the command, only if the syntax is correct.
Type the CECI option on the empty CICS screen after having logged in. It gives you the list of options available.
Example
Following example shows how to send mapped output data to terminal. We will be discussing about MAPS in the upcoming modules.
CECI SEND MAP (map-name) MAPSET (mapset-name) ERASE
CEDF
CEDF is known as CICS Execute Debug Facility. It is used for debugging the program step by step, which helps in finding the errors.
Type CEDF and press enter in the CICS region. The terminal is in EDF mode message will be displayed. Now type the transaction id and press the enter key. After initiation, with each enter key, a line is executed. Before executing any CICS command, it shows the screen in which we can modify the values before proceeding further.
CMAC
CMAC is known as CICS Messages for Abend Codes. It is used to find the explanation and reasons for CICS Abend Codes.
Example
Following example shows how to check details for an Abend code −
CMAC abend-code
CESF
CESF is known as CICS Execute Sign Off. It is used to Sign Off from the CICS region.
Example
Following example shows how to log off from the CICS region −
CESF LOGOFF
CEBR
CEBR is known as CICS Execute Temporary storage Browse. It is used to display contents of a temporary storage queue or TSQ.
CEBR is used while debugging to check if the items of the queue are being written and retrieved properly. We will discuss more about TSQ in the upcoming modules.
Example
Following example shows how to invoke the CEBR command −
CEBR queue-id
CICS Concepts
Each command could be achieved by executing a series of CICS macros. We will discuss some basic features which will help us understand the concepts better −
Multitasking
This feature of operating system allows more than one task to be executed concurrently. The task may be sharing the same program or using different programs. The CICS schedules the task in its own region.
Multi-threading
This feature of the operating system allows more than one task to be executed concurrently sharing the same program. For multi-threading to be possible, an application program should be a re-entrant program under the operating system or a quasi-reentrant under the CICS.
Re-entrancy
A re-entrant program is one which does not modify itself and can re-enter in itself and continue processing after an interruption by the operating system.
Quasi-reentrancy
A quasi-reentrant program is a re-entrant program under CICS environment. CICS ensures re-entrancy by acquiring a unique storage area for each task. Between CICS commands, the CICS has the exclusive right to use the CPU resources and it can execute other CICS commands of other tasks.
There are times when many users are concurrently using the same program; this is what we call multi-threading. For example, lets suppose 50 users are using a program A. Here the CICS will provide 50 working storage for that program but one Procedure Division. And this technique is known as quasi-reentrancy.
