
- Blockchain - Home
- Blockchain - Introduction
- History of Blockchain
- Blockchain - Technology
- Blockchain and Cryptography
- Blockchain Beyond Crypto
- Blockchain - Advanced Concepts
- Blockchain - Decentralization
- Blockchain - D-Apps
- Blockchain - DeFi
- Blockchain - Future Scope
- Smart Contracts in Blockchain
- Blockchain - Ricardian Contracts
- Blockchain - Oracles
- Blockchain - DAO
- Bitcoin
- Bitcoin - Invisible Gold
- How Bitcoin Works?
- Bitcoin - Network
- Bitcoin - Wallets
- Bitcoin - Innovations
- Ethereum
- Ethereum Alternate Cryptocurrency
- Ethereum Ecosystem
- Ethereum Virtual Machine
- Advanced Ethereum
- Ethereum Wallets
- Ethereum Miner Nodes
- Miscellaneous
- Blockchain - Double Spending
- Public Key Cryptography
- Blockchain - Hashing
- Bitcoin - Mining
- Blockchain - Chaining Blocks
- Blockchain - Proof of Work
- Blockchain - Network & Mining
- Blockchain - Incentives to Miners
- Blockchain - Merkle Tree
- Blockchain - Payment Verification
- Blockchain - Resolving Conflicts
- Blockchain - Privacy
- Bitcoin - Mitigating Attacks
- Blockchain - Conclusion
Bitcoin - Mining
When Bob creates a purchase request for Lisa, he does not send it to Lisa alone. Rather the request message is broadcasted on the entire network to which he is connected. Bobs network is depicted in image.
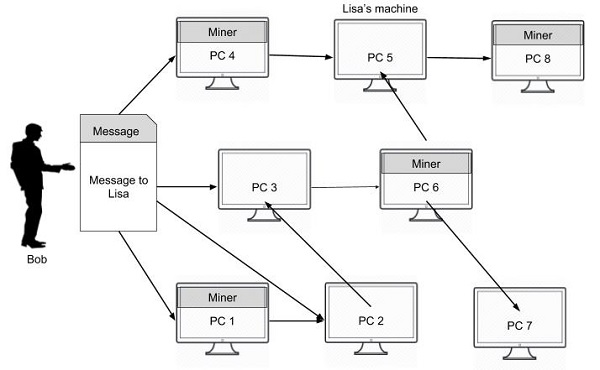
The message goes to all the connected nodes (machines). Some of the nodes in the diagram are marked as miners. These are the machines which run a piece of software for mining the bitcoin message. I will now explain you what this mining means.
Mining Process
As the entire network is widely distributed, every miner in the network is expected to receive multiple messages from multiple vendors at any given period of time. What the miner does is he combines these messages in a single block. This is illustrated in image −
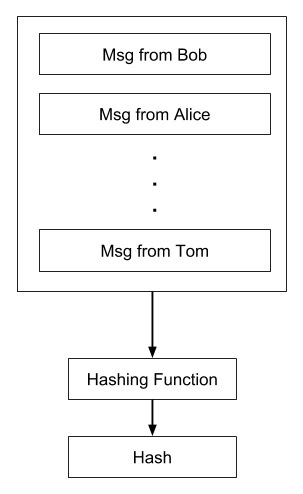
After a block of messages is formed, the miner creates a hash on the block using the hashing function described earlier. Now, as you know if any third party modifies the contents of this block, its hash would become invalid. Incidentally, each message is time-stamped so that nobody can modify its chronological order without affecting the blocks hash value. Thus, the messages in the block are perfectly secured from tampering. How this fact is used in securing all the transactions in the network is explained further.
