
- Cryptography Tutorial
- Cryptography - Home
- Cryptography - Origin
- Cryptography - History
- Cryptography - Principles
- Cryptography - Applications
- Cryptography - Benefits & Drawbacks
- Cryptography - Modern Age
- Cryptography - Traditional Ciphers
- Cryptography - Need for Encryption
- Cryptography - Double Strength Encryption
- Cryptosystems
- Cryptosystems
- Cryptosystems - Components
- Attacks On Cryptosystem
- Cryptosystems - Rainbow table attack
- Cryptosystems - Dictionary attack
- Cryptosystems - Brute force attack
- Cryptosystems - Cryptanalysis Techniques
- Types of Cryptography
- Cryptosystems - Types
- Public Key Encryption
- Modern Symmetric Key Encryption
- Cryptography Hash functions
- Key Management
- Cryptosystems - Key Generation
- Cryptosystems - Key Storage
- Cryptosystems - Key Distribution
- Cryptosystems - Key Revocation
- Block Ciphers
- Cryptosystems - Stream Cipher
- Cryptography - Block Cipher
- Cryptography - Feistel Block Cipher
- Block Cipher Modes of Operation
- Electronic Code Book (ECB) Mode
- Cipher Block Chaining (CBC) Mode
- Cipher Feedback (CFB) Mode
- Output Feedback (OFB) Mode
- Counter (CTR) Mode
- Classic Ciphers
- Cryptography - Reverse Cipher
- Cryptography - Caesar Cipher
- Cryptography - ROT13 Algorithm
- Cryptography - Transposition Cipher
- Cryptography - Encryption Transposition Cipher
- Cryptography - Decryption Transposition Cipher
- Cryptography - Multiplicative Cipher
- Cryptography - Affine Ciphers
- Cryptography - Simple Substitution Cipher
- Cryptography - Encryption of Simple Substitution Cipher
- Cryptography - Decryption of Simple Substitution Cipher
- Cryptography - Vigenere Cipher
- Cryptography - Implementing Vigenere Cipher
- Modern Ciphers
- Base64 Encoding & Decoding
- Cryptography - XOR Encryption
- Substitution techniques
- Cryptography - MonoAlphabetic Cipher
- Cryptography - Hacking Monoalphabetic Cipher
- Cryptography - Polyalphabetic Cipher
- Cryptography - Playfair Cipher
- Cryptography - Hill Cipher
- Polyalphabetic Ciphers
- Cryptography - One-Time Pad Cipher
- Implementation of One Time Pad Cipher
- Cryptography - Transposition Techniques
- Cryptography - Rail Fence Cipher
- Symmetric Algorithms
- Data Encryption Standard
- Triple DES
- Advanced Encryption Standard
- Data Integrity in Cryptography
- Data Integrity in Cryptography
- Message Authentication
- Cryptography Digital signatures
- Public Key Infrastructure
- Cryptography Useful Resources
- Cryptography - Quick Guide
- Cryptography - Discussion
Cryptography - Output Feedback (OFB) Mode
The Output Feedback (OFB) Mode is similar to the Cipher Feedback mode, but it delivers encrypted output instead of the XOR output. This output feedback option sends all block bits rather than just a subset of them. The output feedback mode of block cipher is extremely vulnerable to bit transmission errors. This reduces the dependecy of cipher's need on plaintext.
It involves inserting the successive output blocks from the underlying block cipher back into it. In CFB mode, feedback blocks send a string of bits to the encryption algorithm, which then generates the key-stream.
The OFB mode needs an IV as the first random n-bit input block. The Initialization Vector does not need to be kept secret. The operation of OFB mode is shown in the below image −
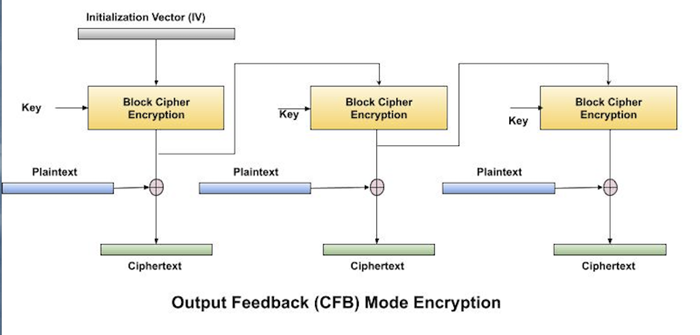
Operation
The fundamental difference between OFB and CFB is that the OFB mode uses XOR to combine plaintext and ciphertext blocks with larger copies of the initialization vector.
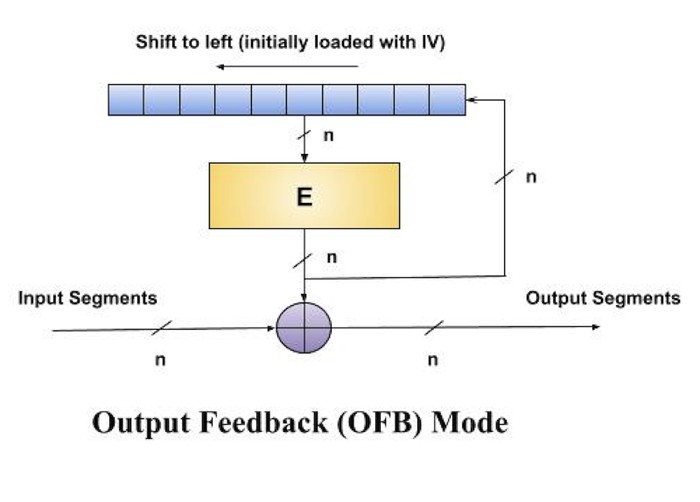
This operation can be considered as a one-time pad, and the expanded vectors as pad vectors. The formula below shows how a series of pad vectors is created −
Vi = EK(Vi-1)
where EK represents the block encryption technique with key K, and Vi and Vi-1 are adjacent vectors.
Note that the calculation above assumes V0 to be the initialization vector.
After creating a series of pad vectors, the following formula can be used to execute encryption in the OFB mode −
Ci = Vi ⊕ Bi
Decryption works in a similar way −
Bi = Vi ⊕ Ci
Note that, like the CFB mode, OFB uses the same encryption algorithm for both encryption and decryption.
Analysis of OFB Mode
OFB mode gives high security, successful parallel processing, and tolerance for block loss. To avoid any security issues, care must be taken to ensure that the initialization vector is random and unique. Also, the lack of error propagation can call for more precautions to protect data integrity in the case of transmission problems.
Bit-Width of OFB Mode
The following table show the bit-width of the interfaces that OFB mode offer −
| plaintext | ciphertext | cipherkey | IV | |
|---|---|---|---|---|
| OFB-DES | 64 | 64 | 64 | 64 |
| OFB-AES128 | 128 | 128 | 128 | 128 |
| OFB-AES192 | 128 | 128 | 192 | 128 |
| OFB-AES256 | 128 | 128 | 256 | 128 |
Advantages of CFB Mode
Once the pad vectors (also known as keystream) have been created, the OFB (Output Feedback) mode enables for block encryption and decryption in simultaneously. This can lead to improved performance in situations where processing speed is important, as numerous blocks can be handled concurrently.
As each block is encrypted independently of the others, OFB mode can withstand the loss of encrypted blocks during transmission. This means that if a block is lost or corrupted, succeeding blocks' decryption will be unaffected, allowing for better error recovery.
Disadvantages of OFB Mode
Repeatedly encrypting the initialization vector (IV) in OFB mode can generate the same state, possibly revealing a security vulnerability. If the IV is not properly random or changes predictably, the encryption process can reuse the same keystream, allowing an attacker information about the plaintext.
Unlike other modes, like CBC (Cipher Block Chaining), OFB mode does not transmit errors. While this can be beneficial in some cases since it prevents errors from affecting succeeding blocks, it also means that problems in the ciphertext may not be recognised or fixed, potentially leading to data damage or security vulnerabilities.
To Continue Learning Please Login