
- OAuth 2.0 - Home
- OAuth 2.0 - Overview
- OAuth 2.0 - Architecture
- OAuth 2.0 - Client Credentials
- Obtaining an Access Token
- Accessing a Protected Resource
- OAuth 2.0 - Extensibility
- OAuth 2.0 - IANA Considerations
- OAuth 2.0 Useful Resources
- OAuth 2.0 - Quick Guide
- OAuth 2.0 - Useful Resources
- OAuth 2.0 - Discussion
OAuth 2.0 - Refresh Token
Refresh tokens are the credentials that can be used to acquire new access tokens.
The lifetime of a refresh token is much longer compared to the lifetime of an access token.
Refresh tokens can also expire but are quiet long-lived.
When current access tokens expire or become invalid, the authorization server provides refresh tokens to the client to obtain new access token.
The following figure illustrates the process of refreshing an expired Access Token.
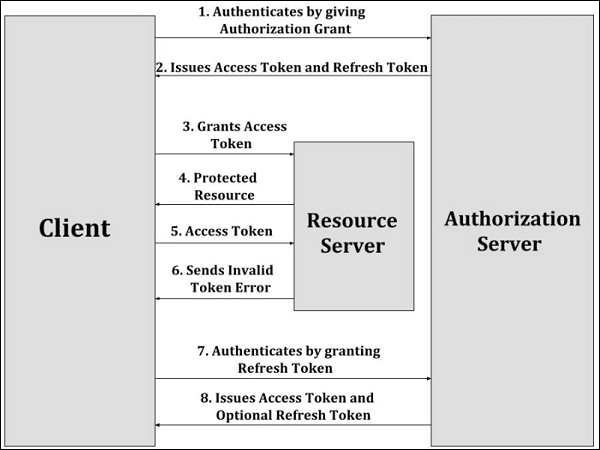
Step 1 − First, the client authenticates with the authorization server by giving the authorization grant.
Step 2 − Next, the authorization server authenticates the client, validates the authorization grant and issues the access token and refresh token to the client, if valid.
Step 3 − Then, the client requests the resource server for protected resource by giving the access token.
Step 4 − The resource server validates the access token and provides the protected resource.
Step 5 − The client makes the protected resource request to the resource server by granting the access token, where the resource server validates it and serves the request, if valid. This step keeps on repeating until the access token expires.
Step 6 − If the access token expires, the client authenticates with the authorization server and requests for new access token by providing refresh token. If the access token is invalid, the resource server sends back the invalid token error response to the client.
Step 7 − The client authenticates with the authorization server by granting the refresh token.
Step 8 − The authorization server then validates the refresh token by authenticating the client and issues a new access token, if it is valid.
