
- Internet Security Tutorial
- Internet Security - Home
- Internet Security - Overview
- Internet Security - Cookies
- Internet Security - Phishing
- Internet Security - Social Network
- Internet Security - Chrome
- Internet Security - Mozilla
- Internet Security - Explorer
- Internet Security - Safari
- Internet Security - Gaming
- Internet Security - Child Safety
- Internet Security - Spamming
- Internet Security - Chatting
- Internet Security - File Download
- Internet Security - Transactions
- Internet Security - Banking
- Internet Security - e-Commerce
- Internet Security - Certificates
- Internet Security - Email Security
- Internet Security - Identity Theft
- Internet Security - Cybercrime
- Internet Security - Laws
- Internet Security - Checklist
- Internet Security Useful Resources
- Internet Security - Quick Guide
- Internet Security - Useful Resources
- Internet Security - Discussion
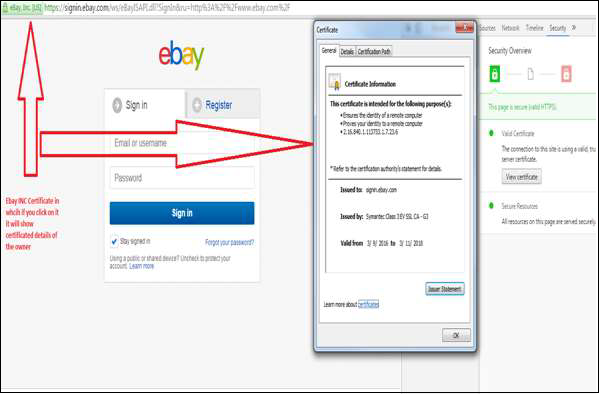
Internet Security - Certificates
Digital Certificates are a standard of security for establishing an encrypted link between a server and a client. Generally, between a mail server or a webserver, which protects data in transitions by encrypting them. A Digital Certificate is also a Digital ID or a passport which is issued by a Third Party Authority which verifies the identity of the server’s owner and not claiming a false identity.
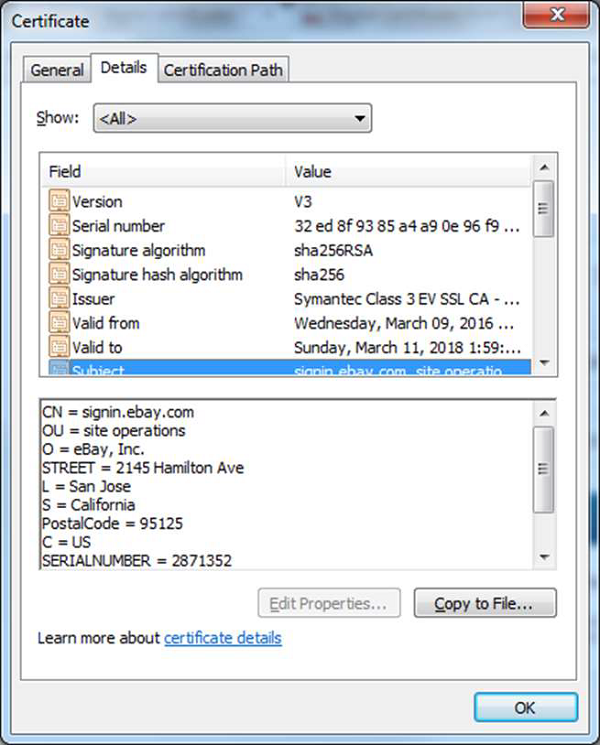
Components of a Digital Certificate
All these following components can be found in the certificate details −
Serial Number − Used to uniquely identify the certificate.
Subject − The person, or entity identified.
Signature Algorithm − The algorithm used to create the signature.
Signature − The actual signature to verify that it came from the issuer.
Issuer − The entity that verified the information and issued the certificate.
Valid-From − The date the certificate is first valid from.
Valid-To − The expiration date.
Key-Usage − Purpose of the public key (For example: encipherment, signature, certificate signing...).
Public Key − The public key.
Thumbprint Algorithm − The algorithm used to hash the public key certificate.
Thumbprint − The hash itself, used as an abbreviated form of the public key certificate.
Levels of Validations
In this section we will discuss the various levels of validations of an SSL (Secure Sockets Layer) Certificate. Some of the most important ones are as follows −
Domain Validation SSL Certificate − It validates the domain that is registered by a system administrators and they have administrator rights to approve the certificate request, this validation generally is done by email request or by a DNS record.
Organization Validated SSL Certificates − It validates the domain ownership and also the business information like the Official Name, City, Country, etc. This validation is done by email or DNS record entering and the certificate authority would also need some genuine documents to verify the Identity.
Extended Validation SSL Certificates − It validates domain ownership and organization information, plus the legal existence of the organization. It also validates that the organization is aware of the SSL certificate request and approves it. The validation requires documentation to certify the company identity plus a set of additional steps and checks. The Extended Validation SSL Certificates are generally identified with a green address bar in the browser containing the company name.
The reviews and some of the biggest digital certificate providers’ details can be found in the following link − https://www.sslshopper.com/certificate-authority-reviews.html